12 Data Loss Prevention Best Practices (+ Real Success Stories)
eSecurity Planet
APRIL 12, 2024
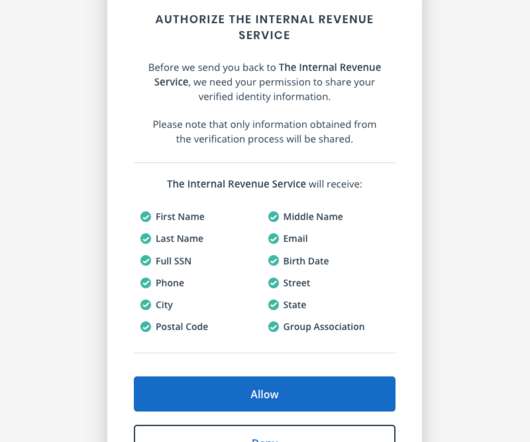
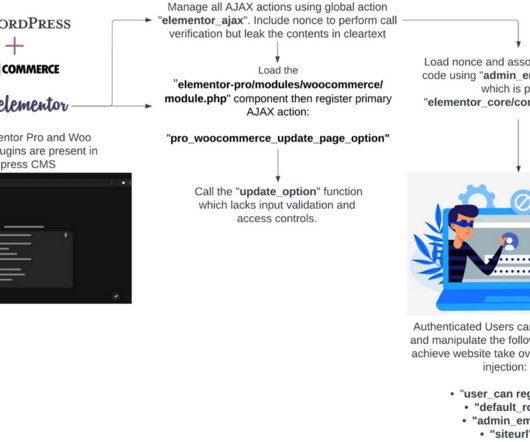
Employ Authentication Methods for All Users & Devices A zero trust approach rejects any sort of inherent trust and requires continual verification of all users and devices. Implement stringent access rules, multi-factor authentication, and continuous monitoring to authenticate all access attempts, regardless of prior trust status.










































Let's personalize your content