U.S. Hacks QakBot, Quietly Removes Botnet Infections
Krebs on Security
AUGUST 29, 2023
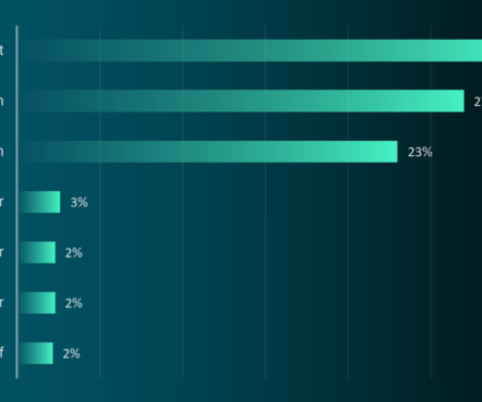
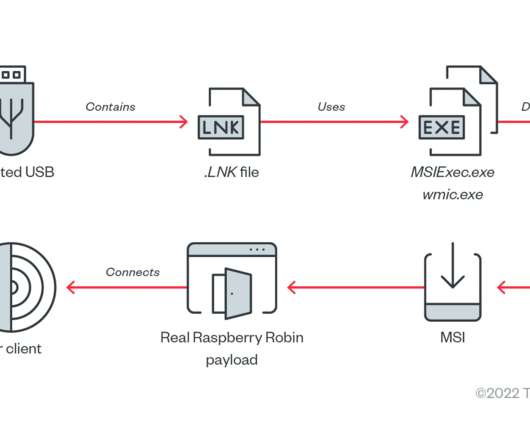
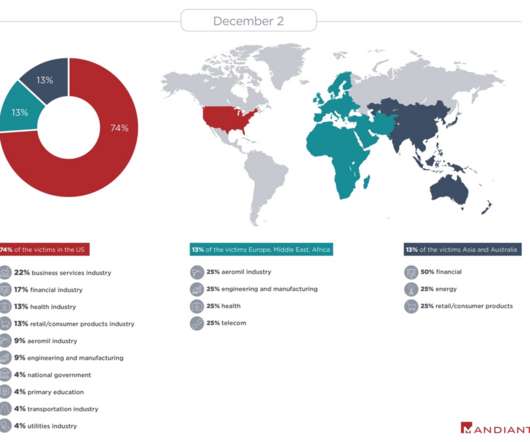
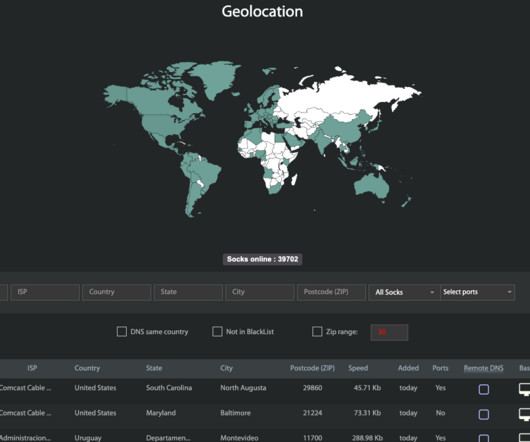
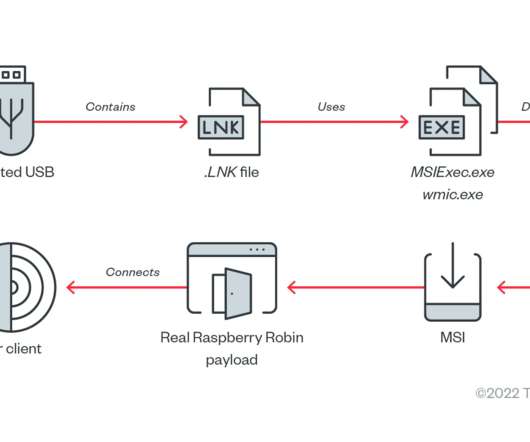
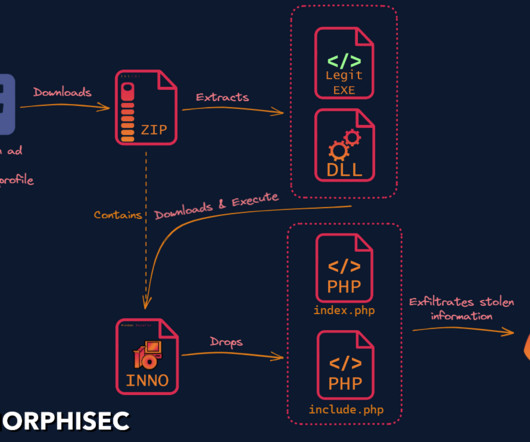
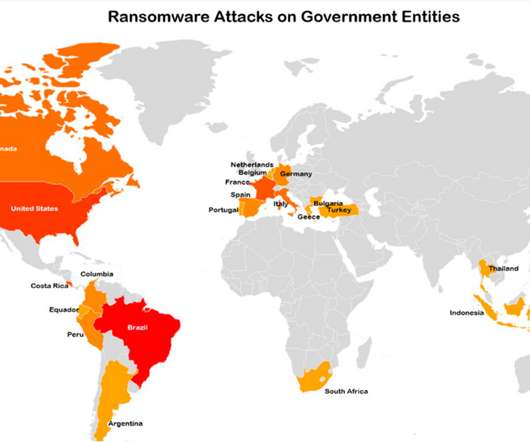
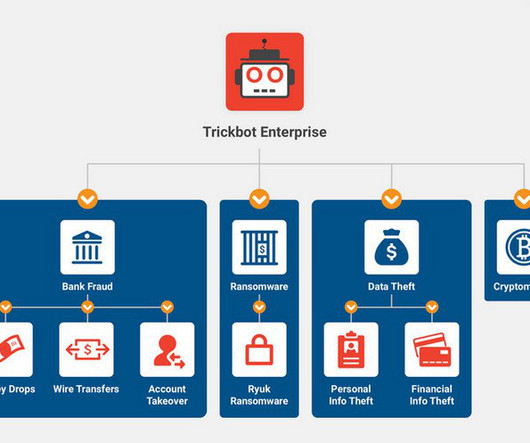
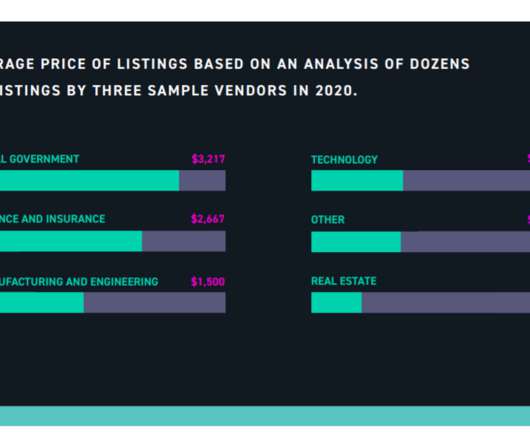
