Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

eSecurity Planet
NOVEMBER 10, 2023
DNS security protects the domain name system (DNS) from attackers seeking to reroute traffic to malicious sites. Since a majority of business IT traffic now accesses or passes through the internet, DNS plays an increasingly important — and vulnerable — role. in the DNS cache for more efficient delivery of information to users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
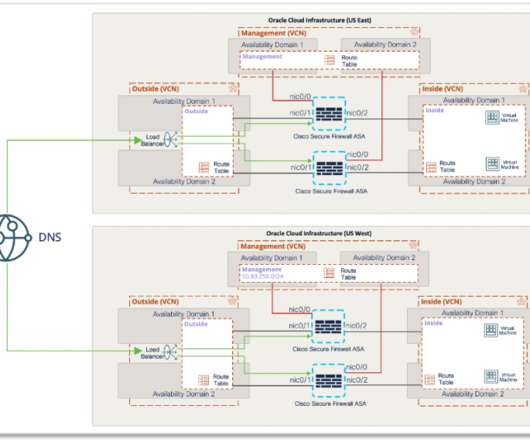
Cisco Security
JULY 9, 2021
With Cisco Secure Firewall, organizations are able to build a scalable RAVPN architecture on OCI, providing employees secure remote access to their organization’s resources from any location or endpoint. It enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port.

SC Magazine
MARCH 4, 2021
A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats. According to NSA and CISA, the service provides defenses in various points of the network exploitation lifecycle, addressing phishing, malware distribution, command and control, domain generation algorithms, and content filtering.

Cisco Security
MARCH 11, 2021
After examining topics such as the MITRE ATT&CK framework , LOLBins , and others, this release will look at DNS traffic to malicious sites. We’ll also look at malicious DNS activity—the number of queries malicious sites receive. Organizations and malicious DNS activity. 48 percent found information-stealing malware activity.

Security Boulevard
MAY 17, 2024
HYAS Protect protective DNS includes a user-friendly interface and four core deployment methods. Organizations of any size can monitor traffic with HYAS Protect’s cloud-based DNS resolver. DNS data from HYAS Protect allows organizations to identify their riskiest users and prioritize proactive security measures.

Cisco Security
MARCH 11, 2021
After examining topics such as the MITRE ATT&CK framework , LOLBins , and others, this release will look at DNS traffic to malicious sites. We’ll also look at malicious DNS activity—the number of queries malicious sites receive. Organizations and malicious DNS activity. 48 percent found information-stealing malware activity.

Security Boulevard
MARCH 3, 2023
Malvertising Enters a New Age While Google grapples with the potential threat that ChatGPT poses to its advertising business, cybercriminals are taking advantage of Google Ads to ramp up their phishing attacks on unsuspecting victims. Your firewall had no problems letting the requested HTTPS traffic through. Next-gen protective DNS.

Cisco Security
AUGUST 12, 2021
This requires a robust connection to the Internet (Lumen and Gigamon), firewall protection (Palo Alto Networks), segmented wireless network (Commscope Ruckus) and network full packet capture & forensics and SIEM (RSA NetWitness); with Cisco providing cloud-based security and intelligence support. Threat Grid (Secure Malware Analytics).

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.

Webroot
APRIL 13, 2021
This includes essential security measures like firewalls, endpoint protection and DNS protection. And, since even firewalls can be circumvented, it means keeping backups of all business data so you never have to pay a ransom to get your data back. Attacks like BEC are less about malware and more about manipulating people.
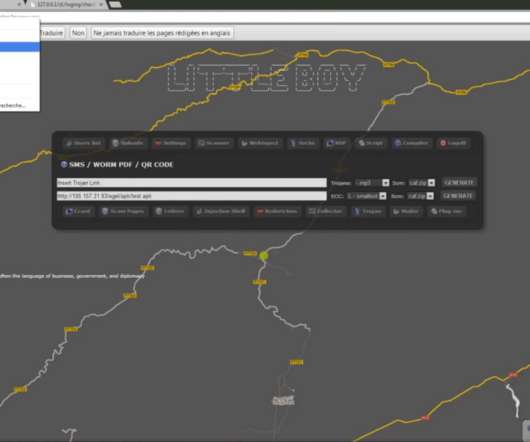
Krebs on Security
MARCH 2, 2020
A large number of French critical infrastructure firms were hacked as part of an extended malware campaign that appears to have been orchestrated by at least one attacker based in Morocco, KrebsOnSecurity has learned.
Webroot
FEBRUARY 16, 2021
In recent months, you’ve likely heard about DNS over HTTPS , also known as DNS 2.0 and DoH, which is a method that uses the HTTPS protocol to encrypt DNS requests, shielding their contents from malicious actors and others who might misuse such information. Ultimately, this DNS privacy upgrade has been a long time coming.

eSecurity Planet
JULY 29, 2021
Social engineering can manifest itself across a wide range of cybersecurity attacks: Phishing Smishing Vishing Whaling Pharming Baiting Pretexting Scareware Deepfakes. Phishing is a broad category of social engineering attacks that specifically target most businesses’ primary mode of communication: email.

