How to use TunnelBear VPN (Step-by-Step Tutorial)
Tech Republic Security
MARCH 5, 2024
This is an in-depth tutorial on how to use TunnelBear VPN. Learn how to download, set up and use TunnelBear VPN with our guide.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MARCH 5, 2024
This is an in-depth tutorial on how to use TunnelBear VPN. Learn how to download, set up and use TunnelBear VPN with our guide.

SecureBlitz
AUGUST 3, 2021
Will a VPN prevent my ISP from seeing what I download? A VPN can prevent your ISP from seeing what you download by encrypting the data leaving your device. What your VPN sees is scrambled data with no way of knowing or seeing what you’re downloading, the website you’re downloading from, and the.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Bleeping Computer
DECEMBER 22, 2023
Three malicious Chrome extensions posing as VPN (Virtual Private Networks) infected were downloaded 1.5 million times, acting as browser hijackers, cashback hack tools, and data stealers. [.]
SecureBlitz
FEBRUARY 1, 2022
Today, we will show you how to download and install CyberGhost VPN on your Windows and Mac PC. CyberGhost VPN is a powerful VPN application used by so many people across the globe. This is a VPN service that protects your online identity from hackers, ISP, and legal authorities. How does it do this?

Tech Republic Security
MARCH 5, 2024
Selecting the right virtual private network provider for your needs requires a fair bit of legwork because the choices are many and the offerings vary greatly. This quick-glance chart from TechRepublic Premium is blank and to be filled in by the user. The idea is to round up the top contenders and compare them across.

SecureBlitz
FEBRUARY 1, 2021
Although, you can use Thunder VPN only on your Android phone; however, in this post, I will show you how to download it for your PC. A VPN or virtual private network is a piece of software that helps to create a tunnel between your network and a private VPN server. This VPN helps to.

CyberSecurity Insiders
NOVEMBER 28, 2022
Windows 11 is all set to get a VPN Status Indicator in its system tray, allowing users to connect or download files anonymously and without the revelation of their home or IP address. The post Windows 11 gets a VPN Status Indicator appeared first on Cybersecurity Insiders.

Identity IQ
OCTOBER 17, 2023
Should You Always Use a VPN? IdentityIQ Using a virtual private network (VPN) can help keep you safe and anonymous online. It’s a good idea to always keep your VPN active for maximum protection, but there are certain scenarios when you might need to temporarily shut it off. Here’s what you need to know about VPNs.

SecureBlitz
MARCH 7, 2022
One of our readers asked – is Turbo VPN safe to use? Find out in this Turbo VPN review. Currently, the use of VPN is fast becoming a must for cybersecurity and Turbo VPN is trying to also shine amongst other VPN providers. You might be wondering if this app with 300 million downloads is.

Security Affairs
JANUARY 31, 2024
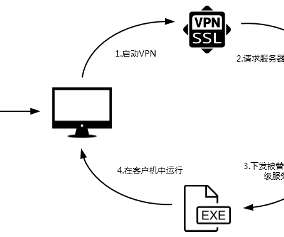
Threat actors are exploiting recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) VPN devices to deliver KrustyLoader. Synacktiv researchers noticed that threat actors used the KrustyLoader as a loader to download a Golang-based Sliver backdoor from a remote server and execute it. ” concludes the report.

Security Affairs
SEPTEMBER 8, 2023
CISA warned that nation-state actors are exploiting flaws in Fortinet FortiOS SSL-VPN and Zoho ManageEngine ServiceDesk Plus. Cybersecurity and Infrastructure Security Agency (CISA) warned that nation-state actors are exploiting security vulnerabilities in Fortinet FortiOS SSL-VPN and Zoho ManageEngine ServiceDesk Plus.
Heimadal Security
MARCH 11, 2022
VPNs and proxy servers are both technologies that allow you to keep your online activities private while browsing, sending emails, reading online messages, streaming video, or downloading files. The post Proxy vs VPN – Differences and Advantages appeared first on Heimdal Security Blog. What Is a Proxy Server?

