NSA, CISA issue guidance on Protective DNS services
SC Magazine
MARCH 4, 2021
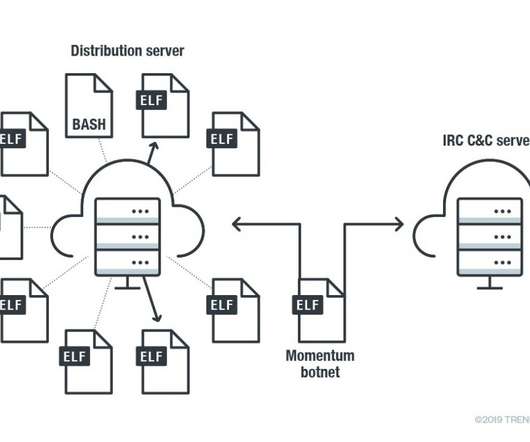
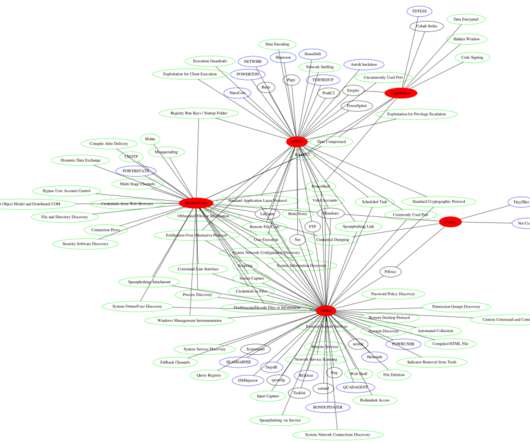
A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats. Over a six-month period, the PDNS service examined more than 4 billion DNS queries to and from the participating networks, blocking millions of connections to identified malicious domains.









































Let's personalize your content