Apple Warns Users of Targeted Spyware Attacks – Here’s How to Stay Safe
Penetration Testing
APRIL 11, 2024
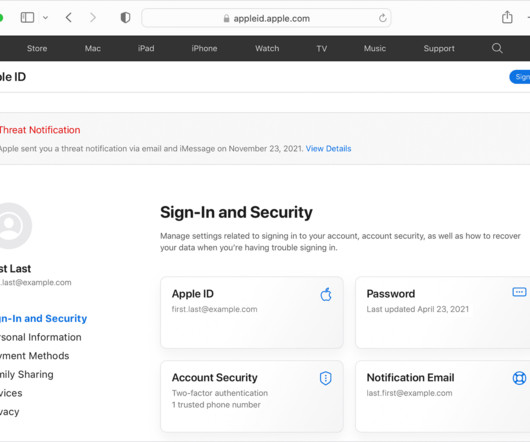
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Penetration Testing
APRIL 11, 2024
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.
Security Affairs
DECEMBER 21, 2023
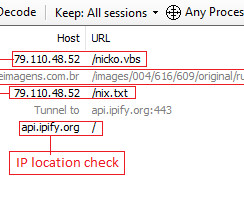
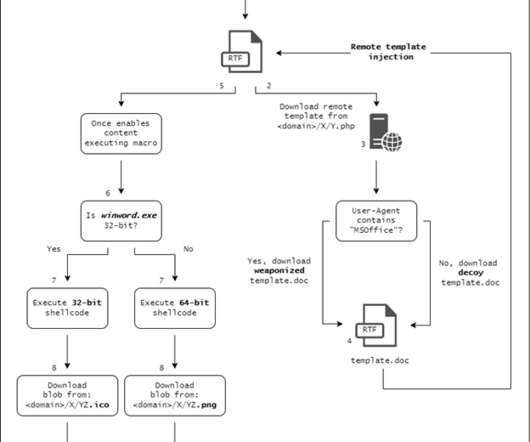
Threat actors are exploiting an old Microsoft Office vulnerability, tracked as CVE-2017-11882, to spread the Agent Tesla malware. Threat actors are exploiting an old Microsoft Office vulnerability, tracked as CVE-2017-11882 (CVSS score: 7.8), as part of phishing campaigns to spread the Agent Tesla malware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
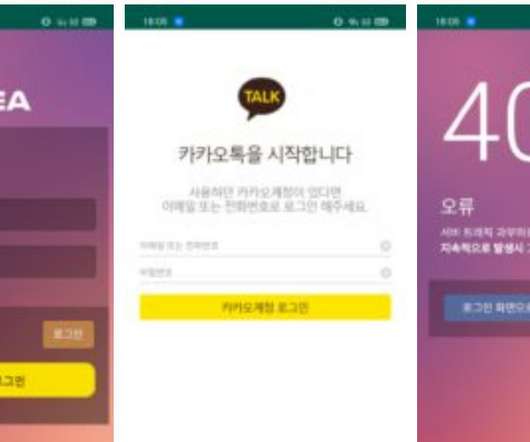
NOVEMBER 10, 2021
South Korean users have been targeted with a new sophisticated Android spyware, tracked as PhoneSpy, as part of an ongoing campaign. Researchers from Zimperium zLabs uncovered an ongoing campaign aimed at infecting the mobile phones of South Korean users with new sophisticated android spyware dubbed PhoneSpy. Zimperium concludes.

Schneier on Security
MAY 5, 2020
Interesting story of malware hidden in Google Apps. That's when Russian security firm Dr. Web found a sample of spyware in Google's app store that impersonated a downloader of graphic design software but in fact had the capability to steal contacts, call logs, and text messages from Android phones.
Security Boulevard
JUNE 22, 2022
It could be via virus malware, phishing, social engineering, fileless malware, etc. So, we’re here to talk about one such common tactic: Spyware. What is spyware and how does it work? The post What is Spyware and How to Protect Against it? The post What is Spyware and How to Protect Against it?

Heimadal Security
DECEMBER 14, 2021
Agent Tesla initially detected in late 2014, is a known spyware aimed at collecting sensitive data from a victim’s device, such as stored application credentials and keyboard inputs (keylogger). The post Agent Tesla Spyware Used in Phishing Campaign appeared first on Heimdal Security Blog.