Malwarebytes
JULY 16, 2021
A Virtual Private Network (VPN) can stop others from snooping on or tampering with your Internet traffic. It does this by concealing your traffic inside an encrypted tunnel between you and your VPN provider. At Malwarebytes, we have noticed an increase in VPN usage worldwide. So, does a VPN slow down Internet speeds?

eSecurity Planet
SEPTEMBER 9, 2021
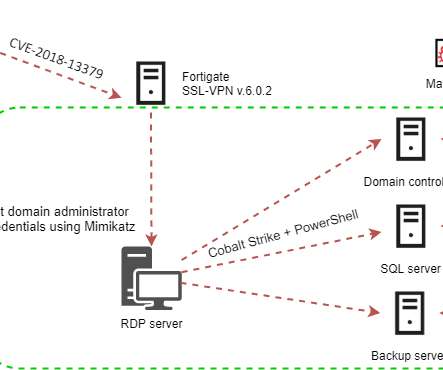
In an advisory , Fortinet said the path traversal vulnerability in the FortiOS SSL VPN web portal may allow an attacker to download FortiOS system files through specially crafted HTTP resource requests. to 5.4.12; if the SSL VPN service (web-mode or tunnel-mode) is enabled. Affected products include FortiOS 6.0 – 6.0.0

The Last Watchdog
SEPTEMBER 13, 2021
Thus, Surfshark has just become the first VPN provider to launch an antivirus solution as part of its all-in-one security bundle Surfshark One. This development is part and parcel of rising the trend of VPN providers hustling to deliver innovative “DIY security” services into the hands of individual consumers.
Malwarebytes
JANUARY 4, 2023
Synology has issued an advisory about a vulnerability that allows remote attackers to execute arbitrary commands through a susceptible version of Synology VPN Plus Server. VPN Plus Server. VPN Plus Server allows users to turn their Synology Router into a Virtual Rrivate Network (VPN) server. 0534 and 1.4.4-0635

Security Affairs
FEBRUARY 1, 2024
Rebuild the device per Ivanti’s instructions AND upgrade to one of the following supported software versions through Ivanti’s download portal (there is no cost to upgrade): 9.1R18.3, xml” file via the download portal as temporary workarounds to address CVE-2024-21888 and CVE-2024-21893. 20240126.5.xml”

Hot for Security
FEBRUARY 16, 2021
A virtual private network (VPN) provides anonymity and digital privacy by creating a secure and private tunnel between the user and the online destinations he visits. A VPN encrypts computer traffic, masking your IP address and location, preventing snoopers or hackers from viewing or intercepting your data. Netflix and chill anywhere.
Security Affairs
APRIL 7, 2021
Attackers are actively exploiting the CVE-2018-13379 flaw in Fortinet VPN to deploy the Cring ransomware to organizations in the industrial sector. The #CRING #ransomware is then downloaded via certutill. SecurityAffairs – hacking, Fortinet VPN). ” reads the post published by Kaspersky. ” continues Kaspersky.

Malwarebytes
JUNE 28, 2021
In layman’s terms, a VPN uses encryption to create a private online connection between a device and a VPN server. With a good VPN service, you can shield your data from curious eyes. The type of VPN protocol that you use can affect the speed, stability, ease of use, security, and privacy of your connection.

Security Affairs
JUNE 17, 2021
Iran-linked Ferocious Kitten APT group used instant messaging apps and VPN software like Telegram and Psiphon to deliver Windows RAT and spy on targets’ devices. One of the MarkiRAT variants analyzed by the researchers involves a plain downloader that fetches an executable from a hardcoded domain. Pierluigi Paganini.

Malwarebytes
MAY 24, 2021
In just the past year, free VPN for Android apps have exposed the data of as many as 41 million users, revealing consumers’ email addresses, payment information, clear text passwords, device IDs, and more. All these people that work on [the VPN service], nobody is going to do it for free. There is no best free VPN for Android.

Identity IQ
APRIL 22, 2021
If you want to help secure your digital identity, a virtual private network (VPN) is a great tool you can use for added online privacy. In this guide, we discuss VPNs in detail, including how they work, how they protect you and why you should use one when browsing the web. What is a VPN? How does a VPN Work?

CyberSecurity Insiders
FEBRUARY 16, 2021
Published in collaboration with the Cybersecurity Insiders, the report includes findings from a global survey of more than 350 cybersecurity professionals on the current state of remote access environments, the rise in VPN vulnerabilities, and the role zero-trust security models play in providing access to enterprise applications.
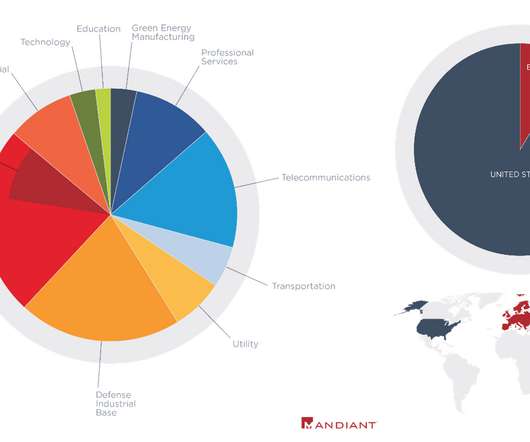
Security Affairs
MAY 28, 2021
Researchers from FireEye warn that China-linked APT groups continue to target Pulse Secure VPN devices to compromise networks. Cybersecurity researchers from FireEye warn once again that Chinese APT groups continue to target Pulse Secure VPN devices to penetrate target networks and deliver malicious web shells to steal sensitive information.