CyberSecurity Insiders
JUNE 29, 2023
Executive summary Credential harvesting is a technique that hackers use to gain unauthorized access to legitimate credentials using a variety of strategies, tactics, and techniques such as phishing and DNS poisoning. According to recent research , phishing assaults targeted credential harvesting in 71.5% of cases in 2020.

CyberSecurity Insiders
MARCH 21, 2021
Therefore, make sure to set up the latest network routers and firewall protocols across all IT equipment to strengthen your security and create a defense against hackers and security breaches. Anti-virus and anti-malware . Firewalls . Install hardware firewalls for the maximum level of network security. .

eSecurity Planet
DECEMBER 8, 2023
Domain name service (DNS) attacks threaten every internet connection because they can deny, intercept, and hijack connections. With the internet playing an increasing role in business, securing DNS plays a critical role in both operations and security. Everything You Need to Know.

SiteLock
AUGUST 27, 2021
This inclusion can then be used to initiate the following: Deliver malicious payloads that can be used to include attack and phishing pages in a visitors’ browsers. A CSRF attack was recently used to seize all control of a Brazilian bank’s DNS settings for over five hours. Include malicious shell files on publicly available websites.
Cisco Security
OCTOBER 19, 2021
In any perimeter defense a key component is firewalls—the proverbial guard towers in your fortifications. In this Threat Trends release, we’ll be looking at Cisco Secure Firewall. The goal is to highlight the common threats that organizations encounter and block with Secure Firewall. Secure Firewall version 7.0

SecureList
SEPTEMBER 21, 2023
The first-ever large-scale malware attacks on IoT devices were recorded back in 2008, and their number has only been growing ever since. A successful password cracking enables hackers to execute arbitrary commands on a device and inject malware. Statista portal predicts their number will exceed 29 billion by 2030. Tested, tried.

eSecurity Planet
FEBRUARY 16, 2021
Malware, short for “malicious software,” is any unwanted software on your computer that, more often than not, is designed to inflict damage. Since the early days of computing, a wide range of malware types with varying functions have emerged. Best Practices to Defend Against Malware. Jump ahead: Adware. RAM scraper.

eSecurity Planet
MARCH 15, 2021
Raise Next-Generation Firewalls . Lastly, and probably the most advanced microsegmentation method is next-generation firewalls (NGFWs). While not initially intended for the cloud, NGFW vendors are increasingly offering their security solutions in the form of firewalls as a service (FWaaS). . Best practices for microsegmentation.

CyberSecurity Insiders
JANUARY 6, 2022
Many people still don’t realize the dangers of phishing, malware, ransomware, unpatched software, and weak passwords. HTTPS and DNS), data link (e.g., Ethernet and MAC), the session (WEB sockets), transport (SSL, TCP, and UDP), perimeter (firewalls), and physical layers (securing endpoint devices).

Vipre
JANUARY 25, 2021
According to the independent institute AV-TEST , the number of total new malware in 2020 increased by 13% compared to the last year, and malware for macOS by 1200% for the same period. Ad blockers, as the name suggests, block advertisements and protects you from phishing scams. Ad Blockers.

eSecurity Planet
JUNE 8, 2023
Email security consists of the policies, tools, and services deployed to protect against threats specific to email such as spam, phishing attacks, malware-infested attachments, impersonation, and email interception.

Pen Test Partners
SEPTEMBER 13, 2023
There is also now a requirement to have automatic process mechanisms in place to detect and protect personnel against email phishing. Section 6 A requirement coming into force in March 2025 is that organisations will need to have a web application firewall in place for any web applications exposed to the internet.

eSecurity Planet
MARCH 14, 2023
When the internet arrived, the network added a firewall to protect networks and users as they connected to the world wide web. Technical controls may be implemented by: Hardware appliances : switches, routers, firewalls, etc. In a complex, modern network, this assumption falls apart.

Cisco Security
AUGUST 29, 2022
25+ Years of Black Hat (and some DNS stats), by Alejo Calaoagan. Cisco is a Premium Partner of the Black Hat NOC , and is the Official Wired & Wireless Network Equipment, Mobile Device Management, DNS (Domain Name Service) and Malware Analysis Provider of Black Hat. Cisco Secure Malware Analytics (formerly Threat Grid).

eSecurity Planet
APRIL 26, 2024
Server: Provides powerful computing and storage in local, cloud, and data center networks to run services (Active Directory, DNS, email, databases, apps). Next-generation firewalls (NGFWs): Improve the general security of a firewall with advanced packet analysis capabilities to block malware and known-malicious sites.
Cisco Security
DECEMBER 8, 2022
While much of the spam circulating is innocuous, many emails are phishing attempts, and some are indeed malicious. To explore these scams, we used a dedicated computer, segmented from the rest of the network, and leveraged Cisco Secure Malware Analytics to safely open the emails before clicking on links or opening attachments.