Bleeping Computer
FEBRUARY 22, 2023
Threat actors are actively exploiting the popularity of OpenAI's ChatGPT AI tool to distribute Windows malware, infect Android devices with spyware, or direct unsuspecting victims to phishing pages. [.]

Malwarebytes
APRIL 28, 2021
Using a proven method of text messages about missed deliveries, an old player on the Android malware stage has returned for an encore. This time it seems to be very active, especially in the UK where Android users are being targeted by text messages containing a link to a particularly nasty piece of spyware called Flubot.
Security Affairs
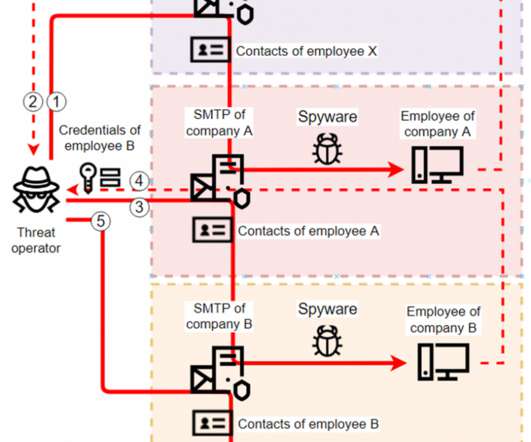
JANUARY 21, 2022
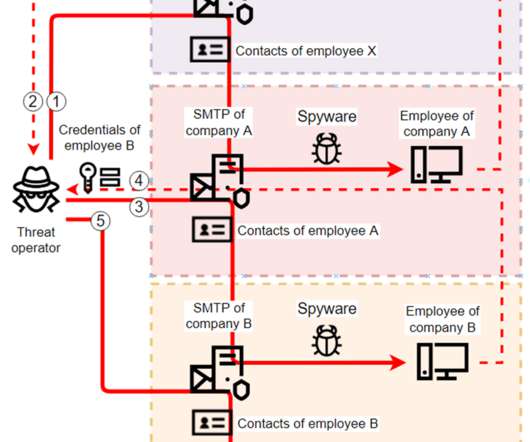
Researchers spotted several spyware campaigns targeting industrial enterprises to steal credentials and conduct financial fraud. Researchers from Kaspersky Lab have uncovered multiple spyware campaigns that target industrial firms to steal email account credentials and carry out fraudulent activities. ” continues the report.

SecureList
MARCH 19, 2024
By percentage of ICS computers on which spyware was blocked. Regions ranked by percentage of ICS computers on which spyware was blocked, H2 2023 By percentage of ICS computers on which worms were blocked. One of the two regions where the percentage of ICS computers on which spyware was blocked rose in the six-month period.

CyberSecurity Insiders
JANUARY 5, 2022
Hackers are found inducing Zloader Malware into Windows machines since November last year and reports are in that the malicious software tool has already targeted over 2,848 victims from 111 countries so far. Highly placed sources say that the malware has been distributed via phishing campaign by a cyber threat group named MalSmoke.
Security Affairs
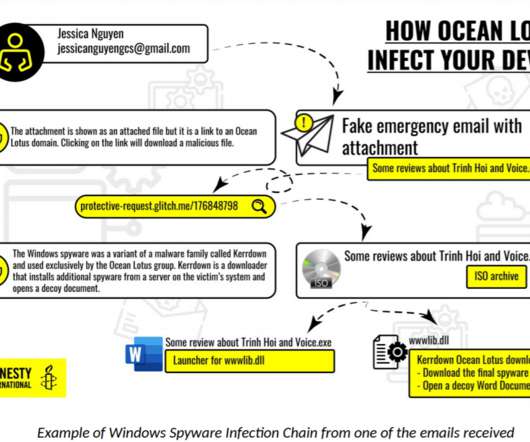
FEBRUARY 24, 2021
The threat actors used by spyware to take over the target systems, spy on the victims, and exfiltrate data. ” The attack chain begins with spear-phishing messages that include a link to an alleged important document to download. The link points to files containing spyware that could infect both Mac OS or Windows systems.

