Active Nitrogen campaign delivered via malicious ads for PuTTY, FileZilla
Malwarebytes
APRIL 9, 2024
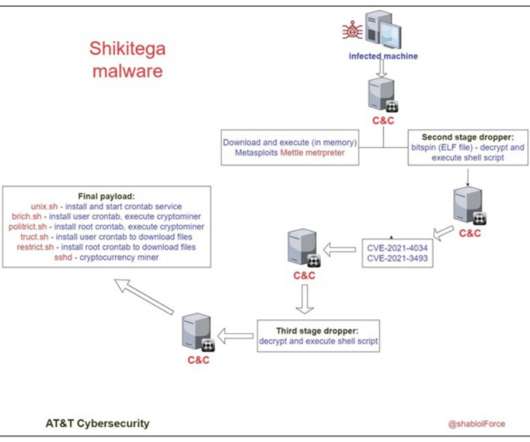
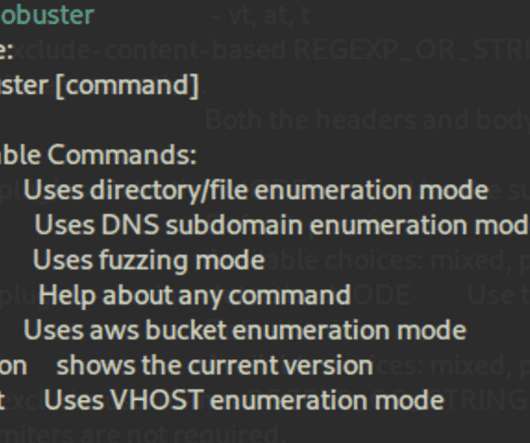
In the past couple of weeks, we have observed an ongoing campaign targeting system administrators with fraudulent ads for popular system utilities. The malicious ads are displayed as sponsored results on Google’s search engine page and localized to North America. dll (Nitrogen).
































Let's personalize your content