New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Troy Hunt
NOVEMBER 25, 2020
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. As with the rest of the IoT landscape, there's a lot of scope for improvement here and also just like the other IoT posts, it gets very complex for normal people very quickly.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
FEBRUARY 8, 2020
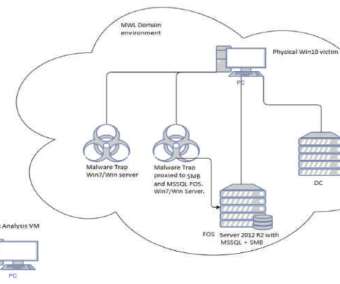
Hackers have infected with a piece of malware some IoT devices running Windows 7 designed by three of the world’s largest manufacturers. Security experts from TrapX reported that some IoT devices running Windows 7 have been infected with a piece of malware, is it a supply chain attack? Pierluigi Paganini.

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
As most of us know, IoT devices are on the rise in enterprise networks. According to McKinsey & Company , the proportion of organizations that use IoT products has grown from 13 percent in 2014 to 25 percent today. The issue is that these tens of billions of new devices will likely amplify the inherent security risks of IoT.

eSecurity Planet
JANUARY 22, 2021
billion Internet of Things (IoT) devices. As more information about IoT device vulnerabilities is published, the pressure on industry and government authorities to enhance security standards might be reaching a tipping point. government, standards will not apply to the IoT market at-large. Implications for IoT devices.
Notice Bored
JUNE 13, 2022
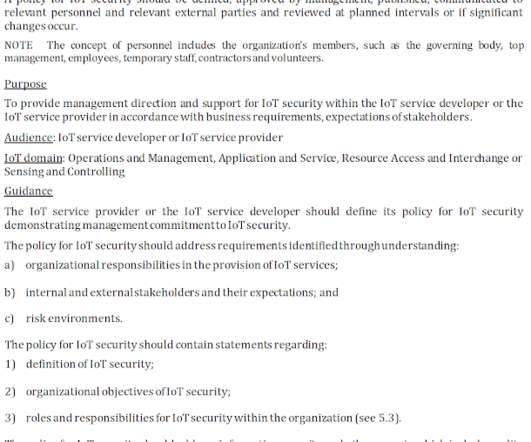
To celebrate the publication of ISO/IEC 27400:2022 today, we have slashed the price for our IoT security policy templates to just $10 each through SecAware.com. IoT policy is the first of the basic security controls shown on the 'risk-control spectrum' diagram above, and is Control-01 in the new standard.

Security Boulevard
JUNE 29, 2021
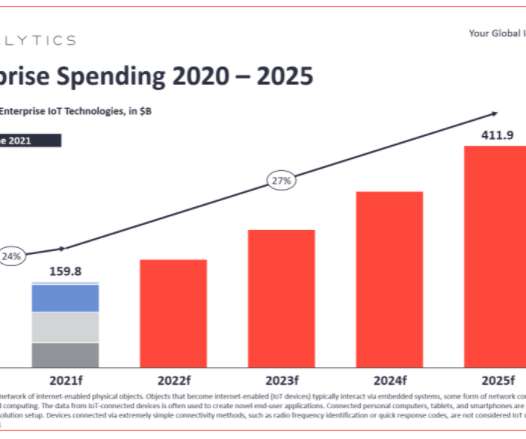
The IoT is maturing rapidly, and surveys show that global IoT spending will achieve a combined annual growth rate (CAGR) of 11.3% It offers promising benefits that are rapidly transforming a variety of industries, including manufacturing, health care, commercial buildings, smart homes, retail and energy.

Security Boulevard
SEPTEMBER 22, 2022
Attacks targeting cloud infrastructure are on the rise, according to the Netwrix 2022 Cloud Data Security Report, and the industry that is most vulnerable to attacks on the cloud is manufacturing. Slightly more than half of manufacturing companies experienced an attack on their cloud infrastructure in the past year.

SC Magazine
MAY 27, 2021
Today’s columnist, Matt Wyckhouse of Finite State, says to lock down IoT devices, manufacturers have to build security in from the start. billion IoT devices expected to hit the market globally by 2025. Manufacturers have experienced slower deal cycles and more demands for security reviews.
eSecurity Planet
NOVEMBER 1, 2021
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. Manufacturers will be required to adhere to the new cybersecurity safeguards when designing and producing these products. IoT market growth. IoT Security Neglected.
SecureWorld News
OCTOBER 13, 2022
consumers could have a set of cybersecurity labeling standards to protect their Internet of Things (IoT) devices as early as spring 2023 if the White House National Security Council has its way. Come up with roughly four solid cybersecurity standards that manufacturers of IoT devices can use to properly label cybersecurity risks to users.

