Can a VPN Be Hacked?
Tech Republic Security
APRIL 23, 2024
Learn about the potential vulnerabilities of VPNs and the measures you can take to enhance your VPN security.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
APRIL 23, 2024
Learn about the potential vulnerabilities of VPNs and the measures you can take to enhance your VPN security.

Malwarebytes
MARCH 11, 2021
Virtual Private Networks ( VPN s) are popular but often misunderstood. VPNs are for illegal activity. Some people think that VPNs are only useful for doing things like torrenting, accessing geo-locked content, or getting around work/school/government firewalls. I don’t need a mobile VPN. My VPN won’t let me watch Netflix.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CyberSecurity Insiders
JUNE 6, 2023
In 2019, the United Nations released an estimate confirming that the North Korean regime, led by Kim Jong Un, had accumulated a staggering $2 billion by launching hacks on cryptocurrency firms and internationally recognized banks. The post North Korean cyber attacks income and free VPN data breach appeared first on Cybersecurity Insiders.

Security Affairs
JANUARY 31, 2024
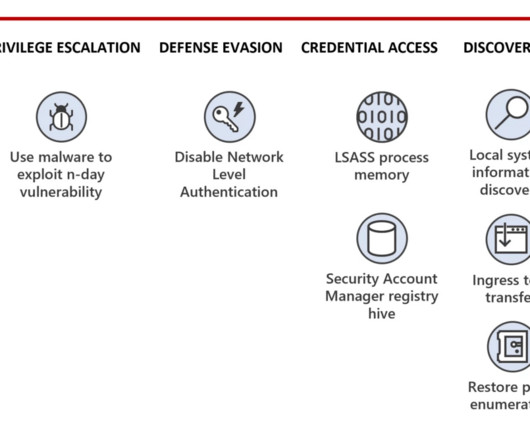
Threat actors are exploiting recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) VPN devices to deliver KrustyLoader. ” Sliver is a post-exploitation framework that is gaining notoriety in the hacking underground as an alternative to the Cobalt Strike framework. ” concludes the report.

CyberSecurity Insiders
AUGUST 6, 2021
Most VPNs are user-friendly and are created with well-detailed guides which are navigable by nearly anyone, even a technology illiterate individual. In addition to that, VPNs have come in handy, especially during the pandemic since most employees are working remotely, and therefore, data security is still maintained.
Security Affairs
JANUARY 16, 2024
Experts warn that recently disclosed Ivanti Connect Secure VPN and Policy Secure vulnerabilities are massively exploited in the wild. Through forensic analysis of the memory sample, Volexity was able to recreate two proof-of-concept exploits that allowed full unauthenticated command execution on the ICS VPN appliance.
Security Affairs
DECEMBER 26, 2023
The Rhysida ransomware group claimed to have hacked Abdali Hospital, a multi-specialty hospital located in Jordan. pic.twitter.com/6uHMDcNhTC — Dominic Alvieri (@AlvieriD) December 26, 2023 The group published images of stolen documents as proof of the hack. Abdali Hospital provides care to patients in numerous specialties.
Krebs on Security
MAY 28, 2024
KrebsOnSecurity identified one of the three men in a July 2022 investigation into 911 S5, which was massively hacked and then closed ten days later. 911 built its proxy network mainly by offering “free” virtual private networking (VPN) services. based startup that tracks proxy and VPN services.
Security Affairs
NOVEMBER 25, 2023
The Rhysida ransomware group claimed to have hacked the Chinese state-owned energy conglomerate China Energy Engineering Corporation. The ransomware gang hit organizations in multiple industries, including the education, healthcare, manufacturing, information technology, and government sectors. reads the joint advisory.

