Google Stored G Suite Passwords in Plaintext Since 2005
Threatpost
MAY 22, 2019
Google said it had stored G Suite enterprise users' passwords in plain text since 2005 marking a giant security faux pas.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Threatpost
MAY 22, 2019
Google said it had stored G Suite enterprise users' passwords in plain text since 2005 marking a giant security faux pas.

Adam Levin
MAY 24, 2019
Google announced a glitch that stored unencrypted passwords belonging to several business customers, a situation that had been exploitable since 2005. This issue has been fixed and, again, we have seen no evidence of improper access to or misuse of the affected passwords.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

WIRED Threat Level
MAY 21, 2019
On the heels of embarrassing disclosures from Facebook and Twitter, Google reveals its own password bugs—one of which lasted 14 years.

Dark Reading
JANUARY 25, 2023
Zacks Elite sign-ups for the period 1999–2005 were accessed, including name, address, email address, phone number, and the password associated with Zacks.com.

Schneier on Security
DECEMBER 14, 2018
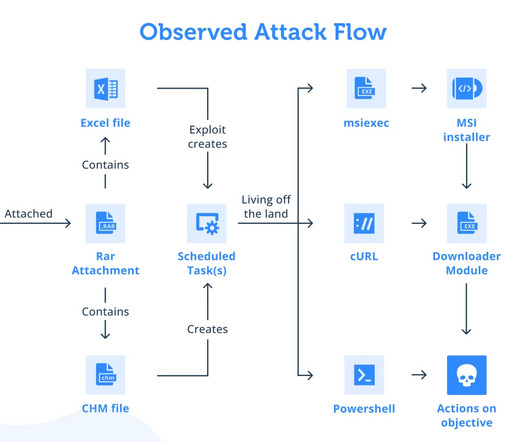
When targets entered passwords into a fake Gmail or Yahoo security page, the attackers would almost simultaneously enter the credentials into a real login page. In the event targets' accounts were protected by 2fa, the attackers redirected targets to a new page that requested a one-time password. This isn't new.

Malwarebytes
JANUARY 12, 2024
is an open-source CMS that’s been around since 2005, and has been one of the most popular CMS platforms by market share for much of that time. Super User’s password. Many companies, from small outfits to large enterprises, use a CMS in some form to manage their websites. versions 4.0.0-4.2.7. or later.

Security Affairs
MAY 22, 2019
Google accidentally stored the passwords of its G Suite users in plain-text for 14 years allowing its employees to access them. The news is disconcerting, Google has accidentally stored the passwords of the G Suite users in plain-text for 14 years, this means that every employee in the company was able to access them.

Security Affairs
JUNE 13, 2023
According to HIBP, the records in the database contain names, addresses, phone numbers, email addresses, usernames, and passwords stored as unsalted SHA-256 hashes. The company attempted to downplay the security breach by telling Have I Been Pwned that threat actors only had access to encrypted passwords. ” reported HIBP.

Krebs on Security
MAY 4, 2023
Launched in 2005, Try2Check soon was processing more than a million card-checking transactions per month — charging 20 cents per transaction. ” In February 2005, Nordex posted to Mazafaka that he was in the market for hacked bank accounts, and offered 50 percent of the take. Denis Kulkov, a.k.a. Image: USDOJ.
Krebs on Security
JUNE 28, 2022
In a typical PPI network, clients will submit their malware—a spambot or password-stealing Trojan, for example —to the service, which in turn charges per thousand successful installations, with the price depending on the requested geographic location of the desired victims. AWM Proxy’s online storefront disappeared that same day.

Krebs on Security
JANUARY 8, 2024
From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a Collectively in control over millions of spam-spewing zombies, those botmasters also continuously harvested passwords and other data from infected machines. w s, icamis[.]ru ru , and icamis[.]biz.

Security Affairs
JANUARY 25, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. Exposed customers’ data may include name, address, phone number, email address, and password used for Zacks.com. ” concludes the notice.
Krebs on Security
JUNE 1, 2023
.” Constella Intelligence , a company that tracks exposed databases, finds that 774748@gmail.com was used in connection with just a handful of passwords, but most frequently the password “ featar24 “ Pivoting off of that password reveals a handful of email addresses, including akafitis@gmail.com. ru in 2008.