SecureWorld News
NOVEMBER 2, 2022
government threat report , released this morning and titled "Rise in Mobile Phishing Credential Theft Targeting Public Sector," includes these key findings: Nearly 50% of state and local government employees are running outdated Android operating systems, exposing them to hundreds of device vulnerabilities.
Security Boulevard
MARCH 3, 2021
Another reason is that social engineering lures may be expertly crafted by the attacker after they have been monitoring a victim’s activity for some time, resulting in more effective phishing campaigns with serious security implications. Continue reading Trojan Spyware and BEC Attacks at Sucuri Blog.
Security Affairs
JULY 21, 2021
Check Point Research (CPR) experts have spotted a cheap malware, dubbed XLoader variant, which was upgraded to target both Windows and macOS PCs. XLoader is a very cheap malware strain that is based on the popular Formbook Windows malware. Thus, a “Malware-as-a-Service” scheme is used. ” continues the report.
Security Affairs
MARCH 10, 2024
Judge ordered NSO Group to hand over the Pegasus spyware code to WhatsApp Cybercrime BlackCat Ransomware Affiliate TTPs American Express credit cards EXPOSED in third-party vendor data breach – account numbers and names among details accessed in hack LockBit 3.0’S

Malwarebytes
FEBRUARY 16, 2021
Today, we are showing readers just what that evolution looked like, in our State of Malware 2021 report. This report provides our most comprehensive analysis of last year’s malware trends, with breakdowns by malware category, malware type, operating system, region, industry, and more.

Identity IQ
APRIL 29, 2021
What is Malware? . Malware is an umbrella term used to describe any malicious software designed to harm, exploit, or extract sensitive data from a system, device, or network. Why do Cybercriminals Use Malware? How does Malware Spread? Types of Malware. Warning Signs Cour computer Is Infected by Malware.
Security Affairs
AUGUST 21, 2022
The Donot Team threat actor, aka APT-C-35 , has added new capabilities to its Jaca Windows malware framework. In the past, the Donot Team spyware was found in attacks outside of South Asia. To understand which modules are used in the current infection, the malware communicates with another C2 server.” Pierluigi Paganini.
Security Affairs
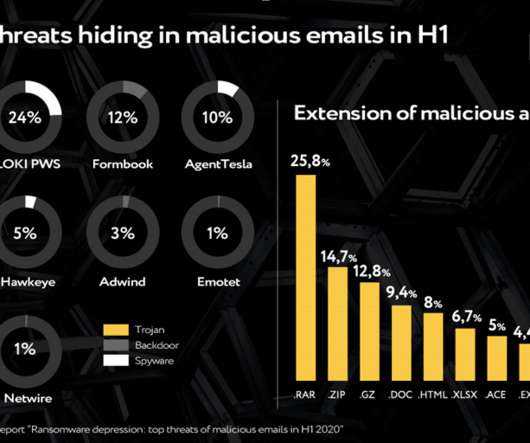
SEPTEMBER 18, 2020
Web-phishing targeting various online services almost doubled during the COVID-19 pandemic , it accounted for 46 percent of the total number of fake web pages. Downloaders , intended for the installation of additional malware,and backdoors , granting cybercriminals remote access to victims’ computers, also made it to top-3.

The Hacker News
JULY 31, 2023
Organizations in Italy are the target of a new phishing campaign that leverages a new strain of malware called WikiLoader with an ultimate aim to install a banking trojan, stealer, and spyware called Ursnif (aka Gozi). "It The malware uses multiple mechanisms to evade
Security Affairs
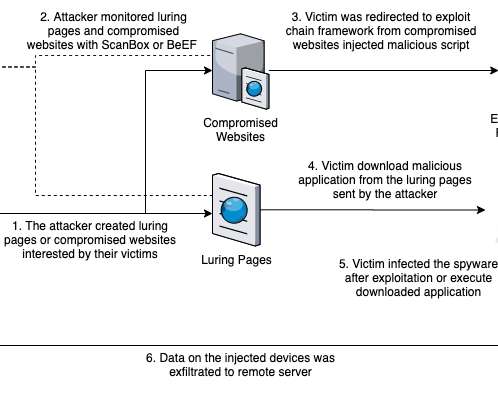
JUNE 15, 2020
The Earth Empusa threat group is distributing new Android spyware, dubbed ActionSpy, through watering hole attacks to targets Turkic minority group. Attackers injected the malicious code to deploy the spyware in websites, some of them were actually fake. The server, in turn, may send some commands to the compromised device.

