Overview of IoT threats in 2023
SecureList
SEPTEMBER 21, 2023
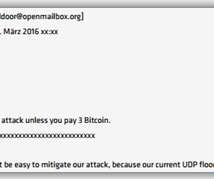
IoT devices (routers, cameras, NAS boxes, and smart home components) multiply every year. The first-ever large-scale malware attacks on IoT devices were recorded back in 2008, and their number has only been growing ever since. Telnet, the overwhelmingly popular unencrypted IoT text protocol, is the main target of brute-forcing.














































Let's personalize your content