Security Boulevard
JULY 12, 2022
Large-scale digital transformation initiatives over the last decade mean that cyber-physical systems are now intertwined with many manufacturing and industrial processes. There are also IoT devices connecting IT and OT environments, and smart devices get created and sold to…. Risks appeared first on Nuspire.

eSecurity Planet
AUGUST 9, 2021
A malicious advertising campaign originating out of Eastern Europe and operating since at least mid-June is targeting Internet of Things (IoT) devices connected to home networks, according to executives with GeoEdge, which offers ad security and quality solutions to online and mobile advertisers. Malvertising is Evolving.
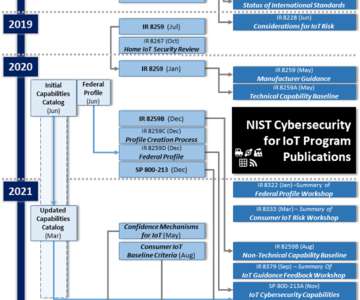
NSTIC
MAY 16, 2022
The NIST Cybersecurity for IoT program published Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks (NISTIR 8228) in June 2019, nearly 3 years ago. Since then, IoT technology has continued to develop and be adopted across sectors and markets.

Security Boulevard
MAY 30, 2022
Why Healthcare IoT Requires Strong Machine Identity Management. The healthcare industry has been leveraging IoT devices for years, steadily increasing its use in facilities and patient care. By 2027, the IoT in Healthcare market is expected to reach $290 billion , up from just $60 billion in 2019. brooke.crothers.

Heimadal Security
SEPTEMBER 19, 2022
Device manufacturers with poor cybersecurity policies and features risk paying fines if the new regulation is enacted. The post The European Union Prepares New Cybersecurity Regulations for IoT Devices appeared first on Heimdal Security Blog. What Is The Act Affecting? By introducing […].

The Hacker News
MARCH 8, 2022
As many as seven security vulnerabilities have been disclosed in PTC's Axeda software that could be weaponized to gain unauthorized access to medical and IoT devices.

Thales Cloud Protection & Licensing
FEBRUARY 16, 2021
Critical Success Factors to Widespread Deployment of IoT. Digital technology and connected IoT devices have proliferated across industries and into our daily lives. Finally, IoT devices are being used extensively in smart vehicles and home appliances to provide enhanced user experiences. Threat vectors on IoT.

Thales Cloud Protection & Licensing
JULY 15, 2021
Key Developments in IoT Security. Remember the early days of the emergence of Internet of Things (IoT) devices? Vulnerabilities have been discovered in many of these IoT devices. Ellen has extensive experience in cybersecurity, and specifically, the understanding of IoT risk. Thu, 07/15/2021 - 10:09.

Thales Cloud Protection & Licensing
OCTOBER 19, 2022
Manufacturing needs to adopt a Zero Trust approach to mitigate increased cyber threats. Long gone is the time when manufacturing systems and operations were siloed from the Internet and, therefore, were not a cybersecurity target. Thu, 10/20/2022 - 06:20. Survey’s key findings.
Pen Test Partners
OCTOBER 30, 2023
Risks and challenges The critical development in the medical device space is the growing number of devices that are connected to the internet. But what are the risks and challenges? But what are the risks and challenges? Security Risks: Medical devices connected to the internet are prime targets for cyberattacks.

Tech Republic Security
DECEMBER 21, 2016
The coming year will bring a large-scale IoT security breach, with fleet management, retail, manufacturing, and government at the biggest risk, according to experts.

Security Affairs
OCTOBER 13, 2020
The number of sensors and smart devices connected to the internet is exponentially rising, which are the 5 Major Vulnerabilities for IoT devices. If you take a look at the global market for IoT, you can easily spot the trend. IoT devices are exposed to cybersecurity vulnerabilities. IoT is a complicated concept.

CyberSecurity Insiders
JANUARY 28, 2022
As an increasing number of companies plan to implement 5G mobile networks on a large scale, organizations need to consider the security risks that the technology can pose. This article explores the possible ramifications that 5G could have for IoT security, along with some steps that enterprises can take to prepare for it.

Dark Reading
JULY 16, 2020
The only entities equipped to safeguard Internet of Things devices against risks are the IoT device manufacturers themselves.

Security Boulevard
FEBRUARY 9, 2024
Insight #1 From toasters to toothbrushes , the Internet of Things (IoT) continues to wreak havoc on the internet. As consumers, it's important to balance necessity with risk, just like with everything else. IoT manufacturers need to do better.

Thales Cloud Protection & Licensing
MAY 31, 2021
Use cases of secure IoT deployment. In our previous blog post , we discussed the challenges for securing IoT deployments, and how businesses and consumers benefit from authenticating and validating IoT software and firmware updates. Use case 3: Smart meter manufacturer. Tue, 06/01/2021 - 06:55.

