LW ROUNDTABLE — How 2024’s cyber threats will transform the security landscape in 2025
The Last Watchdog
DECEMBER 16, 2024
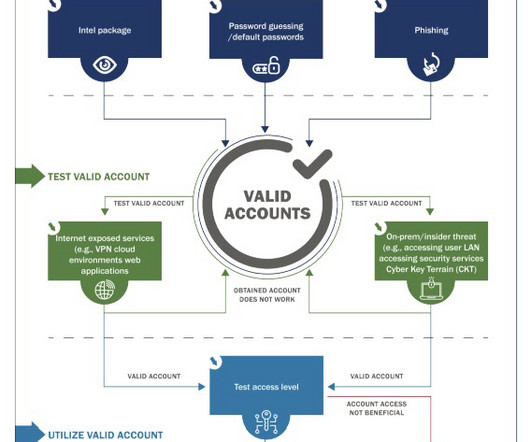
Complex DevSecOps, APIs, and cloud integrations will become leading attack vectors, while insider threats and accidental disclosures drive data leakage risks. With adversaries destroying backups to increase extortion payouts, recovery will grow harder and slower, emphasizing the need for stronger security controls and architecture.














































Let's personalize your content