How to Use Your Asset Management Software to Reduce Cyber Risks
CyberSecurity Insiders
APRIL 29, 2022
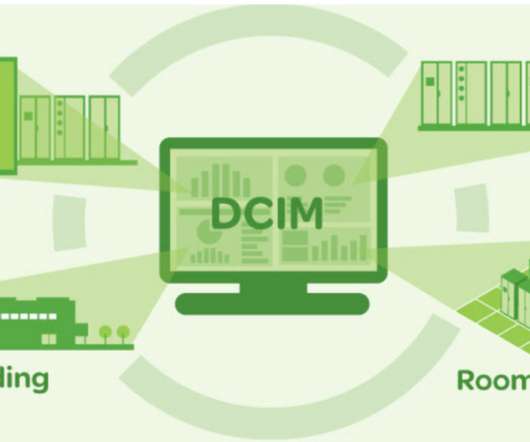
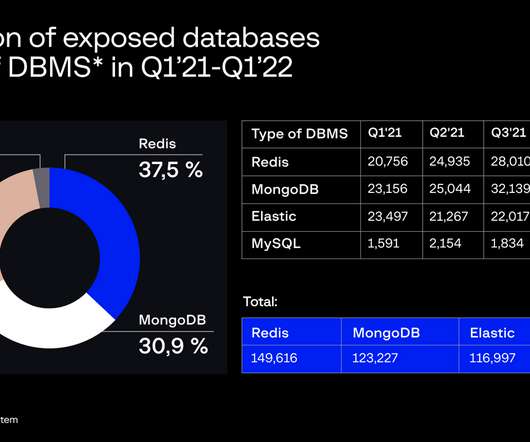
Here is a rundown of the benefits of an asset management software in cutting down cyber-related threats. Identify assets and their associated risks. Admins can reduce security risks associated with unidentified, forgotten, or malfunctioning IT assets when IT possessions are tracked. Source . .











































Let's personalize your content