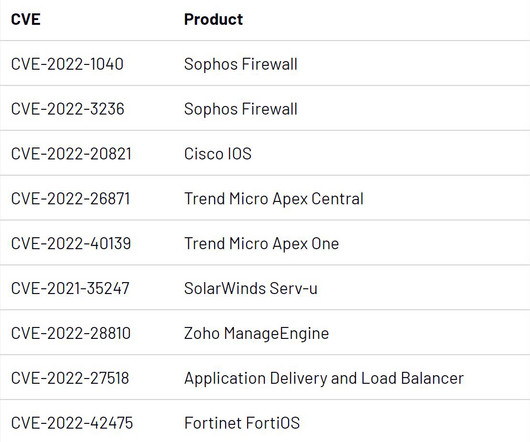
CISA Order Highlights Persistent Risk at Network Edge
Krebs on Security
JUNE 15, 2023
The directive applies to any networking devices — such as firewalls, routers and load balancers — that allow remote authentication or administration. The researchers found that just being able to reach the management interface for a vulnerable Fortinet SSL VPN appliance was enough to completely compromise the devices.













































Let's personalize your content