Is Your Home or Small Business Built on Secure Foundations? Think Again…
Dark Reading
JULY 27, 2022
Did you know that the standard router relied upon in homes and by thousands of small businesses is the most frequently attacked IoT device?
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
JULY 27, 2022
Did you know that the standard router relied upon in homes and by thousands of small businesses is the most frequently attacked IoT device?

The Last Watchdog
SEPTEMBER 5, 2023
New government rules coupled with industry standards meant to give formal shape to the Internet of Things (IoT) are rapidly quickening around the globe. When it comes to IoT, we must arrive at specific rules of the road if we are to tap into the full potential of smart cities, autonomous transportation and advanced healthcare.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
SEPTEMBER 21, 2023
Introduction In today’s interconnected world, understanding the OWASP Top 10 IoT vulnerabilities is crucial, especially for small businesses striving to maintain a secure environment. However, with the myriad of benefits comes a host of vulnerabilities, … OWASP Top 10 IoT Vulnerabilities: How to Avoid Them!

Security Boulevard
SEPTEMBER 23, 2023
Introduction The convergence of the Internet of Things (IoT) and endpoint security has become a pivotal focal point for small businesses. These businesses are striving to safeguard their digital landscapes. The integration of IoT has revolutionized operational processes.

Security Boulevard
NOVEMBER 16, 2021
The post Examples of Large & Small Business Cyber Attacks: Fighting for Survival Against a New Wave of Cyber Criminals appeared first on Allot's Network Security & IoT Blog for CSPs & Enterprises. Just this month, according to Bleeping Computer, electronics retail giant MediaMarkt suffered.

Security Affairs
JANUARY 24, 2019
Cisco released security updates for several products, including SD-WAN, Webex, Firepower, IoT Field Network Director, Identity Services Engine, and Small Business routers. The tech giant addressed two serious issues in Cisco’s Small Business RV320 and RV325 routers. Pierluigi Paganini.

Tech Republic Security
JULY 19, 2017
Leon Kuperman, CTO of CUJO IoT Security, why your small business and home office needs a firewall, and why your ISP can't protect you from bad IPs, phishing links, and sites loaded with malware.

The Security Ledger
OCTOBER 28, 2021
IoT and OT (operation technology) deployments are growing and pose challenges to organizations that are still. Related Stories Spotlight: Automation Beckons as DevOps, IoT Drive PKI Explosion Spotlight: Operationalizing MDR with Pondurance CISO Dustin Hutchison Spotlight: Operationalizing MDR with Pondurance CISO Dustin Hutchinson.

CyberSecurity Insiders
JUNE 21, 2021
–( BUSINESS WIRE )– Luminous Cyber Corp. ( [link] ) today announced it has been awarded a Small Business Innovation Research (SBIR) grant from the U.S. Air Force Awards Small Business Innovation Research (SBIR) Funding to Luminous Cyber for Secure Geolocation Technology appeared first on Cybersecurity Insiders.

eSecurity Planet
FEBRUARY 2, 2024
Within the last couple of months, smart device vulnerabilities have been piling up, prompting businesses to protect their Internet of Things (IoT) environments. While Teslas aren’t the typical business IoT device, their connection to the internet makes them a cyber threat as much as your business’s other IoT technology.

eSecurity Planet
MAY 13, 2024
Small business owners tend to adopt Tinyproxy and also tend to use part-time IT resources which potentially threatens related supply chains with third-party risk. Tinyproxy provides a lightweight, open-source HTTP/S proxy adopted by individuals and small businesses for basic proxy functionality.

Malwarebytes
MAY 9, 2022
Over 50 countries sign the “Declaration for the Future of the Internet” Watch out for these 3 small business cybersecurity mistakes. The post A week in security (May 2 – 8) appeared first on Malwarebytes Labs.
Security Affairs
DECEMBER 5, 2021
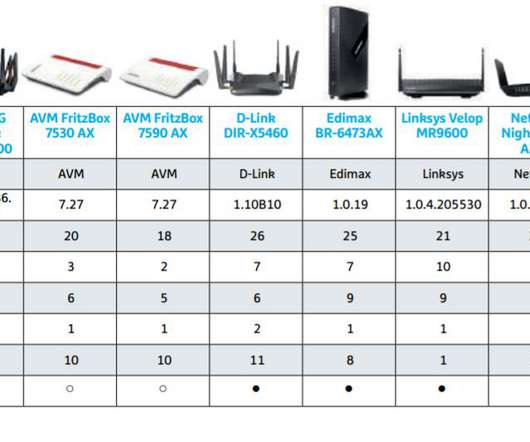
The researchers analyzed the network devices using IoT Inspector’s security platform, which checked for thousands of CVEs and security flaws. The test negatively exceeded all expectations for secure small business and home routers. “Some of the security issues were detected more than once. “The

The Last Watchdog
MARCH 13, 2019
The drivers of IoT-centric commerce appear to be unstoppable. Count on the wide deployment of IoT systems to continue at an accelerated rate. There are already more IoT devices than human beings on the planet, according to tech industry research firm Gartner. This time the stakes are too high. Security-by-design lacking.