CyberSecurity Insiders
AUGUST 11, 2021
A survey conducted by Gartner in 2019 said that 88% of companies operating worldwide were hit by a cyber attack and out of those, 51% of them experienced the incident for password steal. Only 5 percent of the total data and virtual files stored across the world are secure and so the Cybersecurity business is said to reach a valuation of $170.3

Security Affairs
APRIL 19, 2020
.” Webkinz were originally released by the Canadian toy company Ganz on April 29, 2005. A hacker has leaked the usernames and passwords of nearly 23 million players of Webkinz World on a well-known hacking forum. . ” reported ZDNet. Famous nostalgic game, Webkinz, got hacked and database leaked.
Krebs on Security
SEPTEMBER 1, 2021
An ad circa 2005 for A311 Death, a powerful banking trojan authored by “Corpse,” the administrator of the early Russian hacking clique Prodexteam. Image: Google Translate via Archive.org. Corpse/Revive also long operated an extremely popular service called check2ip[.]com

The Last Watchdog
JUNE 23, 2021
In fact, PAM technology came on the scene around 2005, as a subset of identity access and management (IAM) systems. At a very basic level PAM does this by implementing multi-factor authentication and proactively managing passwords for privileged users and for the users of shared privileged accounts. Password concierge.

Security Affairs
SEPTEMBER 3, 2019
XKCD is one of the most popular webcomic platform created by the American author Randall Munroe in 2005, it is a webcomic of romance, sarcasm, math, and language. The phpBB forum exposed email and IP addresses, usernames and passwords stored in MD5 phpBB3 format. XKCD has suffered a data breach that exposed data of its forum users.
Security Affairs
MARCH 28, 2023
million records dating back to at least 2005 were also compromised in the data breach. We will never contact customers requesting their passwords.” .” The company announced that it will reimburse those customers who choose to replace their stolen ID documents. The statement also reported that approximately 6.1

Malwarebytes
JANUARY 16, 2024
As a member of the club, he competed in a local programming competition, helping the team to win in both 2005 and 2006. While at CWRU, he was accused of “cracking passwords” on a CWRU network. Despite this, he was active in extracurricular activities. In high school, he participated in a computer club.

Identity IQ
JANUARY 19, 2021
These records contained logs of conversations between Microsoft support and customers going back to 2005. The data was available to anyone on the web, unsecured with passwords or any other authentication requirements. The customer data included emails, birth dates, passwords, physical addresses, phone numbers and IP addresses.

Krebs on Security
JULY 25, 2023
Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed AVrecon that enslaves Internet routers into botnet that bilks online advertisers and performs password-spraying attacks. md , and that they were a systems administrator for sscompany[.]net. form [sic] hackers on public networks.”

Herjavec Group
NOVEMBER 16, 2020
When this trend started back in 2005, people preferred to shop while they were at the office, using fast computers and high-speed connections. Even amateur hackers can snoop on public Wi-Fi and pick up your email and other account login IDs and passwords. Change all of your passwords. But why Cyber Monday and not Saturday?

Anton on Security
JUNE 10, 2022
There are people moving to “next-gen” firewalls (a great innovation of 2005) in 2022. A password manager claimed “zero trust for passwords” while a SIEM/UEBA vendor promised to reveal all zero trust secrets (I bet they use VPN internally…). There are people buying their first SIEM in 2022.

Security Affairs
AUGUST 1, 2018
The hacker accessed user data, email addresses, and a 2007 backup database containing hashed passwords managed by the platform. “A hacker broke into a few of Reddit’s systems and managed to access some user data, including some current email addresses and a 2007 database backup containing old salted and hashed passwords. .

SC Magazine
JUNE 25, 2021
A young woman plays on the Electronic Arts (EA) newest product “Sims2 – Nightlife” at a Computer Gaming Convention on August 18, 2005 in Leipzig, Germany. Photo by Andreas Rentz/Getty Images). The post Attacks against game companies are up.

Security Boulevard
JUNE 10, 2022
There are people moving to “next-gen” firewalls (a great innovation of 2005) in 2022. A password manager claimed “zero trust for passwords” while a SIEM/UEBA vendor promised to reveal all zero trust secrets (I bet they use VPN internally…). There are people buying their first SIEM in 2022.

Malwarebytes
OCTOBER 4, 2021
Cybersecurity Awareness Month is a fixture of the calendar now, as are Data Privacy Day, World Password Day, and a host of other well-intentioned privacy and security themed events. I’ve been involved with events like this since 2005, and one time at a panel with reps from the FTC and the NYAG…. The questions is, is anybody listening?
Krebs on Security
MAY 2, 2023
Ditto for a case the FTC brought in 2005. Constella reports that for roughly a year between 2021 and 2022, a Microsoft Windows device regularly used by Mr. Mirza and his colleagues was actively uploading all of the device’s usernames, passwords and authentication cookies to cybercriminals based in Russia.

