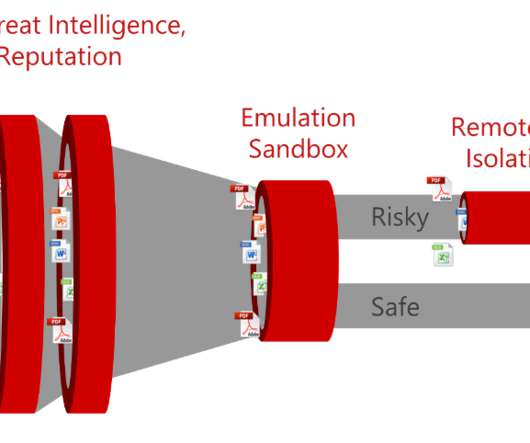
MY TAKE: Coping with security risks, compliance issues spun up by ‘digital transformation’
The Last Watchdog
AUGUST 22, 2019
Companies are being compelled to embrace digital transformation, or DX , if for no other reason than the fear of being left behind as competitors leverage microservices, containers and cloud infrastructure to spin-up software innovation at high velocity. The massive transformation that’s happening right now introduces a lot of risk.











































Let's personalize your content