Malvertising Is a Cybercrime Heavyweight, Not an Underdog
SecureWorld News
MARCH 29, 2024
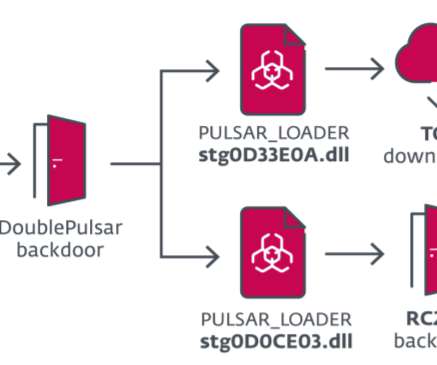
The concept of the term "malvertising" (a portmanteau of "malicious advertising") suggests an overlap with ads, albeit dodgy ones, and therefore fuels the fallacy that its impact hardly goes beyond frustration. Malvertising acts as a vessel for malware propagation. How does a malvertising attack unfold?



















Let's personalize your content