CyberSecurity Insiders
MAY 21, 2021
Furthermore, the number of regular telecommuting employees has grown by 173% since 2005. Hence apart from just using simple passwords, users are prompted to present additional information such as biometric readings or another connected device verification to in order to be granted access.

SiteLock
AUGUST 27, 2021
As you can see in the chart below from Statista, data breaches rose more than tenfold between 2005 and 2017. You are often required to provide your email address, date of birth, first and last name, and a password. Now think about the type of data you enter when you create a new account on a website. How do databases get compromised?

The Last Watchdog
JANUARY 30, 2019
Turn the corner into 2019 and we find Citigroup, CapitalOne, Wells Fargo and HSBC Life Insurance among a host of firms hitting the crisis button after their customers’ records turned up on a database of some 24 million financial and banking documents found parked on an Internet-accessible server — without so much as password protection.

Security Boulevard
APRIL 28, 2021
Networks can also be easily breached by social engineering, password theft, or tainted USBs, as in the Stuxnet attack. . . Estimated to have been around since 2005, Kaspersky Lab discovered Stuxnet in 2010. Now decades later, these complex systems are running on legacy software and operating systems.
Security Affairs
APRIL 28, 2020
Shellbot is known since 2005 and even available on GitHub. We suggest to harden and update your SSH server configuring authentication with authorized keys and disabling passwords. This means that, most probably, the gang will deploy a new IRC server leaving the rest of the infrastructure untouched.
eSecurity Planet
MARCH 26, 2022
In 2005, the open standard consortium OASIS released SAML 2.0 These communications on the backend of username and password login processes ensure users get authenticated by the overarching identity manager and authorized to use the given web service(s). In 2005, OASIS released 2.0, to broad appeal. A year later, SAML 1.0

ForAllSecure
DECEMBER 2, 2021
It was for UNIX systems and it was created by Dan Farmer and Wheat-say Vene-ma, who then co-authored a book in 2005 called Forensic Discovery. So eventually, we can figure out better ways of accessing the infrastructure versus just a regular RDP, which is prone to the password spray, like, right.

eSecurity Planet
DECEMBER 3, 2021
Normally account take overs are due to insecure passwords or recovery options, this is definitely something different. Once a penetration tester, Paul Asadoorian has been the founder and CEO of Security Weekly and host of a weekly show since 2005. Enable 2FA and get a password manager. Eugene Kaspersky | @e_kaspersky.

eSecurity Planet
FEBRUARY 16, 2021
In 2005, Sony BMG delivered millions of CDs with a rootkit that monitored listening habits and unintentionally left a backdoor to the device for cybercriminals. Always change the default passwords for any IoT devices you install before extended use. Good password hygiene is one of the best ways to prevent access to keyloggers.

Cisco Security
MAY 26, 2022
In 2005, I was lucky enough to become a Senior Editor at Tom’s Hardware Guide and attended Black Hat as accredited press from 2005 to 2008. were applied, as well as a standard WPA2 SSID for the devices that the device vendor had set up (we gave them the name of the SSID and Password).

Elie
DECEMBER 20, 2018
reuse of passwords found in data breaches and phishing attacks. in 2005 and TOTP in. Performing a longitudinal analysis highlights that the adoption rate of 2FA (two-factor authentication) has been mostly stagnant over the last five years, despite the ever increasing number of accounts hijacked due to the. HOTP was standardized in the.

SecureList
APRIL 24, 2023
Some file stealers are backdoor variants and share the same code base. 0 No operation cmd|[command] Executes the specified command, and returns the result in the cmd key of the JSON response.

Herjavec Group
AUGUST 26, 2021
1962 — Allan Scherr — MIT sets up the first computer passwords, for student privacy and time limits. Student Allan Scherr makes a punch card to trick the computer into printing off all passwords and uses them to log in as other people after his time runs out. She connects him to any phone number he requests for free.

eSecurity Planet
APRIL 26, 2022
Notable cybersecurity exits for the company include Forescout, Imperva, Webroot, Tenable, and Crowdstrike; and Accel’s other successful investments include Atlassian, Cloudera, Etsy, and Meta. Accel Investments. Paladin Capital Group. Ten Eleven Ventures.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content