NEW TECH: Silverfort helps companies carry out smarter human and machine authentications
The Last Watchdog
MAY 26, 2020
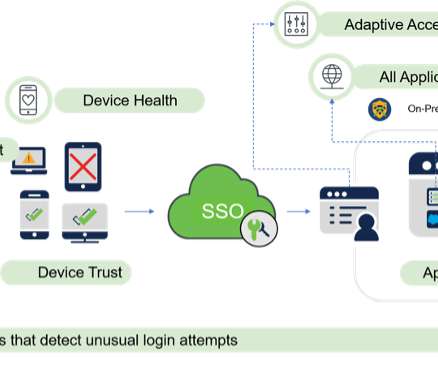
Doing authentication well is vital for any company in the throes of digital transformation. Related: Locking down ‘machine identities’ At the moment, companies are being confronted with a two-pronged friction challenge, when it comes to authentication. We spoke at RSA 2020. And that’s not an easy task.










































Let's personalize your content