Does Your Domain Have a Registry Lock?
Krebs on Security
JANUARY 24, 2020
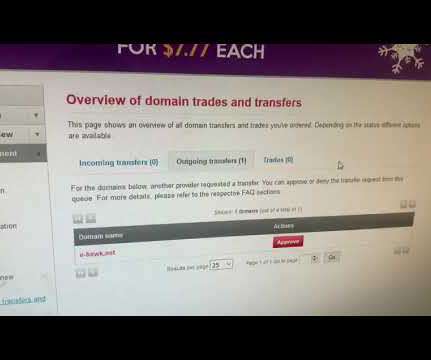
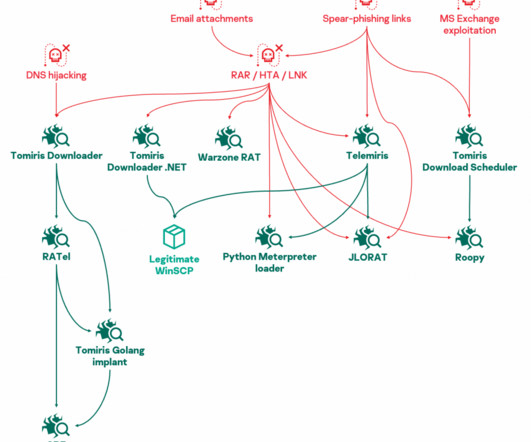
13, 2020, which was the date the fraudsters got around to changing the domain name system (DNS) settings for e-hawk.net. That alert was triggered by systems E-HAWK had previously built in-house that continually monitor their stable of domains for any DNS changes. Use DNSSEC (both signing zones and validating responses).































Let's personalize your content