The Last Watchdog
MAY 15, 2023
Related: Privacy rules for vehicles As vehicles continue to offer modern features such as app-to-car connectivity, remote control access, and driver assistance software, a huge risk lurks in the shadows. The risk of compromise is not just theoretical; there have been instances where vehicles were momentarily commandeered.

The Last Watchdog
NOVEMBER 15, 2018
Even as enterprises across the globe hustle to get their Internet of Things business models up and running, there is a sense of foreboding about a rising wave of IoT-related security exposures. And, in fact, IoT-related security incidents have already begun taking a toll at ill-prepared companies. Tiered performances.

SC Magazine
APRIL 30, 2021
The IoT security team at the Microsoft Security Response Center said vulnerabilities discovered affect at least 25 different products made by more than a dozen organizations, including Amazon, ARM, Google Cloud, Samsung, RedHat, Apache and others. A signage of Microsoft is seen on March 13, 2020 in New York City. Jeenah Moon/Getty Images).
eSecurity Planet
AUGUST 10, 2021
In a recent blog post , the researchers said the bad actors are looking to leverage a path traversal vulnerability that could affect millions of home routers and other Internet of Things (IoT) devices that use the same code base and are manufactured by at least 17 vendors. ” Should Updates Be Automated? ” Multiple Threats.

SecureWorld News
JUNE 14, 2022
I love the possibilities that Internet of Things (IoT) products bring to our lives. But I'm also very concerned about the associated security and privacy risks that IoT products inherently bring to those using them when controls do not exist or are not used to mitigate the risks. Consider just a few recent statistics.

The Last Watchdog
MARCH 4, 2020
However, to fully capture the benefits of an IoT-centric economy, a cauldron of privacy and security concerns must first be quelled. Related : The promise and pitfalls of IoT At the technology level, two fundamental things must get accomplished. More IoT standards are sure to come, but regulation will raise the bar only so high.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Three IoT Attack Avenues for 2019.

Thales Cloud Protection & Licensing
MARCH 10, 2021
What’s driving the security of IoT? There are so many reasons why manufacturers connect their products to the Internet, whether it’s industrial machines, medical devices, consumer goods or even cars. It’s also enabling manufacturers to respond faster to security vulnerabilities, market demand, and even natural disasters.

The Last Watchdog
FEBRUARY 21, 2024
Related: How decentralized IoT boosts decarbonization Yet, more so than ever, infusing trustworthiness into modern-day digital services has become mission critical for most businesses. If you factor in where we are in the world today with things like IoT, quantum computing and generative AI, we could be heading for a huge trust crisis.”

Malwarebytes
AUGUST 25, 2023
New research highlights another potential danger from IoT devices, with a popular make of smart light bulbs placing your Wi-Fi network password at risk. Researchers from the University of London and Universita di Catania produced a paper explaining the dangers of common IoT products.

SecureWorld News
SEPTEMBER 15, 2021
Now George Jetson’s reality is nearly our own, and Rosie the Robot is somewhat interchangeable with any number of IoT devices like Siri, Roomba, or Alexa. Today, organizations are also embracing a record number of Internet of Things (IoT) devices to accomplish objectives. Securing your IoT environment.

SiteLock
AUGUST 27, 2021
Simply defined, the internet of things (IoT) is a network of Internet-connected objects able to collect and exchange data. In today’s digital-driven world, IoT connects almost everything including homes, offices, and vehicles, allowing users the convenience of activating and operating nearly any device remotely. Think again.

SecureWorld News
FEBRUARY 17, 2024
This and many other vulnerabilities pose a significant risk, as they not only permit unauthorized access to individual devices but also enable hackers to infiltrate huge hospital networks and cause mass disruption through malicious software. Vulnerabilities in medical devices present significant risks, expanding the potential for breaches.

Security Boulevard
JUNE 28, 2022
IoT and Machine Identity Management in Financial Services. How is IoT changing the financial sector? IoT has already positively impacted the financial sector and will only continue to in the future. The most notable and well-documented example of investment in the IoT infrastructure has been by retail banks.

CyberSecurity Insiders
JANUARY 11, 2022
The 2021 ISG Provider Lens Manufacturing Industry Services – Global report finds the complex mix of legacy OT and newer, connected technologies such as industrial IoT and machine learning has forced manufacturers to add security extensions for protection against cyberattacks. STAMFORD, Conn.–(

eSecurity Planet
FEBRUARY 23, 2022
These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. Industries with very expensive operational technology (OT) and Internet of Things (IoT) devices, such as healthcare or industrial manufacturing, can be especially vulnerable.

SecureWorld News
FEBRUARY 18, 2024
While connected cars, stereo speakers, headphones, and even lightbulbs can be connected via Bluetooth, there are some risks associated with connecting to devices without security PINs (used during initial pairing) and ephemeral devices like rental cars. To begin, consider the simplest and most well-known risk.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content