Understanding the Essential Pillars of Phishing Mitigation
SecureWorld News
JUNE 6, 2023
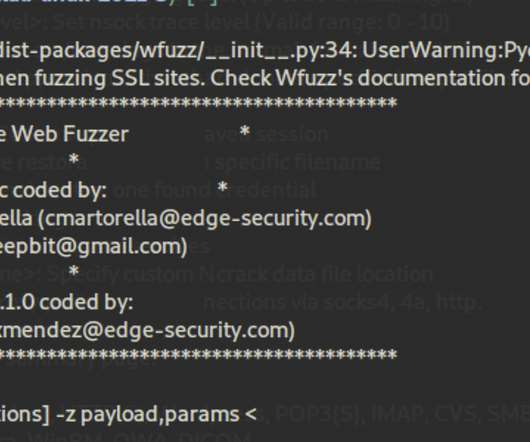
These attacks can come from malicious instructions, social engineering, or authentication attacks, as well as heavy network traffic. Defending against phishing The general defense methods for protecting oneself against an attack can be thought of as the pillars that support your overall security online.
























Let's personalize your content