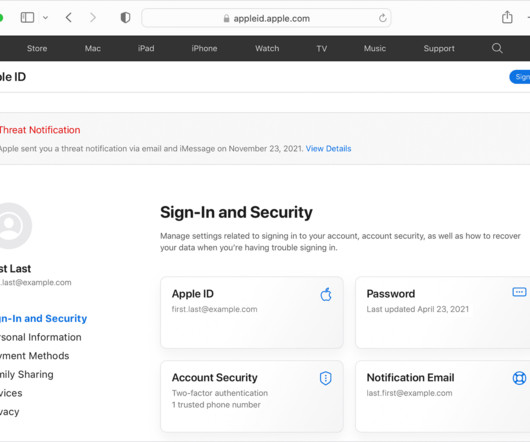
Apple Warns Users of Targeted Spyware Attacks – Here’s How to Stay Safe
Penetration Testing
APRIL 11, 2024
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Penetration Testing
APRIL 11, 2024
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.

Malwarebytes
FEBRUARY 16, 2021
Today, we are showing readers just what that evolution looked like, in our State of Malware 2021 report. This report provides our most comprehensive analysis of last year’s malware trends, with breakdowns by malware category, malware type, operating system, region, industry, and more.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureList
FEBRUARY 16, 2023
Short-lived phishing sites often offered to see the premieres before the eagerly awaited movie or television show was scheduled to hit the screen. Thus, during the World Cup a brand-new scam appeared: it offered users to win a newly released iPhone 14 for predicting match outcomes.

Identity IQ
APRIL 29, 2021
What is Malware? . Malware is an umbrella term used to describe any malicious software designed to harm, exploit, or extract sensitive data from a system, device, or network. Why do Cybercriminals Use Malware? How does Malware Spread? Types of Malware. Warning Signs Cour computer Is Infected by Malware.
SecureList
FEBRUARY 15, 2021
Agentb malware family. The Kaspersky Anti-Phishing component blocked 434,898,635 attempts at accessing scam sites. The most frequent targets of phishing attacks were online stores (18.12 The contact phone trick was heavily used both in email messages and on phishing pages. Trends of the year.
Security Affairs
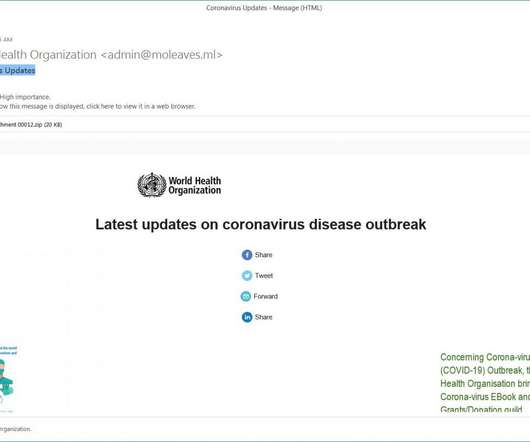
MARCH 8, 2020
Experts uncovered a new Coronavirus (COVID-19 ) -themed campaign that is distributing a malware downloader that delivers the FormBook information-stealing Trojan. Experts at MalwareHunterTeam uncovered a new malspam campaign exploiting the fear in the Coronavirus (COVID-19) to deliver malware. states the analysis published by FireEye.

BH Consulting
OCTOBER 6, 2022
Is it just us, or is phishing everywhere right now? Banks and insurance companies are telling customers to be wary of scam messages. Social engineering techniques, such as phishing, target not the systems but the people using them. Social engineering techniques, such as phishing, target not the systems but the people using them.
SecureList
FEBRUARY 9, 2022
The most common malware family found in attachments were Agensla Trojans. Our Anti-Phishing system blocked 253 365 212 phishing links. Safe Messaging blocked 341 954 attempts to follow phishing links in messengers. Hurry up and lose your account: phishing in the corporate sector. Trends of the year.

