Killnet targeting healthcare apps hosted on Microsoft Azure
CyberSecurity Insiders
MARCH 24, 2023
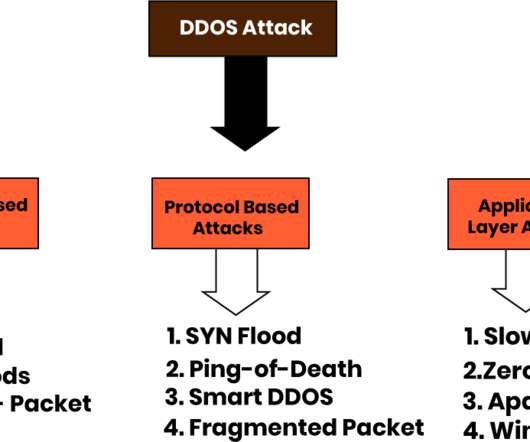
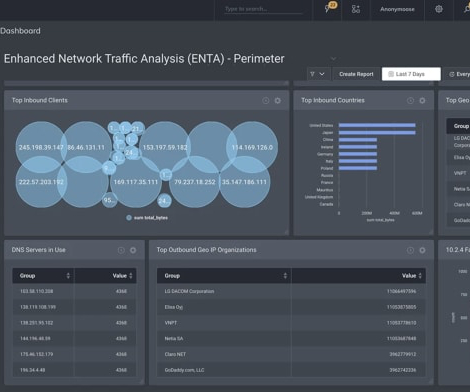
Microsoft issued a clarification that those enrolled in Azure DDoS Network Protection and Web Application Firewall services need not worry as all such attacks will be mitigated by the threat detection teams of the company.





































Let's personalize your content