SecureList
FEBRUARY 16, 2023
Short-lived phishing sites often offered to see the premieres before the eagerly awaited movie or television show was scheduled to hit the screen. At the beginning of that year, we still observed phishing attacks that used the themes of infection and prevention as the bait.
Security Affairs
APRIL 21, 2024
carmaker with phishing attacks Law enforcement operation dismantled phishing-as-a-service platform LabHost Previously unknown Kapeka backdoor linked to Russian Sandworm APT Cisco warns of a command injection escalation flaw in its IMC. Automotive Industry Chinese Organized Crime’s Latest U.S.
SecureList
FEBRUARY 15, 2021
Agentb malware family. The Kaspersky Anti-Phishing component blocked 434,898,635 attempts at accessing scam sites. The most frequent targets of phishing attacks were online stores (18.12 The contact phone trick was heavily used both in email messages and on phishing pages. Trends of the year.
Security Affairs
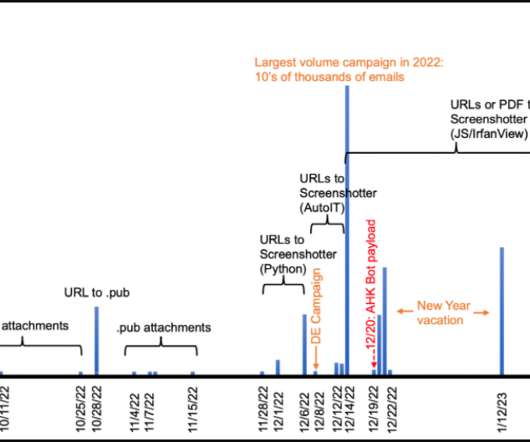
FEBRUARY 10, 2023
The TA886 hacking group targets organizations in the United States and Germany with new spyware tracked as Screenshotter. A recently discovered threat actor, tracked as TA886 by security firm Proofpoint, is targeting organizations in the United States and Germany with new malware dubbed Screenshotter.
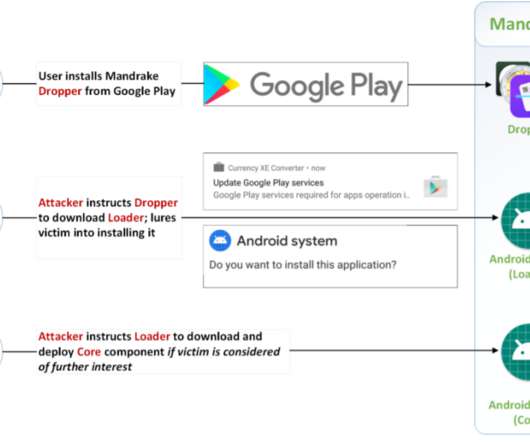
Security Affairs
MAY 18, 2020
Security experts discovered a highly sophisticated Android spyware platform, dubbed Mandrake, that remained undetected for four years. Researchers from Bitdefender discovered a high-sophisticated Android spyware platform dubbed Mandrake, it was involved in highly targeted attacks against specific devices. ” continues the report.

SecureList
OCTOBER 5, 2022
We are often asked how targets are infected with malware. Our answer is nearly always the same: (spear) phishing. Last month, we focused on infection methods used in various malware campaigns: methods that we do not see used very often. It used cracked games and software as bait to trick users into installing malware.

Security Affairs
JUNE 4, 2023
Xplain hack impacted the Swiss cantonal police and Fedpol Zyxel published guidance for protecting devices from ongoing attacks Kimsuky APT poses as journalists and broadcast writers in its attacks New Linux Ransomware BlackSuit is similar to Royal ransomware CISA adds Progress MOVEit Transfer zero-day to its Known Exploited Vulnerabilities catalog (..)
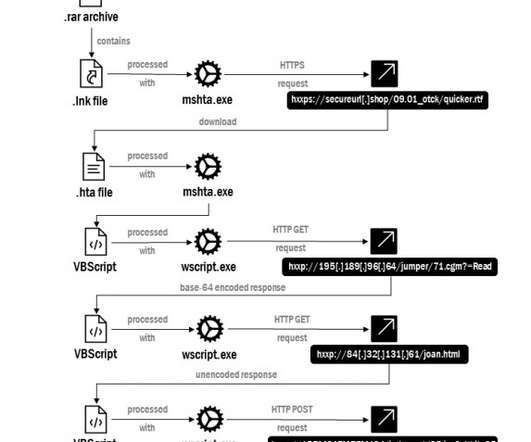
Security Affairs
FEBRUARY 3, 2023
Russia-linked threat actor Gamaredon employed new spyware in cyber attacks aimed at public authorities and critical information infrastructure in Ukraine. The attack chain starts with spear-phishing messages with a.RAR attachment named “12-1-125_09.01.2023.” lnk” (“Request of the Security Service of Ukraine 12-1-125 dated 09.01.2023.lnk”).