SiteLock
AUGUST 27, 2021
Breaking news last week, the NIST (National Institute of Standards and Technology) Small Business Cybersecurity Act was signed into law. The bill will provide an avenue of resources and guidelines for small businesses to reduce their cybersecurity risks.

The Security Ledger
OCTOBER 14, 2022
But for all its bluster, Mirai and the IoT botnets that followed it were pretty simple creatures. The goal was to build a platform for future, external attacks – not probing the home and small business networks the routers fronted. New Rapidly-Spreading Hide and Seek IoT Botnet Identified by Bitdefender.

SecureWorld News
DECEMBER 8, 2021
Most organizations would struggle to do business without a network of Wi-Fi routers, and the security of those routers is essential. IoT Inspector , a European platform for IoT security analysis, and CHIP , a German IT magazine, recently discovered an alarming number of vulnerabilities in commonly used Wi-Fi routers.

CyberSecurity Insiders
SEPTEMBER 29, 2021
Cybersecurity asset management is a process that involves identifying the IT assets such as PCs, servers, IoT devices, and databases that are owned by an organization. Container monitoring is crucial for organizations as the IoT continues to expand. In fact, 60% of businesses that have experienced a data breach were small businesses.
Security Affairs
JANUARY 18, 2020
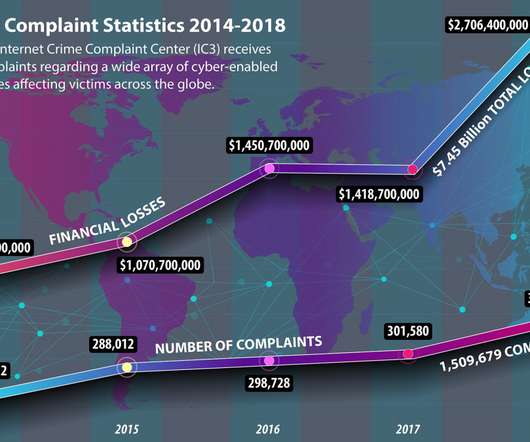
Which is the impact of cybercrime on small business? According to the 2019 Data Breach Investigations Report , 43% of all nefarious online activities impacted small businesses. Small businesses with fewer than 500 employees lose an average of $2.5 million on average. million due to security incidents.

Privacy and Cybersecurity Law
MAY 17, 2017
Sessions at the workshop are being livestreamed , and are exploring the extraterritorial application of the NIST framework, sector-specific requirements, and uses for small businesses. NIST’s focus on the IoT sector also comes as the IoT sector is coming under greater regulatory scrutiny in the US.
Security Boulevard
JULY 25, 2023
Now new findings reveal that AVrecon is the malware engine behind a 12-year-old service called SocksEscort, which rents hacked residential and small business devices to cybercriminals looking to hide their true location online. The post Who and What is Behind the Malware Proxy Service SocksEscort?

IT Security Guru
APRIL 6, 2021
Because larger businesses, with stronger and more mature security practices, have the defenses in place to keep bad actors from infiltrating their company while many small businesses do not. Small business owners are focussed on running their business with cybersecurity often a secondary concern.

Responsible Cyber
APRIL 8, 2020
IoT Opens Excessive Entry Points. The Internet of Things (IoT) is undeniably the future of technology. It is imperative for employers to now ensure that all IoT devices are set up correctly and no room for a network breach is left. Until a ransom is paid, businesses will be unable to access critical files and services.

Security Affairs
JANUARY 28, 2019
Cisco released security updates to address security flaws in several products including Small Business RV320/RV325 routers and hackers are already targeting them. The tech giant addressed two serious issues in Cisco’s Small Business RV320 and RV325 routers. SecurityAffairs – Cisco RV320/RV325 routers, IoT).

SiteLock
AUGUST 27, 2021
Recovering from an DDoS attack like this could cost a small business hundreds of thousands of dollars. As a small business owner, it’s critical that you know how to prevent a DDoS attack on your website. DDoS attacks are growing in both size and frequency. Why Is a DDoS Attack Destructive?
Webroot
AUGUST 2, 2021
Now with so many new victims of ransomware, businesses are turning to cyber security experts and asking why they’re a target. Small businesses fall victim to ransomware because of misconfigured systems, lack of proper security and human error. But the truth is there are only so many Fortune 500 companies to prey on.

Security Boulevard
MARCH 6, 2024
Even if employees’ devices are secure, the people and IoT devices that share the same home network (kids’ phones, printers, smart toasters, you name it) may not be protected. In fact, it is estimated that 60% of small businesses that are victims of a cyber attack go out of business within six months.

