3 Top Things to Know About Social Engineering
SecureWorld News
APRIL 15, 2021
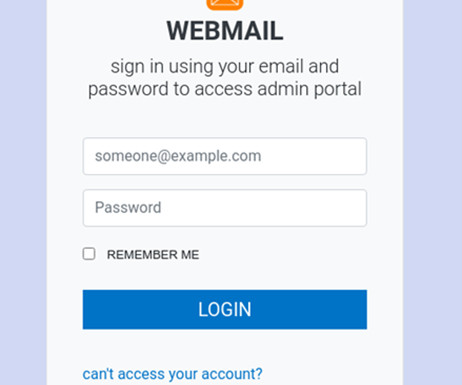
On a recent SecureWorld Sessions podcast episode, Social Engineering: Hacking Humans , host Bruce Sussman spoke with Christopher Hadnagy, an entrepreneur and author of five books about social engineering and hacking the human. 1 How do you define social engineering? 19 million, okay?







































Let's personalize your content