Encryption is on the Rise!
Cisco Security
JANUARY 18, 2023
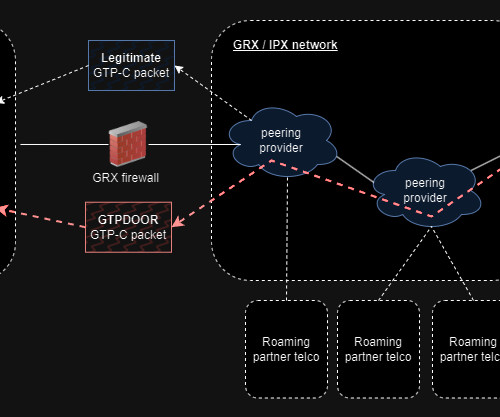
In the January 2019 report, EMA concluded: Some participants’ organizations may find they have to go back to the drawing board and come up with a Plan B to enable TLS 1.3 Technology improvements will increase rates of adoption over time, such as Cisco Secure Firewall’s ability to decrypt and inspect encrypted traffic.


































Let's personalize your content