The Internet of Things Is Everywhere. Are You Secure?
Security Boulevard
MARCH 18, 2021
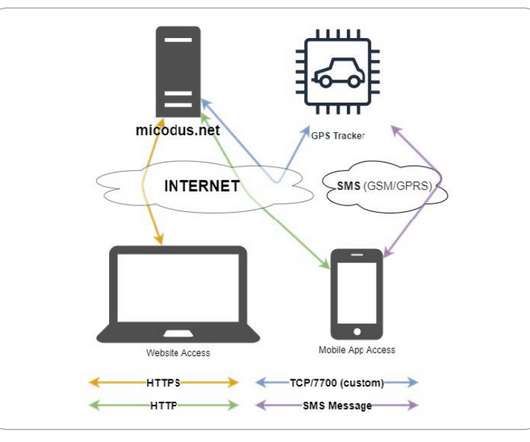
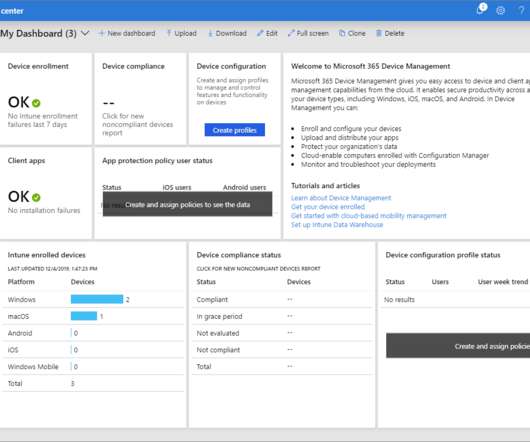
From smart homes that enable you to control your thermostat from a distance to sensors on oil rigs that help predict maintenance to autonomous vehicles to GPS sensors implanted in the horns of endangered black rhinos , the internet of things is all around you. A Safer Internet of Things. Source: DZone’s Edge Computing and IoT, 2020 .









































Let's personalize your content