Webroot
OCTOBER 25, 2021
Even strong security can’t prevent an account from being hacked if account credentials are stolen in a phishing attack, one of the most common causes of identity theft. In 2020, phishing scams spiked by 510 percent between January and February alone. Web-borne malware remains widespread.

Identity IQ
FEBRUARY 21, 2023
Most times, spam emails contain malware , which can compromise your devices connected to the email. Trojan Horses A trojan horse is a malware that is disguised to appear as a legitimate program. Unfortunately, many individuals who have methods of verifying emails can also fall victim to this malware. This is a trap.

eSecurity Planet
JUNE 16, 2022
billion malware attacks were identified by the report. Cisco Umbrella , analyzing the threat environment for 2022, found that 86% of organizations experienced phishing, 69% experienced unsolicited crypto mining, 50% were affected by ransomware, and 48% experienced some form of information-stealing malware. Crimeware and spyware.

SecureList
MARCH 1, 2021
The word “covid” in various combinations was typically used in the names of packages hiding spyware and banking Trojans, adware or Trojan droppers. The mobile malware Trojan-Ransom.AndroidOS.Agent.aq Last year was notable for both malware and adware, the two very close in terms of capabilities. More on that later.

IT Security Guru
FEBRUARY 13, 2023
With so many well known banking sites falling short when it comes to blocking fraudsters, cybersecurity experts at VPNOverview have compiled a list of 12 safety tips to keep your money safe from malware and phishing scams. What are the possible dangers of online banking?

Hot for Security
JUNE 14, 2021
Most security threats faced by regular users arrive via the Internet, whether it’s a malicious app or a rigged website , a scam delivered through the user’s social media channels, or a phishing scheme carried out via email or SMS. In many cases, no malware is needed to compromise this data. Platform-agnostic threats.

Malwarebytes
OCTOBER 26, 2021
We talked to members of our Malware Removal Support team and asked them what kind of problems they get asked to solve for our customers. Some people get so convinced they have spyware on their system that they contact our support team to help them get rid of it. Social media and scams. More Facebook concerns.

Identity IQ
FEBRUARY 18, 2021
A common example is phishing. Phishing is a type of social engineering attack whereby hackers send fictitious emails or other communication , from what appears to be a trusted company, to induce victims to reveal personal information such as passwords, usernames or payment details. Anti-Malware Software. Public Wi-Fi Networks.

Malwarebytes
JULY 11, 2022
Chrome patches ANOTHER zero-day vulnerability Cloud-based malware is on the rise. How can you secure your business?

Hot for Security
JUNE 15, 2021
Given the portability and myriad of functionalities, mobile devices are highly susceptible to cyber threats, including malware, spyware and phishing attempts that may compromise that precious piece of tech we keep in our pocket and any information stored on it. Avoid smishing and phishing attacks.

Malwarebytes
SEPTEMBER 27, 2021
Uber scam lures victims with alert from a real Uber number Teaching cybersecurity skills to special needs children with Alana Robinson: Lock and Code S02E18. Last week on Malwarebytes Labs. Other cybersecurity news.

Security Affairs
APRIL 24, 2022
If you want to also receive for free the newsletter with the international press subscribe here. T-Mobile confirms Lapsus$ had access its systems Are you using Java 15/16/17 or 18 in production? Patch them now!

Security Boulevard
MAY 3, 2021
Millions in the UK Targeted by Malware via a DHL Scam Text Message. Millions of UK citizens received a scam text message (aka smashing) which impersonated DHL in April. That link would attempt to install spyware called Flubot, malware designed to steal online banking data from Andriod devices. .

SecureList
MARCH 15, 2021
From targeted attacks to exploiting all things COVID-related, the biggest trends in spam and phishing. Phishing is still one of the most effective types of attacks because it exploits users’ emotions, particularly their fear and anxiety. A fake landing page for a mask advertised in a phishing email. Lessons learned.

