The Clock To Q-Day Is Ticking: InfoSec Global and Thales Provide Collaborative Path to Quantum Readiness
Thales Cloud Protection & Licensing
FEBRUARY 19, 2024
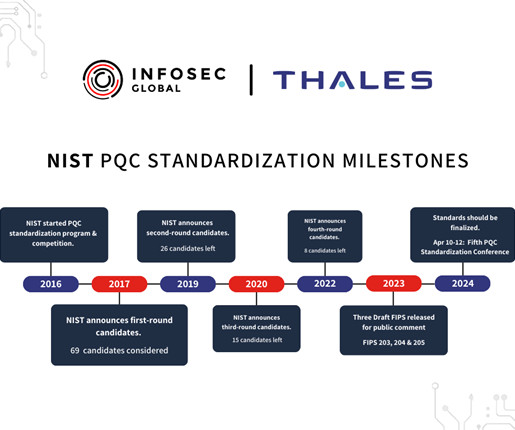
To counter HNDL, migrating critical systems to Post-Quantum Cryptography (PQC) provides encryption and authentication methods resistant to an attack from a cryptographically relevant quantum computer (CRQC). The National Institute of Standards and Technology (NIST) has long played an active role in shaping cybersecurity best practices.










































Let's personalize your content