How to Secure WiFi
Quick Heal Antivirus
OCTOBER 15, 2023
It’s important to secure your WiFi connection to prevent unauthorized access to your computer files and Internet activity. The post How to Secure WiFi appeared first on Quick Heal Blog.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 how-to-secure-wifi
how-to-secure-wifi 
Quick Heal Antivirus
OCTOBER 15, 2023
It’s important to secure your WiFi connection to prevent unauthorized access to your computer files and Internet activity. The post How to Secure WiFi appeared first on Quick Heal Blog.

SiteLock
AUGUST 27, 2021
As the digital workforce continues to expand, more people are dependent on public WiFi than ever before. However, that convenience can come with a potentially hefty price if you’re not focused on staying secure when connecting to 3rd party WiFi signals. Is Public WiFi Safe? Become Security Aware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
MAY 28, 2024
Decades later, the telecom industry figured out how to spread WiFi, GPS, BlueTooth and 5G signals over a wide bandwidth and then also added pseudo-random codes — to prevent tampering. Acohido is dedicated to fostering public awareness about how to make the Internet as private and secure as it ought to be. (LW

Troy Hunt
DECEMBER 11, 2022
For the first time in I don't know how long, I couldn't do this live. Turns out both cell and wifi in Lapland are, with the benefit of hindsight, exactly what you'd expect from a remote location in the Arctic circle. Is it feasible? Measurable? Does it even matter?)

Malwarebytes
JUNE 11, 2023
But data costs can be expensive, and out of your own home often the only WiFi available is public, passwordless and free. In security, we've been trained to carefully contemplate anything that's free, because, well, often when something is free, you turn out to be the product. In public, using shared WiFi carries risks.

Malwarebytes
MAY 13, 2021
We use WiFi to connect to the Internet, but what is it, and what does it stand for? How does it have such a catchy name, and why do we sometimes have a weak Internet connection with a strong WiFi signal and vice versa? What does WiFi mean? How does WiFi work? What is the difference between WiFi and Internet?

Security Affairs
JUNE 20, 2021
A new bug in iPhone can permanently break users’ WiFi by disabling it, the issue could be triggered by simply connecting to a rogue hotspot. The researcher Carl Schou discovered a new bug in iPhone that can permanently break users’ WiFi by disabling it, the issue could be triggered by simply connecting to a rogue hotspot. .

The Last Watchdog
MARCH 16, 2020
The idea is to divide the network up into segments, called subnetworks, to both optimize performance as well as strengthen security. Related: A use case for endpoint encryption At RSA 2020 in San Francisco recently, I learned about how something called “micro segmentation” is rapidly emerging as a viable security strategy.

Security Boulevard
APRIL 23, 2021
how to secure wifi for remote work, working from home securely, security home network, secure wifi network, remote work security risks, work from home security best practices. The post Keeping employee data safe – no matter where they may be appeared first on NuData Security.

Heimadal Security
OCTOBER 27, 2021
A researcher wanted to prove that a hacker could hijack a home network with ease by exploiting their lack of security, so he cracked 70% of a 5,000 WiFi network sample. This happened in Tel Aviv when he did the WiFi network cracking experiment, Tel Aviv being his hometown. How Did the Researcher Do His […].
Troy Hunt
MAY 6, 2022
not very good (I don't want to blame HA for this, it's a network-level issue) The wifi proximity sensor I installed in my mailbox is heading for "the drawer of broken dreams" (I spoke the Lars after recording and he agreed - it sucks!)

Malwarebytes
JULY 9, 2021
A researcher has found a way to disable the WiFi functionality on iPhones by getting them to join a WiFi hotspot with a weird name. Like a WiFi network name. All I would have to do is make you connect to a specific WiFi hotspot. So you can see why an WiFi network called %p%s%s%s%s%n might cause problems.
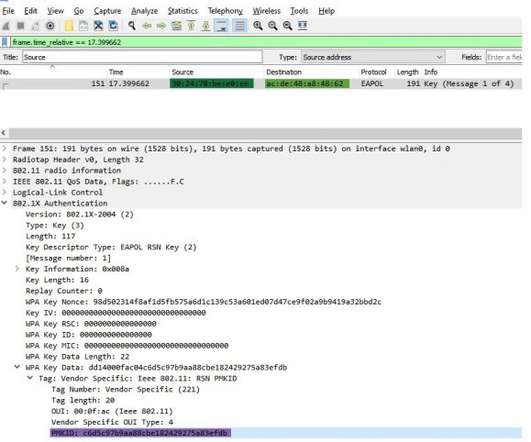
Security Affairs
OCTOBER 26, 2021
A researcher from the security firm CyberArk has managed to crack 70% of Tel Aviv’s Wifi Networks starting from a sample of 5,000 gathered WiFi. CyberArk security researcher Ido Hoorvitch demonstrated how it is possible to crack WiFi at scale by exploiting a vulnerability that allows retrieving a PMKID hash.

