Facebook’s Extensive Surveillance Network
Schneier on Security
FEBRUARY 1, 2024
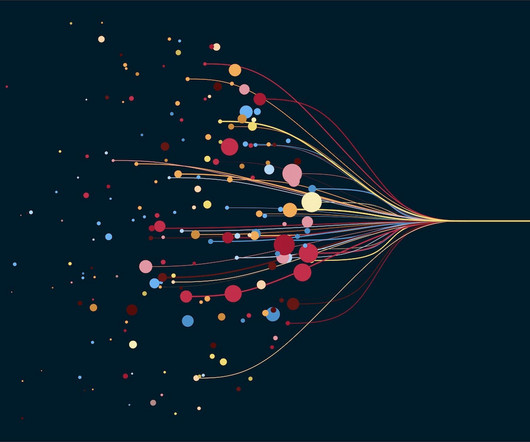
Consumer Reports is reporting that Facebook has built a massive surveillance network: Using a panel of 709 volunteers who shared archives of their Facebook data, Consumer Reports found that a total of 186,892 companies sent data about them to the social network. On average, each participant in the study had their data sent to Facebook by 2,230 companies.
















Let's personalize your content