IoT and Cybersecurity: What’s the Future?
Security Affairs
MAY 2, 2022
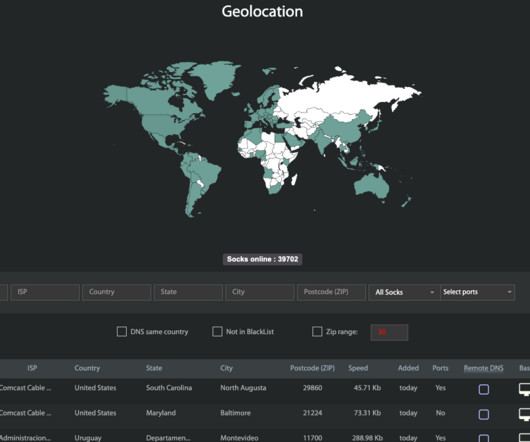
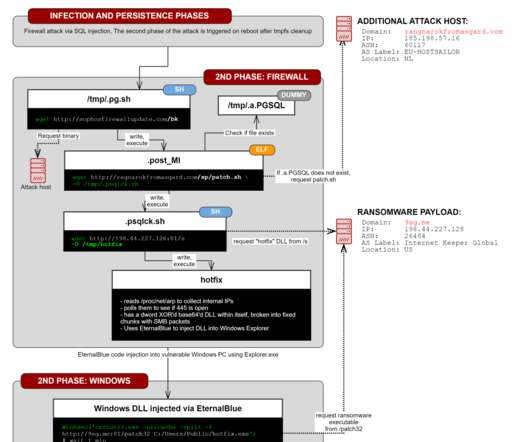
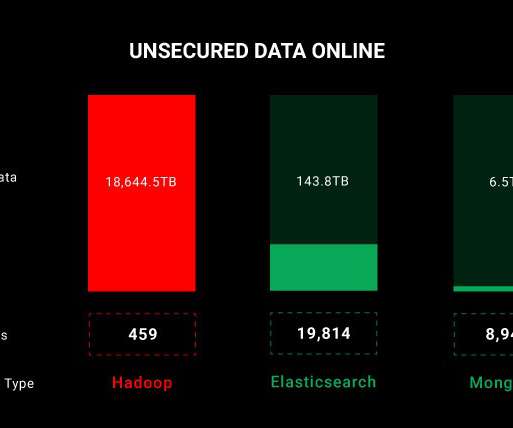
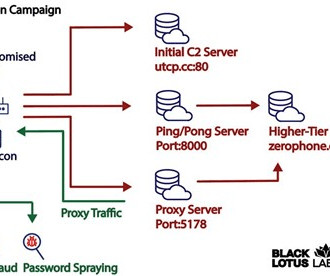
IoT gizmos make our lives easier, but we forget that these doohickeys are IP endpoints that act as mini-radios. Department of Homeland Security described IoT security as a matter of homeland security. IoT devices expose users to two main weaknesses. IoT Means Someone Has To Store Loads Of Data.




































Let's personalize your content