CyberSecurity Insiders
JANUARY 31, 2022
million smart and advanced meters in homes and small businesses by the end of 2020 , representing a 12% increase from the previous year. But, through the use of technology such as IoT eSIMs , providers can ensure that their smart meters remain connected 24/7 over a typical 10 to 15 year lifespan. In the UK alone, there were 23.6

Cisco Security
JULY 29, 2021
This commonly involves targeting vulnerabilities within software found on servers, laptops, and IoT devices. For example, a small business will likely not have a digital forensics expert on staff however, they should know who to call in if legal action needs to be taken due to a cyber related incident.

eSecurity Planet
MARCH 9, 2023
These complex multi-location entities often deploy local networks, virtual computing environments, cloud infrastructure, and a variety of devices that classify into the internet of things (IoT) and operational technology (OT) categories. Some even deploy applications, web servers, and containers. Free trials subscriptions are available.

Security Affairs
AUGUST 11, 2019
Russia-linked STRONTIUM APT targets IoT devices to hack corporate networks. Cisco addressed critical flaws in Cisco Small Business 220 Series Smart Switches. Crooks turn victims into money mules via confidence/romance scams. Expert publicly disclosed a zero-day vulnerability in KDE.
The Security Ledger
FEBRUARY 26, 2020
» Related Stories Spotlight Podcast: Building Resilience into the IoT with Rob Spiger Episode 176: Security Alarms in Census II Open Source Audit. Also: The New Face of Insider Threats with Code42 As Cyber Attacks Mount, Small Businesses seek Authentication Fix. Read the whole entry. »

Malwarebytes
MARCH 14, 2022
All these applied to Cisco’s Small Business RV160, RV260, RV340, and RV345 series routers by the way. Other interesting items on the list are some IoT vulnerabilities that got some fame in 2020 under the name Ripple20. In fact, only 5 vulnerabilities were patched in 2022. This brings me to the next thing that is remarkable.

Security Affairs
DECEMBER 1, 2020
However, the database has already been indexed on at least one popular IoT search engine, which means that there is almost no doubt that the data has been accessed and possibly downloaded by outside parties for potentially malicious purposes. What’s the impact of the Apodis Pharma leak?

Joseph Steinberg
APRIL 7, 2021
For years, in articles, lectures, and books I have discussed how the spread of IoT and AI technologies – both individually and together – are dramatically increasing the danger to human life posed by cyberattacks on healthcare facilities. Argus Cyber Security .

McAfee
OCTOBER 10, 2019
In Part I of the series, we explored IT security trends for 2019 and ways companies can protect themselves from IoT device vulnerability. In this joint project with Europol and AWS, it’s been an amazing journey to watch and even invest in helping protect businesses against ransomware.

Krebs on Security
OCTOBER 12, 2018
BK: Do you see any parallels between the challenges of securing the supply chain and the challenges of getting companies to secure Internet of Things (IoT) devices so that they don’t continue to become a national security threat for just about any critical infrastructure, such as with DDoS attacks like we’ve seen over the past few years?

Krebs on Security
JULY 25, 2023
Now new findings reveal that AVrecon is the malware engine behind a 12-year-old service called SocksEscort , which rents hacked residential and small business devices to cybercriminals looking to hide their true location online. Image: Lumen’s Black Lotus Labs.

ForAllSecure
JULY 13, 2021
A National Cyber Security Alliance reported that in a survey of 1,009 small businesses with 500 employees 10% went out of business; 25% had to file for bankruptcy; and 37% percent experienced financial loss. With the advent of IoT, as soon as the software is outdated, the device itself is considered disposable.

Security Affairs
APRIL 22, 2022
Small businesses are disproportionately impacted. As attacks become increasingly automated, it has become easier and more profitable for criminals to target small organizations. “We For example, what happens if a facility is damaged or even destroyed because of a cybersecurity incident targeting a connected IoT device?

eSecurity Planet
JUNE 30, 2023
External vulnerability scans are conducted based on the size of your organization, with different frequencies for small and large enterprises.

SC Magazine
MARCH 16, 2021
Finally, readying the business so it can take advantage of emerging technologies, like the cloud, 5G and internet of things (IoT), is definitely a priority — but it’s also important to never lose sight of the basics. How can cyber leaders work with corporate peers to win buy-in from c-suites and boards of directors?

SiteLock
AUGUST 27, 2021
With that, 43 percent of cyberattacks target small businesses. Advanced persistent threats (APTs) are on the rise, and new ways of invading business and personal networked systems are created every day. How real and prevalent are cyber threats?

The Last Watchdog
OCTOBER 19, 2022
The only way for digital innovation to achieve its full potential is if enterprises and small businesses alike embrace technologies and best practices that support agility, while at the same time choking off any unauthorized network access. The Internet of Things is a huge new platform for amazing innovation,” Hanna observes.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content