Understanding AI risks and how to secure using Zero Trust
CyberSecurity Insiders
JUNE 12, 2023
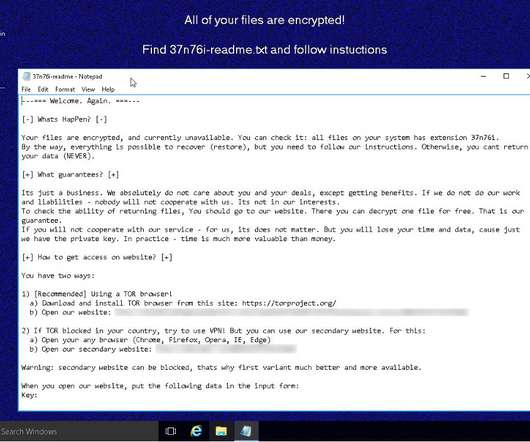
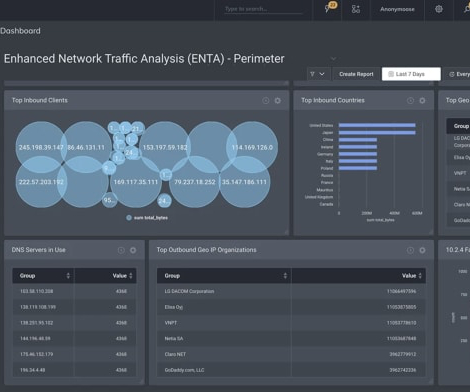
Understanding AI threats Mitigating AI threats risks requires a comprehensive approach to AI security, including careful design and testing of AI models, robust data protection measures, continuous monitoring for suspicious activity, and the use of secure, reliable infrastructure.











































Let's personalize your content