SiteLock
AUGUST 27, 2021
Cyberattacks are often caused by malware, which is the umbrella term used to describe software created for malicious purposes. You may be most familiar with computer malware such as Trojan viruses and spyware, which can be used to retrieve sensitive data from a computer or even take control of the system.

SecureWorld News
APRIL 11, 2023
No charging station is safe, apparently, as the FBI is warning travelers looking to charge their devices in airports, hotels, and coffee shops that "juice jacking" is a thing—as bad actors are using public chargers and even free cables and charging plugs to infect phones and other devices with malware.

Identity IQ
MAY 7, 2021
Once they have access to an account with sufficient authority, cybercriminals can use that trusted email address to scam other companies into making fraudulent payments or just distribute malware en mass. Research by Verizon has shown that a third of all breaches in the past year involved phishing scams. The Bottom Line.

SecureList
NOVEMBER 22, 2022
Unlike common stealers, this malware gathered data that can be used to identify the victims, such as browsing histories, social networking account IDs and Wi-Fi networks. According to the freshest data on DeFi, every hour 15 newly deployed scams against smart contracts are detected.
Security Affairs
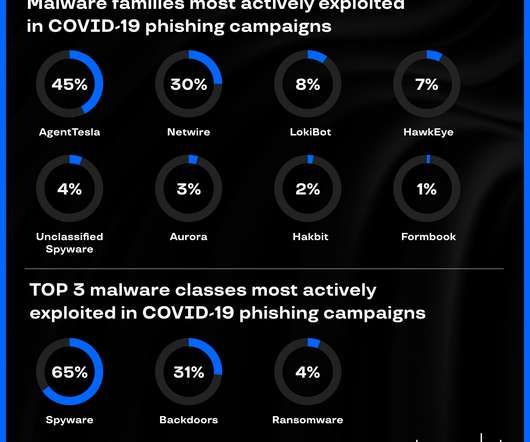
APRIL 9, 2020
Group-IB’s CERT-GIB analyzed hundreds of coronavirus -related phishing emails and discovered top malware strains in COVID-19 campaigns. Group-IB’s Computer Emergency Response Team ( CERT-GIB ) analyzed hundreds of coronavirus-related phishing emails between February 13 and April 1, 2020. Source: CERT-GIB. Source: CERT-GIB.

Malwarebytes
MAY 10, 2023
Just check out the following stats from last year: 18 percent of clicked phishing emails in 2022 came from a mobile device. Verizon Mobile Security Index 2022) 9 percent of organizations suffered a mobile malware attack in 2022. This could be any other type of malware, such as HiddenAds or Adware to generate money by ads-per-click.

Spinone
NOVEMBER 1, 2019
DLP is included in the organization policy, but individuals must also use this strategy to keep all data safe during ransomware or malware attack. Malware and Ransomware Adware – Software that automatically displays or downloads material when a user is offline. The most widespread spyware are keyloggers and trojans.

Digital Shadows
NOVEMBER 10, 2022
Scams could present themselves in many forms. For instance, financially-motivated threat actors often plant in malicious URLs spoofing these events to fraudulent sites, hoping to maximize their chances of scamming naive internet users for a quick (illicit) profit. pro is flagged as a phishing domain by multiple security providers.

SecureList
AUGUST 5, 2021
A fake notification about a Microsoft Teams meeting or a request to view an important document traditionally takes the victim to a phishing login page asking for corporate account credentials. In addition to various cloud-related emails, we blocked messages disguised as business correspondence and containing links to malware.

SecureList
NOVEMBER 1, 2021
Scamming championship: sports-related fraud. Scam: get it yourself, share with friends. million redirects to phishing pages. Note too that QR codes from questionable sources can carry other threats, for example, spreading malware or debiting money in favor of the scammers. Quarterly highlights.

CyberSecurity Insiders
JANUARY 31, 2021
Regardless of how familiar you are with Information Security, you’ve probably come across the term ‘malware’ countless times. From accessing your business-critical resources and sensitive information to halting business operations and services, a malware infection can quickly become an organization’s worst nightmare come true.

