Chinese Antivirus Firm Was Part of APT41 ‘Supply Chain’ Attack
Krebs on Security
SEPTEMBER 17, 2020
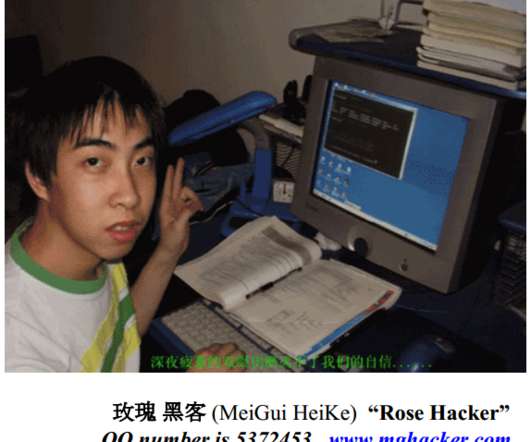
One of the alleged hackers was first profiled here in 2012 as the owner of a Chinese antivirus firm. ” Once inside of a target organization, the hackers stole source code, software code signing certificates, customer account data and other information they could use or resell. Image: FBI.











































Let's personalize your content