Troy Hunt
MARCH 12, 2020
I hate dodgy WiFi, hate it with a passion. I bought a security gateway to do DHCP, a couple of switches for all my connected things, 5 access points for my wireless things and a Cloud Key to control them all. I fixed the poor Wifi on my jet ski with their UniFi Mesh bits (I know, the most first world of problems).

Troy Hunt
JULY 13, 2021
It's still connecting to a mains socket in the roof and it's still connecting to your wifi, but it's a different brand. Plus, it's definitely added to our lives in terms of the things it enables us to do; see them in part 5 of my IoT unravelled blog series. With a different app. And you have to schedule it differently.
Adam Levin
NOVEMBER 29, 2019
State-sponsored cyber-warriors working from a secure command post? Why it matters: If you happen to be in an office, look around and take note of how many co-workers are using their workstations to charge their phones. And, generally speaking, the most affordable (and thus most commonly used) models have minimal built-in security.
Malwarebytes
AUGUST 20, 2023
Citrix Sharefile joins the list of actively exploited file sharing software Exchange Server security updates updated Catching up with WoofLocker, the most elaborate traffic redirection scheme to tech support scams Citrix NetScalers backdoored in widespread exploitation campaign Discord.io

Security Affairs
MAY 12, 2021
Security researcher discovered a series of flaws, collectively tracked as FragAttacks, that impact the WiFi devices sold for the past 24 years. Belgian security researcher Mathy Vanhoef disclosed the details of a multiple vulnerabilities, tracked as FragAttacks, that affect WiFi devices exposed them to remote attacks.

Security Affairs
MAY 2, 2021
A security duo has demonstrated how to hack a Tesla Model X’s and open the doors using a DJI Mavic 2 drone equipped with a WIFI dongle. s Ralf-Philipp Weinmann and Comsecuris GmbH’s Benedikt Schmotzle have discovered remote zero-click flaws in the vehicle and exploited them using a DJI Mavic 2 drone equipped with a WIFI dongle.
Security Affairs
JUNE 13, 2022
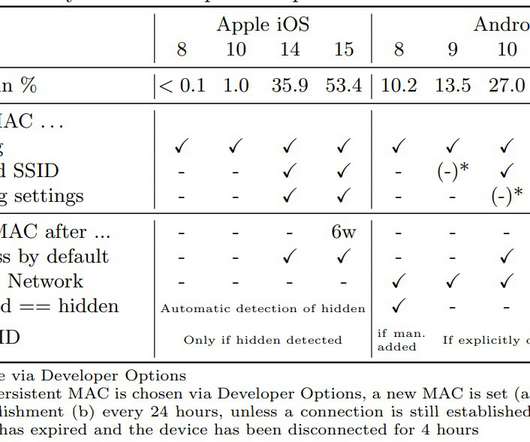
Researchers at the University of Hamburg demonstrated that WiFi connection probe requests expose users to track. A group of academics at the University of Hamburg (Germany) demonstrated that it is possible to use WiFi connection probe requests to identify and track devices and thereby their users. ” reads the research paper.

Malwarebytes
JUNE 7, 2021
The program is the latest example of yet another multibillion-dollar company rolling out significant changes without meaningfully notifying users beforehand, making it increasingly difficult for users to choose how their data is used, or how their products function. They dropped this on us,” Callas said in speaking to ThreatPost.

Malwarebytes
AUGUST 14, 2023
Ford learned from a supplier that a security researcher had discovered a vulnerability in the Wi-Fi software driver supplied for use in the SYNC 3 infotainment system available on some Ford and Lincoln vehicles. Ford has released information about a buffer overflow vulnerability in its SYNC 3 infotainment system.