Joseph Steinberg
MAY 9, 2022
According to a report published by The Washington Post , downloads by Russians of the 10 most popular VPN applications jumped from fewer than 15,000 per day just before the Russian invasion of Ukraine to a current figure of over 300,000 a day – even reaching as high as 475,000 per day at one point during the current military campaign.

Malwarebytes
SEPTEMBER 7, 2021
The Exit Node behaves a bit like a VPN, so any service you use on the Internet will see the Exit Node’s IP address as the source of your traffic. All you have to do is download and install the latest version from the official website and use it like a regular web browser. What is the difference between Tor and a VPN?
Security Affairs
APRIL 6, 2020
DarkHotel nation-state actor is exploiting a VPN zero -day to breach Chinese government agencies in Beijing and Shanghai. State-sponsored hackers used a zero-day vulnerability in Sangfor SSL VPN servers to gain access to victims’ networks. Up to now, a large number of VPN users have been attacked.”

Security Affairs
JANUARY 18, 2022
Some administrators and users reported problems with L2TP VPN connections on Windows 10 after installing the recent Windows 10 and Windows 11 cumulative updates. The OOB updates can be downloaded from the Microsoft Update Catalog , if they are not installed directly from Windows Update as optional updates. Pierluigi Paganini.

Malwarebytes
APRIL 4, 2024
In this blog post, we look at a very recent malvertising campaign impersonating the popular VPN software NordVPN. We want to reiterate that NordVPN is a legitimate VPN provider and they are being impersonated by threat actors. This is true here as well, where we have a redirect to besthord-vpn[.]com xyz besthord-vpn[.]com

Malwarebytes
MARCH 29, 2021
In addition, we speak to Malwarebytes senior security researcher JP Taggart about the importance of trusting your VPN. But obscuring your Internet activity—including the websites you visit, the searches you make, the files you download—doesn’t mean that a VPN magically disappears those things. Source: ComputerWeekly).

Krebs on Security
DECEMBER 2, 2021
They allege that in late December 2020, Sharp applied for a job at another technology company, and then abused his privileged access to Ubiquiti’s systems at Amazon’s AWS cloud service and the company’s GitHub accounts to download large amounts of proprietary data. When FBI agents raided Sharp’s residence on Mar.

Security Affairs
APRIL 28, 2024
From March 18, 2024, to April 16, 2024, Duo Security and Cisco Talos observed large-scale brute-force attacks against a variety of targets, including VPN services, web application authentication interfaces and SSH services. Threat actors use these RESIPs to evade detection.

Security Affairs
OCTOBER 9, 2019
NSA is warning of multiple state-sponsored cyberespionage groups exploiting enterprise VPN Flaws. Last week, the UK’s National Cyber Security Centre (NCSC) reported that advanced persistent threat (APT) groups have been exploiting recently disclosed VPN vulnerabilities in enterprise VPN products in attacks in the wild.

Security Affairs
OCTOBER 6, 2019
The UK’s National Cyber Security Centre (NCSC) warns of attacks exploiting recently disclosed VPN vulnerabilities in Fortinet, Palo Alto Networks and Pulse Secure. Threat actors leverage VPN vulnerabilities in Fortinet, Palo Alto Networks and Pulse Secure, to breach into the target networks. ” reads the alert issued by the NCSC.
SiteLock
AUGUST 27, 2021
This is why using a VPN for secure browsing can help protect your data while using public network. SiteLock VPN makes securing your connection easy! Introducing SiteLock VPN, a safe and easy way to browse the internet without limits. SiteLock VPN is an application available to download for Android, Apple devices, and Windows.
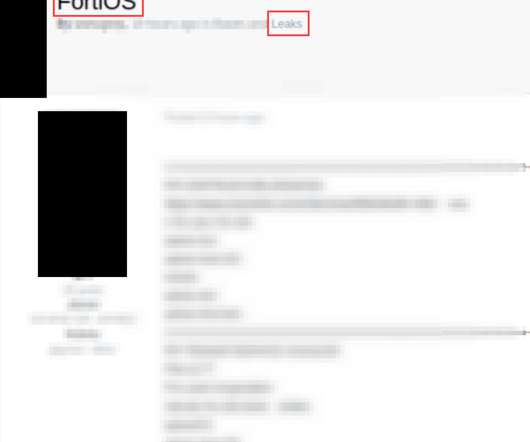
Security Affairs
NOVEMBER 29, 2022
Download the system configuration. “While during routine monitoring, researchers at Cyble observed a Threat Actor (TA) distributing multiple unauthorized Fortinet VPN access over one of the Russian cybercrime forums,” reads the analysis published by Cyble. Add new local users. Pierluigi Paganini.