SecureList
MAY 3, 2021
Banking phishing: new version of an old scheme. In Q1 2021, new banking scams appeared alongside ones that are more traditional. Clients of several Dutch banks faced a phishing attack using QR codes. The link redirected them to a phishing page requesting their Microsoft account credentials. Quarterly highlights.
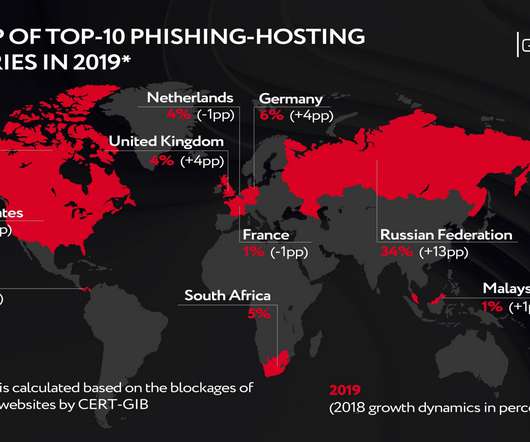
Security Affairs
MAY 8, 2020
Group-IB, a Singapore-based cybersecurity company, observed the growth of the lifespan of phishing attacks in the second half of 2019. Figure 1 The distribution of web-phishing among target categories . CERT-GIB’s findings indicate that phishing attack perpetrators have revised their so-called target pool. Target reshuffle.
Security Affairs
NOVEMBER 11, 2023
Police seized BulletProftLink phishing-as-a-service (PhaaS) platform Serbian pleads guilty to running ‘Monopoly’ dark web drug market McLaren Health Care revealed that a data breach impacted 2.2 Virtual Kidnapping: AI Tools Are Enabling IRL Extortion Scams How a ‘Refund Fraud’ Gang Stole $700,000 From Amazon Info from 5.6

eSecurity Planet
SEPTEMBER 29, 2021
Recent research by Positive Technologies looked at the cyber threat landscape during Q2 2021 and found that ransomware attacks reached “stratospheric” levels, accounting for 69% of all malware attacks, a huge jump from 39% in Q2 2020. Detect compromised accounts, insider threats, and malware. EnigmaSoft. Scan scheduling.

eSecurity Planet
JUNE 8, 2023
Email security consists of the policies, tools, and services deployed to protect against threats specific to email such as spam, phishing attacks, malware-infested attachments, impersonation, and email interception.

Malwarebytes
AUGUST 25, 2022
This is combined with heavy detections of unseen malware, identified through our AI engine, spiking in May as well as September 2021. In the first half of the year, we observed spiking detections of threats associated with tech support scams. These spikes were in March and May 2021 and focused primarily on firms in New York and Texas.

SecureList
NOVEMBER 10, 2021
With millions of new users on streaming platforms, cyberattackers have recognized this heightened demand and seek to take advantage of it by distributing streaming phishing scams and spreading malware under the guise of users’ favorite shows. Malware and riskware instead of streaming. Methodology. Apple TV Plus.

Webroot
MAY 12, 2021
However, when examined more closely, most hosting IPs were found to have hosted malicious content (such as some serious malware ) in the past, and had connections to other high-risk IPs. Contextual graphs such as these show the relationships between web hosts and dropped malware. Bitcoin scams. For instance, rojadirecta[.]me

Malwarebytes
OCTOBER 18, 2021
The breach at the Oldsmar water plant, however, may have involved no malware at all. No spear-phishing attack against an executive’s personal device. No surreptitious implantation of spyware to collect admin credentials. Online scams already ruin people’s lives by emptying their bank accounts.

SecureList
MARCH 7, 2024
To get access to the content (or contest), phishing sites prompted the victim to sign in to one of their gaming accounts. If the victim entered their credentials on the phishing form, the account was hijacked. Alongside the usual get-rich-doing-nothing and paid survey scams, we encountered a few less conventional scenarios.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content