Hot for Security
JUNE 15, 2021
Mobile security is often overlooked by many technology users, who dismiss the reality of security risks brought by careless interactions with the digital world. Mobile security is often overlooked by many technology users, who dismiss the reality of security risks brought by careless interactions with the digital world.

Adam Levin
DECEMBER 16, 2020
Here are 12 New Year Resolutions for a safer and more secure digital you in 2021: Think before you click that email link: 2020 was a record-breaking year for ransomware, malware, and phishing , and many, if not most of these attacks were launched with the click on a link in an email. That’s always the case when it comes to cybersecurity.

Troy Hunt
MARCH 13, 2020
Geez, where do you even begin given how the world has turned just in the last week? I spend a good quarter hour at the start of this video talking about what I'll be doing, namely getting on with business and running a bunch of public workshops remotely in conjunction with Scott Helme. it's remote, so you don't even need to be there ??)

Security Affairs
DECEMBER 10, 2018
The popular expert Jens ‘Atom’ Steube devised a new WiFi hack that allows cracking WiFi passwords of most modern routers. Jens ‘Atom’ Steube, the lead developer of the popular password-cracking tool Hashcat, has developed a new WiFi hacking technique that allows cracking WiFi passwords of most modern routers.

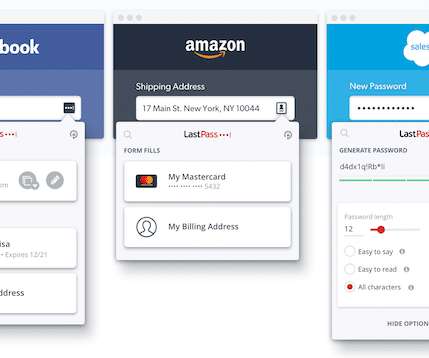
The Last Watchdog
MAY 24, 2022
Excising passwords as the security linchpin to digital services is long, long overdue. Security + efficiency. Password abuse at scale arose shortly after the decision got made in the 1990s to make shared secrets the basis for securing digital connections. Threat actors now routinely bypass these second-layer security gates.
Thales Cloud Protection & Licensing
JULY 13, 2022
why should security ?? As security professionals, we care about protecting ??and so even I know how to use them (or sometimes, but more about that later!). However, as always with digital communication, there are security concerns ??and to help keep your communications safe and your digital identity secure ??.
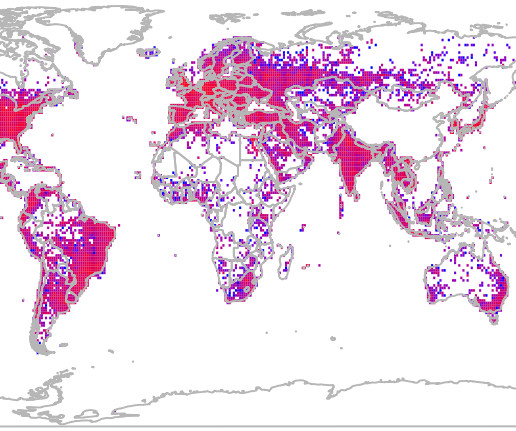
Krebs on Security
MAY 21, 2024
Apple and the satellite-based broadband service Starlink each recently took steps to address new research into the potential security and privacy implications of how their services geo-locate devices. Both record the Media Access Control (MAC) address that a Wi-FI access point uses, known as a Basic Service Set Identifier or BSSID.

Dark Reading
MAY 26, 2021
SPONSORED: Your home WiFi router may be screaming fast, but it's also a major point of vulnerability in this work-from-home era, says Charl van der Walt, head of security research at Orange Cyberdefense. And while Zero Trust offers some relief, he offers up some how-to advice to ensure it's properly deployed.

Troy Hunt
JULY 12, 2018
Even the government has been pushing to drive adoption of HTTPS for all sites, for example in this post by the National Cyber Security Centre in the UK : all websites should use HTTPS, even if they don't include private content, sign-in pages, or credit card details. Is it needed? Does it do any good? What's it actually protecting?

Krebs on Security
MAY 6, 2024
But researchers at Leviathan Security say they’ve discovered it’s possible to abuse an obscure feature built into the DHCP protocol so that other users on the local network are forced to connect to a rogue DHCP server. Image: Shutterstock. Image: Shutterstock.