Security Affairs
AUGUST 25, 2019
BadPackets experts observed on August 22 a mass scanning activity targeting Pulse Secure “Pulse Connect Secure” VPN endpoints vulnerable to CVE-2019-11510. On August 22, BadPackets experts observed a mass scanning activity targeting Pulse Secure “Pulse Connect Secure” VPN endpoints vulnerable to CVE-2019-11510. reads the advisory.

Security Boulevard
APRIL 27, 2022
Risky Behavior: VPN Providers Installing Root Certificates Without User Consent. Some VPN apps automatically install self-signed trusted root certificates without informed user consent, says cybersecurity research firm AppEsteem. “We brooke.crothers. Wed, 04/27/2022 - 16:21. And this can lead to security holes. Users not informed.

Security Affairs
NOVEMBER 14, 2019
“The malware is rather basic, and has limited capabilities that include downloading and running additional malware.” The above scheme shows that the APT group leverage a VPN layer build with a custom-built network of VPN nodes, APT33 was operating its own private VPN network. SecurityAffairs – APT33, VPN).
Google Security
NOVEMBER 2, 2023
The transparency of an app’s data security and privacy play a key role in a user’s decision to download, trust, and use an app. To help give users a simplified view of which apps have undergone an independent security validation , we’re introducing a new Google Play store banner for specific app types, starting with VPN apps.

Krebs on Security
JULY 18, 2022
911 says its network is made up entirely of users who voluntarily install its “free VPN” software. In this scenario, users indeed get to use a free VPN service, but they are often unaware that doing so will turn their computer into a proxy that lets others use their Internet address to transact online. “The 911[.]re
Security Affairs
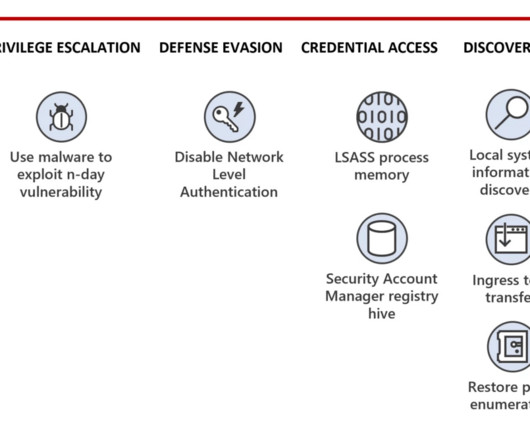
AUGUST 25, 2023
Flax Typhoon was observed using the China Chopper web shell, Metasploit, Juicy Potato privilege escalation tool, Mimikatz, and SoftEther virtual private network (VPN) client. The state sponsored hackers also uses the VPN access to scan for vulnerabilities in targeted organizations. ” continues the report.
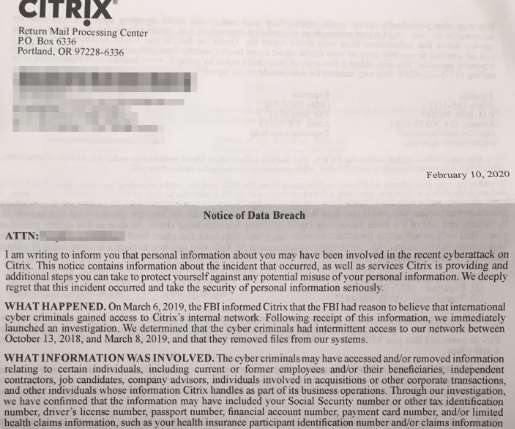
Krebs on Security
FEBRUARY 19, 2020
It is perhaps best known for selling virtual private networking (VPN) software that lets users remotely access networks and computers over an encrypted connection. Iranian hackers recently have been blamed for hacking VPN servers around the world in a bid to plant backdoors in large corporate networks.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content