Why Third-Party Risk Should Be Manufacturing's Top Priority
Dark Reading
NOVEMBER 3, 2022
Manufacturing relies on complex interconnected networks and technologies, but with more vendors comes risk that needs to be secured.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
NOVEMBER 3, 2022
Manufacturing relies on complex interconnected networks and technologies, but with more vendors comes risk that needs to be secured.

Security Boulevard
MARCH 29, 2024
One in four industrial enterprises had to temporarily cease operations due to cyberattacks within the past year, suggesting operational technology must improve. The post Industrial Enterprise Operational Technology Under Threat From Cyberattacks appeared first on Security Boulevard.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JULY 13, 2023
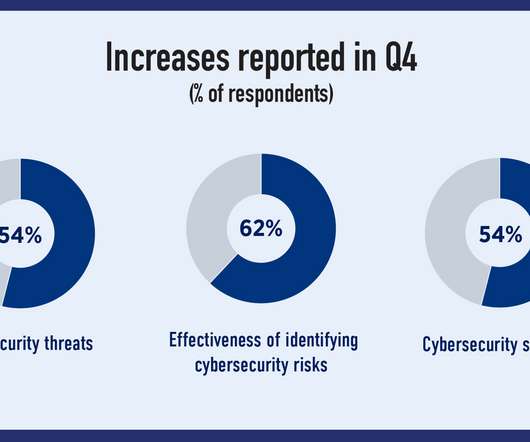
London, July 13, 2023 — Beazley, the leading specialist insurer, today published its latest Risk & Resilience report: Spotlight on: Cyber & Technology Risks 2023. Yet, boardroom focus on cyber risk appears to be diminishing. trillion by 2025, a 300% increase since 2015 1.

Pen Test Partners
FEBRUARY 22, 2024
This is a pivotal moment for manufacturers, importers, and distributors, imposing new compliance measures to safeguard against cyber threats. Implications for manufacturers and vendors This regulatory overhaul extends its reach to the core economic actors in the product lifecycle; manufacturers, importers, and distributors of smart products.

CyberSecurity Insiders
JANUARY 11, 2022
The 2021 ISG Provider Lens Manufacturing Industry Services – Global report finds the complex mix of legacy OT and newer, connected technologies such as industrial IoT and machine learning has forced manufacturers to add security extensions for protection against cyberattacks.

Security Boulevard
JANUARY 16, 2024
What is C-SCRM Cybersecurity Supply Chain Risk Management (C-SCRM) is the strategic process of identifying, assessing, and mitigating risks associated with the information and communication technology (ICT) supply chain.
The State of Security
OCTOBER 31, 2021
Before the revolution of Information Technology (IT), the world experienced the revolution of Operational Technology (OT). Operational Technology is the combination of hardware and software that controls and operates the physical mechanisms of industry.

CSO Magazine
FEBRUARY 16, 2023
The evolution of cybercrime is weighing heavily on digital forensics and incident response (DFIR) teams, leading to significant burnout and potential regulatory risk. That’s according to the 2023 State of Enterprise DFIR survey by Magnet Forensics , a developer of digital investigation solutions.

The Last Watchdog
APRIL 24, 2019
Accounting for third-party risks is now mandated by regulations — with teeth. Allen is a widely respected thought leader on this topic, having launched Shared Assessments in 2005 as an intel-sharing and training consortium focused on third-party risks. That out of the way, business can proceed with less risk.

Thales Cloud Protection & Licensing
OCTOBER 19, 2022
Manufacturing needs to adopt a Zero Trust approach to mitigate increased cyber threats. Long gone is the time when manufacturing systems and operations were siloed from the Internet and, therefore, were not a cybersecurity target. Thu, 10/20/2022 - 06:20. Survey’s key findings.

The Last Watchdog
JANUARY 8, 2023
Departments such as support, manufacturing, design, services, and delivery are enhanced by smart security measures, which allay distracting setbacks and increase the overall inertia. Business initiatives demand faster, more efficient outcomes and technology responds. Smarter security is the rising tide that lifts all ships.

CyberSecurity Insiders
MAY 31, 2023
This conclusion was reached after a comprehensive assessment of inverters from eight different manufacturers, revealing that none of them met even the basic security standards. It is crucial for manufacturers to actively play a role in offering products that comply with established photovoltaic cybersecurity standards.

