Sophos blocked attacks exploiting XG Firewall zero-day to deploy Ransomware
Security Affairs
MAY 21, 2020
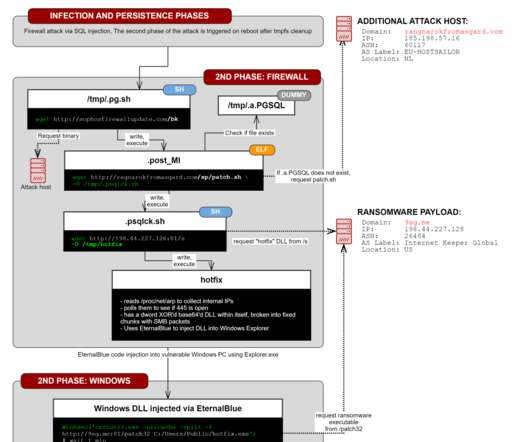
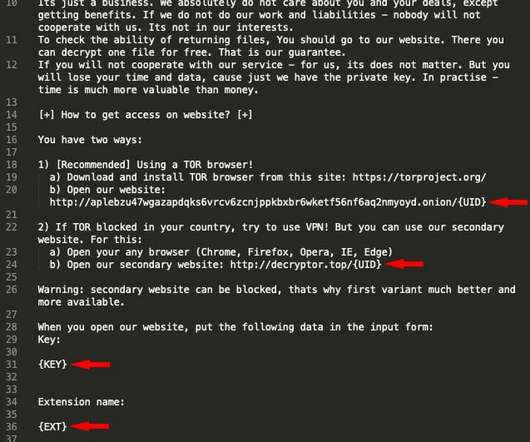
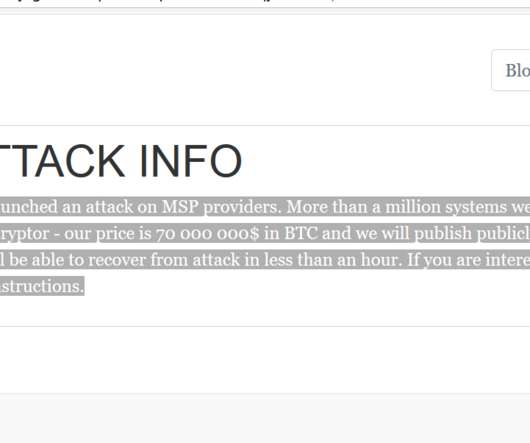
Hackers attempted to exploit a zero-day flaw in the Sophos XG firewall to distribute ransomware to Windows machines, but the attack was blocked. It was designed to download payloads intended to exfiltrate XG Firewall-resident data. The customer noticed “a suspicious field value visible in the management interface.”. “The













































Let's personalize your content