Security Affairs
JUNE 11, 2021
Ask your employees to use a VPN , antivirus and other necessary tools to ensure digital privacy. SecurityAffairs – hacking, cyber threats). The post CEO-Level Guide to Prevent Data Hacking Technologies & Incidents appeared first on Security Affairs. Follow me on Twitter: @securityaffairs and Facebook.
Security Affairs
NOVEMBER 29, 2023
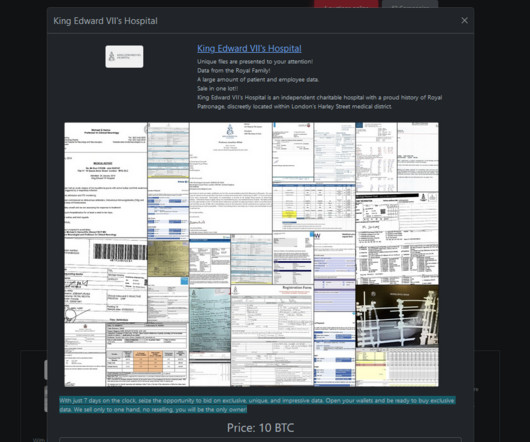
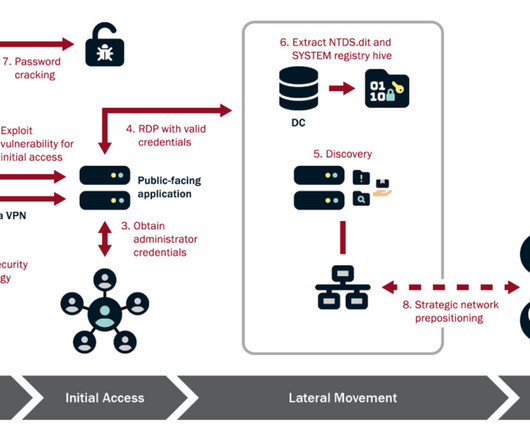
The Rhysida ransomware group claimed to have hacked King Edward VII’s Hospital in London. The Rhysida ransomware group claimed to have hacked King Edward VII’s Hospital in London and added it to the list of victims on its Tor leak site. VPNs, RDPs) to gain initial access to the target network and maintain persistence.

Security Affairs
JANUARY 18, 2022
Europol this week announced the shutdown of VPNLab, a VPN service that is very popular in the cybercrime ecosystem. An international operation conducted by law enforcement bodies from 10 countries took down VPNLab.net, a VPN service provider that is very popular in the cybercrime ecosystem. SecurityAffairs – hacking, VPNLab).

Security Affairs
JUNE 19, 2021
North Korea-linked APT group Kimsuky allegedly breached South Korea’s atomic research agency KAERI by exploiting a VPN vulnerability. A KAERI spokesperson revealed that threat actors exploited a vulnerability in a virtual private network (VPN) server to gain access to the network of the institute. ” reported The Record.
Security Affairs
JANUARY 21, 2023
Researchers warn of about 19,500 end-of-life Cisco VPN routers on the Internet that are exposed to the recently disclosed RCE exploit chain. The communications technology firm said that there are no workarounds to fix this flaw, however, admins may disable remote management and block access to ports 443 and 60443.
Security Affairs
MARCH 21, 2022
Microsoft is investigating claims that the Lapsus$ hacking group breached its internal Azure DevOps source code repositories. On Thursday, March 10, Lapsus$ ransomware gang announced they’re starting to recruit insiders employed within major technology giants and ISPs, such companies include Microsoft, Apple, EA Games and IBM.

Security Affairs
FEBRUARY 16, 2024
The threat actor compromised network administrator credentials through the account of a former employee that was used to successfully authenticate to an internal virtual private network (VPN) access point. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, CISA)

Security Boulevard
FEBRUARY 2, 2024
Introduction Ivanti, an IT management and security company, has issued a warning about multiple zero-day vulnerabilities in its VPN products exploited by Chinese state-backed hackers since December 2023. to gain access to ICS VPN appliances. Zero trust is a fundamentally different architecture than those built upon firewalls and VPNs.

SecureWorld News
JUNE 21, 2021
The South Korean Atomic Energy Research Institute (KAERI) recently confirmed that their internal servers had been breached and they suspect a North Korean hacking group to be the culprit. In this process, the researcher even made a move to cover up the hacking.". South Korea Atomic Energy Research Institute Hacked.