Troy Hunt
OCTOBER 13, 2017
Part of this data was collected via an IoT device called the InnoTab which is a wifi connected tablet designed for young kids; think Fisher Price designing an iPad. then totally screwing up the security. So I gave VTech a suggestion: Hey @vtechtoys , how about put this warning on the box so it can be seen before purchasing?

Malwarebytes
JULY 12, 2021
Kaseya update delayed for security reasons. How one word can disable an iPhone ’s WiFi functionality. How to send an anonymous email. Source: The Register) Hackers use new trick to disable macro security warnings in malicious Office files. Game over: Apex Legends players locked out by protest message.

Security Affairs
FEBRUARY 6, 2020
Check Point experts discovered a high-severity flaw in Philips Hue Smart Light Bulbs that can be exploited to gain entry into a targeted WiFi network. Smart lightbulbs are managed over the air via WiFi protocol or ZigBee, a low bandwidth radio protocol. ZigBee is an IEEE 802.15.4-based ” reads the report published by CheckPoint.”Our

Security Affairs
SEPTEMBER 19, 2022
Researchers discovered two critical vulnerabilities (CVE–2022–36158 and CVE–2022–36159) in Flexlan devices that provide WiFi on airplanes. Researchers from Necrum Security Labs discovered a couple of critical vulnerabilities, tracked as CVE–2022–36158 and CVE–2022–36159, impacting the Contec Flexlan FXA3000 and FXA2000 series LAN devices.

Malwarebytes
MAY 10, 2021
Source: The Register) NSA advised to strengthen the security of operational technology (OT). Source: Tripwire) Tesla automobiles vulnerable to compromise over WiFi. The post A week in security (May 3 – 9) appeared first on Malwarebytes Labs. Other cybersecurity news: Cisco HyperFlex web interface has a critical flaw.

SiteLock
AUGUST 27, 2021
Whether you’re accessing a public WiFi network or working remotely, using a VPN (Virtual Private Network) helps limit your chances of having your data compromised. Learn more about online security by tuning into some of our previous episodes Is Your Website Certifiable? million credit cards and 1.2 million personal data records.

The Last Watchdog
SEPTEMBER 13, 2021
Surfshark wants to help individual citizens take very direct control of their online privacy and security. Thus, Surfshark has just become the first VPN provider to launch an antivirus solution as part of its all-in-one security bundle Surfshark One. You can’t know how good or how invested they are in their IT security.
Daniel Miessler
MAY 14, 2020
I wrote an article recently on how to secure your home network in three different tiers of protection. What follows is a set of basic security hygiene steps that will significantly reduce your risk online. These are the diet and exercise of the computer safety world. So, I decided to update the advice myself.

Security Affairs
APRIL 10, 2019
Security researchers discovered weaknesses in WPA3 that could be exploited to recover WiFi passwords by abusing timing or cache-based side-channel leaks. Security researchers discovered weaknesses in WPA3 that could be exploited to recover WiFi passwords by abusing timing or cache-based side-channel leaks.

Security Affairs
SEPTEMBER 11, 2019
Security experts have discovered that some models of D-Link and Comba WiFi routers leak their administrative login credentials in plaintext. Security researchers from Trustwave’s SpiderLabs have discovered several credential leaking vulnerabilities in some models of D-Link and Comba Telecom. are affected and likely models.
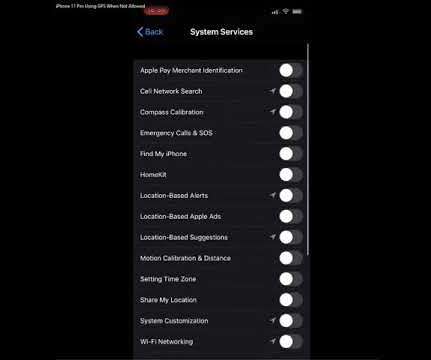
Krebs on Security
DECEMBER 4, 2019
x, sharing a video showing how the device still seeks the user’s location when each app and system service is set to “never” request location information (but with the main Location Data service still turned on). Apple says this is by design, but that response seems at odds with the company’s own privacy policy.

The Last Watchdog
JULY 12, 2018
However, details of the underlying hack , ferreted out and shared by researchers of the Insikt Group, an arm of the security research firm Recorded Future, are most welcomed. This raises wider questions about data security best practices, not to mention the wider contractor support community.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content