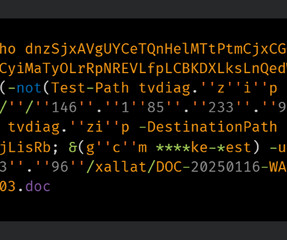
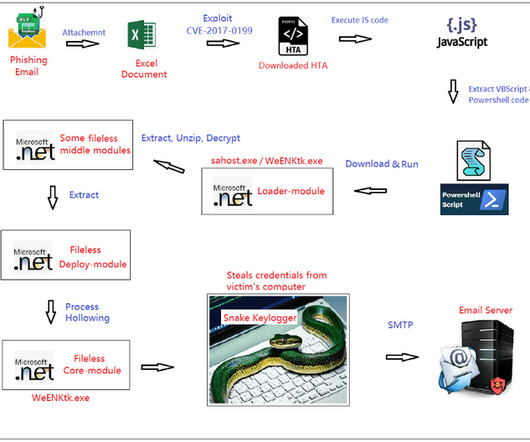
ClickFix: How to Infect Your PC in Three Easy Steps
Krebs on Security
MARCH 14, 2025
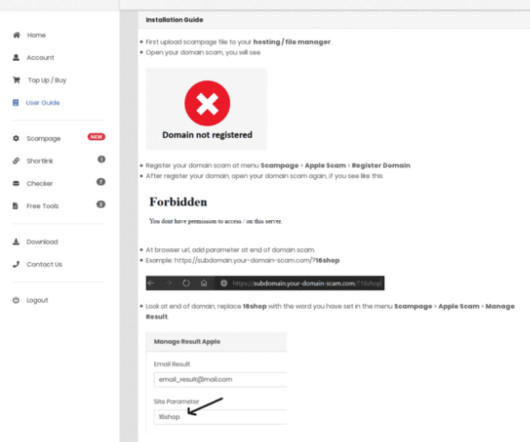
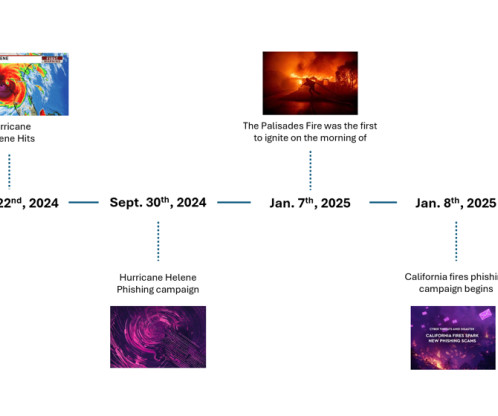
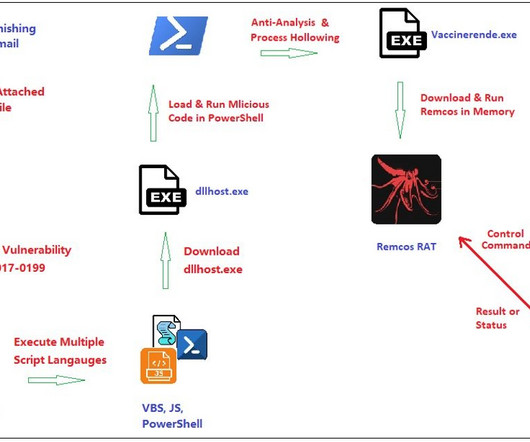
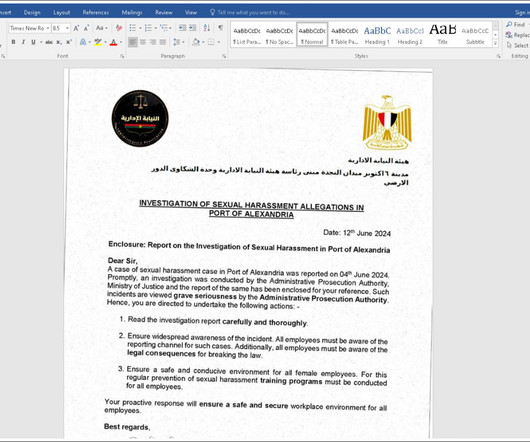
In November 2024, KrebsOnSecurity reported that hundreds of hotels that use booking.com had been subject to targeted phishing attacks. From there, they sent out phishing messages asking for financial information from people who’d just booked travel through the company’s app. HTML files containing ClickFix instructions.






































Let's personalize your content