SecureWorld News
JUNE 21, 2021
The South Korean Atomic Energy Research Institute (KAERI) recently confirmed that its internal servers had been breached and they suspect a North Korean hacking group to be the culprit. In this process, the researcher even made a move to cover up the hacking.". South Korea Atomic Energy Research Institute hacked.

Krebs on Security
MAY 23, 2024
At least a dozen patriotic Russian hacking groups have been launching DDoS attacks since the start of the war at a variety of targets seen as opposed to Moscow. is a company that tracks VPNs and proxy services worldwide. “And at least two of them explained that Stark offered them free VPN services that they were reselling.”

Security Affairs
DECEMBER 5, 2019
Researchers discovered a vulnerability tracked as CVE-2019-14899 that can be exploited to hijack active TCP connections in a VPN tunnel. The experts explained that in this way, it is possible to hijack active connections within the VPN tunnel. SecurityAffairs – CVE-2019-14899 , hacking). Pierluigi Paganini.

Security Affairs
SEPTEMBER 1, 2020
Iran-linked APT group Pioneer Kitten is now trying to monetize its efforts by selling access to some of the networks it has hacked to other hackers. Iran-linked APT group Pioneer Kitten, also known as Fox Kitten or Parisite, is now trying to monetize its efforts by selling access to some of the networks it has hacked to other hackers.
Krebs on Security
JUNE 15, 2023
” When security experts began raising the alarm about a possible zero-day in Barracuda’s products, the Chinese hacking group altered their tactics, techniques and procedures (TTPs) in response to Barracuda’s efforts to contain and remediate the incident, Mandiant found. “Patch your #Fortigate.” ”

Krebs on Security
FEBRUARY 10, 2021
Many facilities have not separated operational technology (the bits that control the switches and levers) from safety systems that might detect and alert on intrusions or potentially dangerous changes. “There’s no business case for hacking these types of systems. Information sharing is broken.”
Security Affairs
AUGUST 25, 2023
Microsoft has not observed The group has been active since mid-2021, it focuses on government agencies and education, critical manufacturing, and information technology organizations in Taiwan. The state sponsored hackers also uses the VPN access to scan for vulnerabilities in targeted organizations. ” continues the report.

Security Affairs
MAY 30, 2024
Since 2011, Wang and his co-conspirators had been distributing malware through malicious VPN applications, including MaskVPN, DewVPN, PaladinVPN, ProxyGate, ShieldVPN, and ShineVPN. The FBI has published information at fbi.gov/911S5 to help identify and remove 911 S5’s VPN applications from your devices or machines.

SC Magazine
APRIL 15, 2021
authorities claim assisted Russian intelligence in hacking and election interference schemes. The Department of the Treasury moved quickly to leverage those new authorities, announcing the same day that six Russian technology and cybersecurity organizations would be subject to sanction.
Krebs on Security
APRIL 20, 2023
3CX hired incident response firm Mandiant , which released a report on Wednesday that said the compromise began in 2022 when a 3CX employee installed a malware-laced software package distributed via an earlier software supply chain compromise that began with a tampered installer for X_TRADER , a software package provided by Trading Technologies.

Krebs on Security
JULY 18, 2022
911 says its network is made up entirely of users who voluntarily install its “free VPN” software. In this scenario, users indeed get to use a free VPN service, but they are often unaware that doing so will turn their computer into a proxy that lets others use their Internet address to transact online. “The 911[.]re

Malwarebytes
DECEMBER 7, 2021
Microsoft has taken control of 42 web domains that a hacking group was using to try to breach its targets. Sadly, any setback to the Chinese hacking group or others will likely be temporary as the hackers will find and build new infrastructure to use in forthcoming attacks. An overview of Chinese hacking groups and their aliases.

