How to Block a Program in a Firewall (Windows & Mac)
eSecurity Planet
MAY 6, 2024
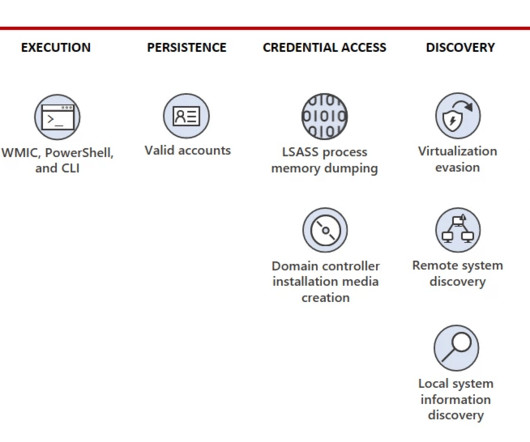
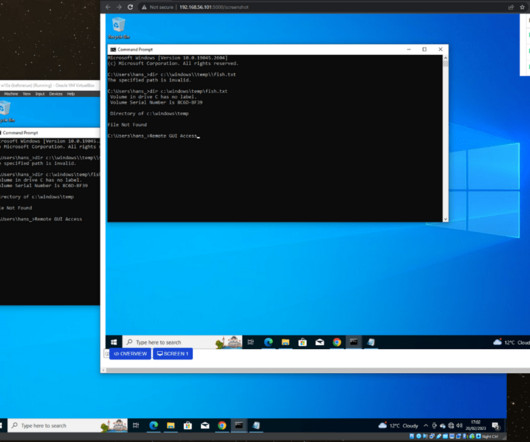
Blocking a program in a firewall is a security measure that protects systems from unwanted access. This process monitors resource consumption, limits internet access, blocks inbound access from malicious sources, and prevents outbound access from installed apps. Block it if it’s not confirmed or if you’re not sure of its legitimacy.














































Let's personalize your content