Guardians of IoT: Addressing IoT security vulnerabilities in electric vehicles and charging stations
Security Boulevard
JANUARY 31, 2024
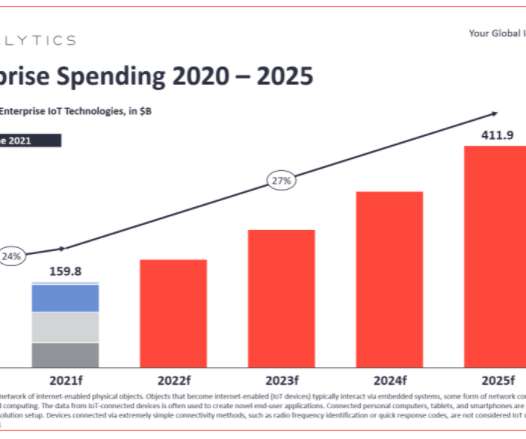
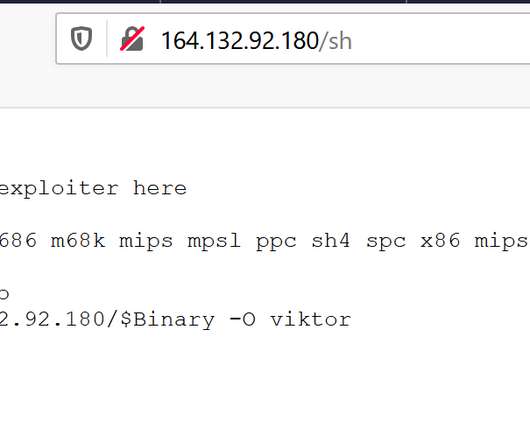
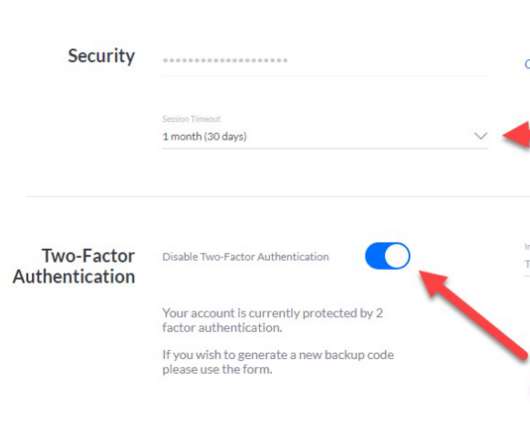
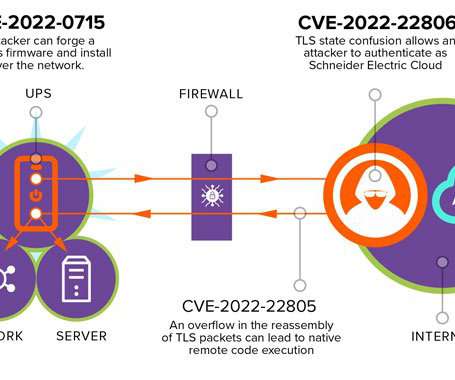
The rise of electric vehicles (EVs) and charging infrastructure necessitates robust security measures, especially in the context of IoT integration. Explore the vulnerabilities in EV systems and potential risks, proposing mitigation strategies like firmware updates, user authentication, intrusion detection systems, and collaboration.










































Let's personalize your content