Krebs on Security
AUGUST 19, 2020
But one increasingly brazen group of crooks is taking your standard phishing attack to the next level, marketing a voice phishing service that uses a combination of one-on-one phone calls and custom phishing sites to steal VPN credentials from employees. SCHOOL OF HACKS. The employee phishing page bofaticket[.]com. Image: urlscan.io.
Security Affairs
FEBRUARY 4, 2024
Clorox estimates the costs of the August cyberattack will exceed $49 Million Mastodon fixed a flaw that can allow the takeover of any account Iranian hackers breached Albania’s Institute of Statistics (INSTAT) Operation Synergia led to the arrest of 31 individuals Ex CIA employee Joshua Adam Schulte sentenced to 40 years in prison Cloudflare breached (..)

Malwarebytes
DECEMBER 7, 2021
Microsoft has taken control of 42 web domains that a hacking group was using to try to breach its targets. Sadly, any setback to the Chinese hacking group or others will likely be temporary as the hackers will find and build new infrastructure to use in forthcoming attacks. An overview of Chinese hacking groups and their aliases.

Daniel Miessler
SEPTEMBER 27, 2020
Example 2: Using a VPN. A lot of people are confused about VPNs. If you log in at the end website you’ve identified yourself to them, regardless of VPN. VPNs encrypt the traffic between you and some endpoint on the internet, which is where your VPN is based. Super Hackers Trying to Hack You.
Security Affairs
SEPTEMBER 10, 2023
Get tips and tricks Norway court rules against Facebook owner Meta in privacy case Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, newsletter ) The post Security Affairs newsletter Round 436 by Pierluigi Paganini – International edition appeared first on Security Affairs.
Krebs on Security
APRIL 22, 2022
The logs indicate LAPSUS$ had exactly zero problems buying, stealing or sweet-talking their way into employee accounts at companies they wanted to hack. The LAPSUS$ group had a laugh at this screenshot posted by their leader, White, which shows him reading a T-Mobile news alert about their hack into Samsung.

Adam Levin
NOVEMBER 15, 2019
News that Virtual Private Network ( VPN ) provider NordVPN was breached spread quickly. While the breach of a major VPN service is newsworthy, this one wasn’t particularly. But one of the watchwords of good cyber hygiene, a VPN, was breached. Who Is Using VPNs? The incident put NordVPN in the hot seat.

Security Affairs
JANUARY 19, 2024
On January, 16, 2023, the University K-State announced it was experiencing a disruption to certain network systems, including VPN, K-State Today emails, and videos on Canvas, or Mediasite. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, KSU)
Security Affairs
MAY 24, 2024
In this advisory, I aim to explore how implementing a specific security technological combination (TLS and DDNS) negatively influences the overall security, inadvertently creating opportunities for attackers to exploit weaknesses on a massive scale. For instance, suppose firewall manufacturer ACME Inc.
Security Affairs
FEBRUARY 8, 2024
In the most recent campaign, the group targeted organizations in the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – Hacking, Volt Typhoon)

The Last Watchdog
NOVEMBER 11, 2020
I had a chance to discuss this seminal transition with George Avetisov, co-founder and chief executive officer of HYPR , a Manhattan-based supplier of advanced authentication technologies. This is a type of advanced, brute-force hacking that leverages automation. Here are a few big takeaways. The reason: credential stuffing.

SC Magazine
MARCH 1, 2021
In response, criminal and state-backed hacking groups stepped up their own exploitation of the technology as well. A recent report from Zscaler found that VPNs are still overwhelmingly popular: 93% of companies surveyed reported that they have used them in some capacity.

The Last Watchdog
MARCH 6, 2021
Technology advancements have made it relatively easy for many employees to carry out their regular job duties from the comfort of their home. Related: Poll confirms rise of Covid 19-related hacks. Many people use a virtual private network (VPN) to bypass geographic restrictions on streaming sites or other location-specific content.

Security Affairs
JANUARY 24, 2024
Tietoevry is a Finnish multinational information technology (IT) and consulting company that provides managed services and cloud hosting for the enterprise. The ransomware attack reported in late 2023, targeted organizations’ networks using poorly secured VPN gateway on Cisco ASA or FTD devices.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content