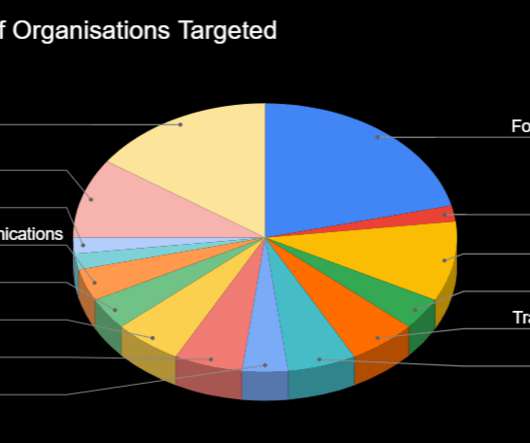
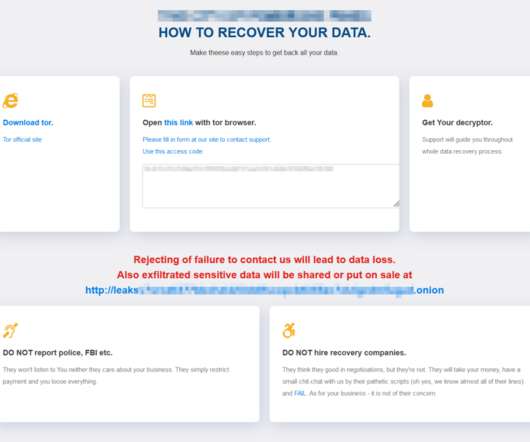
government today announced a coordinated crackdown against QakBot , a complex malware family used by multiple cybercrime groups to lay the groundwork for ransomware infections. Qakbot/Qbot was once again the top malware loader observed in the wild in the first six months of 2023.
























Let's personalize your content