Sophos fixed a critical vulnerability in Cyberoam firewalls
Security Affairs
OCTOBER 10, 2019
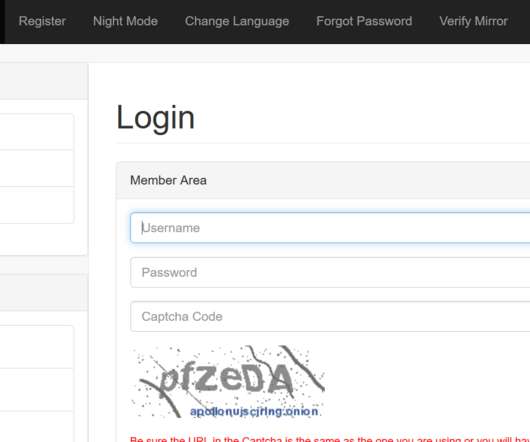
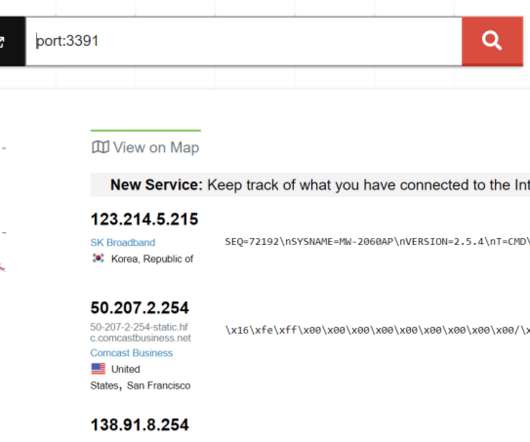
A vulnerability in Sophos Cyberoam firewalls could be exploited by an attacker to gain access to a target’s internal network without authentication. Sophos addressed a vulnerability in its Cyberoam firewalls that could be exploited by an attacker to gain access to a company’s internal network without providing a password.










































Let's personalize your content