Adam Levin
NOVEMBER 26, 2019
Using the information and accesses exposed, they could create effective phishing campaigns, or target companies with various forms of malicious software attacks: malware, spyware, ransomware, and more,” the article continued.
Security Affairs
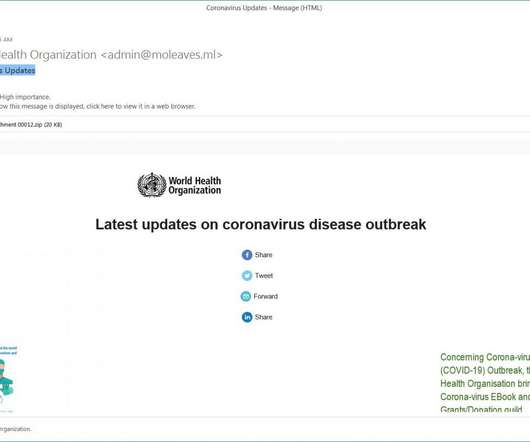
MARCH 8, 2020
Experts uncovered a new Coronavirus (COVID-19 ) -themed campaign that is distributing a malware downloader that delivers the FormBook information-stealing Trojan. Experts at MalwareHunterTeam uncovered a new malspam campaign exploiting the fear in the Coronavirus (COVID-19) to deliver malware. states the analysis published by FireEye.

SecureList
DECEMBER 16, 2021
In June 2021, Kaspersky ICS CERT experts identified malware whose loader has some similarities to the Manuscrypt malware, which is part of the Lazarus APT group’s arsenal. We dubbed the newly-identified malware PseudoManuscrypt. In 2020, the group used Manuscrypt in attacks on defense enterprises in different countries.

eSecurity Planet
AUGUST 11, 2021
As users have increasingly moved from desktop operating systems to mobile devices as their primary form of computing, cyber attackers have taken notice and malware has followed. Mobile malware statistics. More than 3 million of those attacks represented new types of malware. Types of mobile malware. ransomware?

Zero Day
MARCH 24, 2022
The malware is being spread through an interesting phishing tactic.

Security Affairs
JULY 18, 2019
Intezer spotted a new piece of Linux malware dubbed EvilGnome because it disguises as a Gnome extension. The researchers attribute the spyware to the Russia-linked and Gamaredon Group. The attack starts with spear-phishing emails containing weaponized attachments, the malware is distributed via Russian hosting providers.

SecureWorld News
JULY 27, 2023
A new study from Uptycs has uncovered an increase in the distribution of information stealing malware. Newly discovered stealer families include modules that specifically steal logs from MFA applications, like the Rhadamanthys malware. Examining the dark web reveals that infostealer malware has become increasingly widespread.

SecureList
SEPTEMBER 8, 2022
Among global regions, Africa ranked highest based on the percentage of ICS computers on which malware was blocked when removable media was connected. Regions ranked by percentage of ICS computers on which malware was blocked when removable media was connected, H1 2022. Diversity of malware. Industry specifics. of ICS computers.
SecureList
FEBRUARY 9, 2022
The most common malware family found in attachments were Agensla Trojans. Our Anti-Phishing system blocked 253 365 212 phishing links. Safe Messaging blocked 341 954 attempts to follow phishing links in messengers. Hurry up and lose your account: phishing in the corporate sector. Trends of the year.

SecureWorld News
AUGUST 8, 2022
Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) released a joint Cybersecurity Advisory (CSA) providing details on the top malware strains of 2021. The top malware strains in 2021 included remote access Trojans (RATs), banking Trojans, information stealers, and ransomware.
SecureList
JANUARY 19, 2022
Kaspersky ICS CERT has uncovered a number of spyware campaigns targeting industrial enterprises. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content