GUEST ESSAY: ‘CyberXchange’ presents a much-needed platform for cybersecurity purchases
The Last Watchdog
OCTOBER 19, 2020
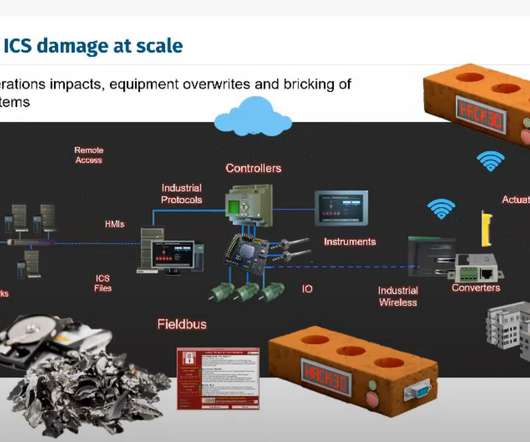
Consider that PCI-DSS alone has over 250 complex requirements that include things like endpoint protection, password management, anti-virus, border security, data recovery and awareness training. That shift will start happening in the B2B sphere and the cybersecurity industry.








































Let's personalize your content