Five Ways to Configure a SIEM for Accurate Threat Detection
eSecurity Planet
JUNE 6, 2023
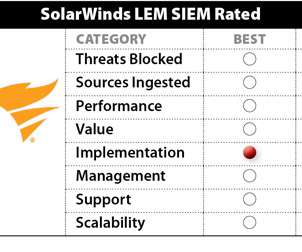
A security information and event management (SIEM) system is about as complicated as a security tool can get, pulling in log and threat data from a wide range of sources to look for signs of a cyber attack. Not surprisingly, they can be challenging to manage.











































Let's personalize your content