eSecurity Planet
FEBRUARY 4, 2022
Malware is one of the biggest threats businesses face, and with nearly a third of all malware coming through the internet and email, businesses and consumers alike need ways to protect themselves. Also Read: Mobile Malware: Threats and Solutions. DNS leak protection Kill switch No log policy. Antivirus Software.
Security Boulevard
APRIL 18, 2022
These typically include phishing, malware attacks/compromised devices, ransomware, DDoS, unauthorized account creation, and network security rule changes. Maybe it’s DNS reputation on a suspicious IP address or an adversary profile based on the command and control traffic. What’s required to make that call?

eSecurity Planet
MARCH 22, 2023
The tools also depend upon physical controls that should also be implemented against malicious physical access to destroy or compromise networking equipment such as routers, cables, switches, firewalls, and other networking appliances. These physical controls do not rely upon IT technology and will be assumed to be in place.

eSecurity Planet
DECEMBER 15, 2021
Secure web gateway (SWG) solutions help keep enterprise networks from falling victim to ransomware , malware , and other threats carried by internet traffic and malicious websites. This is accomplished through various components, including malware detection and URL filtering. Malware detection. Anti-malware scanning.

eSecurity Planet
SEPTEMBER 29, 2021
Recent research by Positive Technologies looked at the cyber threat landscape during Q2 2021 and found that ransomware attacks reached “stratospheric” levels, accounting for 69% of all malware attacks, a huge jump from 39% in Q2 2020. Detect compromised accounts, insider threats, and malware. EnigmaSoft. File scanning.

eSecurity Planet
MARCH 16, 2023
Downloadable malware : When clicked, links in emails or extensions on websites immediately download malicious software onto a host machine. Sometimes this malware can laterally move through the network. Devices that have been infected by malware, like routers, are a threat to the rest of the network.

eSecurity Planet
MAY 28, 2021
Malware detection has long been a game of signature detection. With ML and artificial intelligence (AI) using thousands of strains to train algorithms, one would surmise that the ability to detect malware is only improving. Hackers are using the same ML and AI technology to avoid using recognized malware. Gateway Compromise.

eSecurity Planet
DECEMBER 17, 2021
Continuous monitoring of unsanctioned applications, malware , security policies, and more. Multiple security layers to protect against cloud threats and malware. Scan cloud infrastructure for compromised users, rogue apps, and known malware. Malware detection and prevention. Censornet Features. Microsoft Features.
Daniel Miessler
MAY 8, 2020
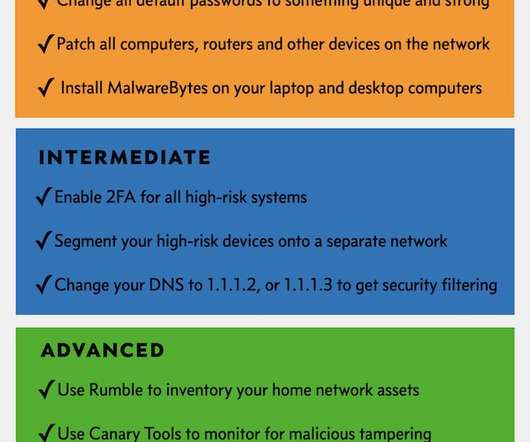
Most home networks get broken into through either phishing or some random device they have with a bad password. MalwareBytes has somehow won the battle of the best consumer anti-malware offering. Change your DNS to 1.1.1.2, Next, you can consider changing your DNS settings on all your devices to use those by Cloudflare.

eSecurity Planet
DECEMBER 3, 2021
Brian Krebs is an independent investigative reporter known for his coverage of technology, malware , data breaches , and cybercrime developments. Russian software engineer Eugene Kaspersky’s frustration with the malware of the 80s and 90s led to the founding of antivirus and cybersecurity vendor Kaspersky Lab.

eSecurity Planet
MAY 2, 2024
Compromised Credentials Compromised identities from phishing, info stealers, keyloggers, and bad password habits provide the entry point for most ransomware attacks and data breaches. Sophos: Noted that 43% of all 2023 malware signature updates are for stealers, spyware, and keyloggers often used to steal credentials from devices.

SecureList
JUNE 15, 2022
I will buy accounts for access to corporate VPNs or firewalls (FortiGate, SonicWall, PulseSecure, etc.) In contrast, less experienced cybercriminals are not always able to see an attack through to the end (malware execution, data theft, etc.), Phishing attacks on employees. Malware log offers on a dark web forum.

eSecurity Planet
MAY 19, 2022
EdgeConnect Enterprise critically comes with firewall , segmentation , and application control capabilities. The first traditional cybersecurity vendor featured is Barracuda Networks, with consistent recognition for its email security , next-generation firewalls ( NGFW ), web application security , and backups. Barracuda Networks.
eSecurity Planet
FEBRUARY 25, 2022
Wiper malware , including the latest HermeticWiper identified by ESET and Symantec. Williams urged viewers to focus on the basics, like phishing , passwords and patching /updating, as those are still the entry point of many attacks. Firewalls work both ways. Espionage, which has included targeting U.S.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content