CyberSecurity Insiders
JANUARY 28, 2022
The 5G technology appears to be perfect from a distance, with its grand claims of fostering efficient interconnectivity and speedy data transfers between people, objects, and devices. Whirlpool has started deploying the 5G technology; other reputable organizations like Samsung, Nokia, and Cisco jump in on the trend.
Security Affairs
MAY 8, 2022
The National Institute of Standards and Technology (NIST) has released updated guidance for defending against supply-chain attacks. The National Institute of Standards and Technology (NIST) has released updated guidance for defending against supply chain attacks. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.
Security Boulevard
MAY 24, 2022
Many modern businesses in almost every sector of the economy are adopting the latest technologies for greater connectivity and efficiency. However, while many of these technologies offer myriad benefits, they can also create new cybersecurity vulnerabilities. The post How Can OEMs Reduce Their Risk of Cyberattacks?

SecureWorld News
FEBRUARY 18, 2024
While connected cars, stereo speakers, headphones, and even lightbulbs can be connected via Bluetooth, there are some risks associated with connecting to devices without security PINs (used during initial pairing) and ephemeral devices like rental cars. To begin, consider the simplest and most well-known risk.

CyberSecurity Insiders
JANUARY 28, 2022
The technological revolution of agriculture is here. Particularly in the context of climate change and a growing global population , the role of emerging technology in the farming industry will be critical to the success and thriving of future generations. This is where smart farming technology can help. With as much as $22.3

Trend Micro
NOVEMBER 11, 2021
5G technology will usher in new personal services through smartphones, and it will also play a large part in industry. We can see signs of increased activity in areas of business that use 5G around the world.

SecureWorld News
FEBRUARY 17, 2024
Wearable technologies continuously monitor vital signs such as heart rate, while larger equipment like dialysis machines and ventilators operate tirelessly to support critical bodily functions. New security solutions are now aiding healthcare organizations' IT teams in promptly resolving issues, even with devices from various manufacturers.
Joseph Steinberg
APRIL 25, 2023
It is hardly a secret that, for nearly 30 years, I have been warning about the danger posed to US national security by the simultaneous combination of our growing reliance on Chinese technology, and our general indifference to China’s huge technological “leaps forward” in the realm of cybersecurity.

SecureWorld News
APRIL 25, 2024
North Korea's prolific state-sponsored hacking units are once again setting their sights on South Korea's defense and arms manufacturing sector. South Korea is home to major defense manufacturers such as Korea Aerospace Industries Ltd. currently Hanwha Ocean Co.

Security Affairs
OCTOBER 4, 2018
Positive Technologies while analyzing Intel Management Engine (ME) discovered that Apple did not disable Intel Manufacturing Mode in its laptops. Experts from security firm Positive Technologies while analyzing Intel Management Engine (ME) discovered that Apple forgot did not lock it in laptops.

Security Boulevard
JULY 28, 2021
Supply chain networks have been driven by technology over the years and have evolved accordingly. However, the same technologies that make supply chains faster and more effective also threaten their cybersecurity. Supply chains have vulnerabilities at touchpoints with manufacturers, suppliers, and other service providers. .

SC Magazine
MAY 27, 2021
Today’s columnist, Matt Wyckhouse of Finite State, says to lock down IoT devices, manufacturers have to build security in from the start. Manufacturers have experienced slower deal cycles and more demands for security reviews. How device manufacturers can stem the tide. infomatique CreativeCommons CC BY-SA 2.0.

SecureBlitz
DECEMBER 7, 2023
As technology advances and vehicles become more connected, the need for automotive cybersecurity is becoming increasingly important. The risk of cyber threats to vehicles has increased significantly in recent years, and this has led to a greater focus on cybersecurity measures by automotive manufacturers and regulators.

eSecurity Planet
FEBRUARY 23, 2022
These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. However, before we dig into the technologies, let’s first examine why we need them. A hard-wired partner realizes a similar isolation, but uses different technology.

The Last Watchdog
AUGUST 31, 2023
The strategic funding round was led by global manufacturing industry leader Rite-Hite with participation from existing investors Eclipse Ventures and World Innovation Lab. We’ve proven that our technology has made great strides toward reducing injuries and saving lives. This takes total funds raised to $30m since 2020.

Security Affairs
MAY 12, 2021
National Security Agency (NSA), along with the DHS Cybersecurity and Infrastructure Security Agency (CISA), and the Office of the Director of National Intelligence (ODNI) have analyzed the risks and vulnerabilities associated with the implementation of 5G networks. ” reads the report. ” concludes the report.”As

Security Boulevard
OCTOBER 31, 2021
Before the revolution of Information Technology (IT), the world experienced the revolution of Operational Technology (OT). Operational Technology is the combination of hardware and software that controls and operates the physical mechanisms of industry.

Security Boulevard
JANUARY 18, 2024
How do we gauge how risky it is and how do we ensure that future APIs are not putting the enterprise at risk? Unfortunately, the security challenges associated with APIs can't be solved by simply updating existing testing tools and edge security defenses to check-the-box technologies that claim to provide "API security."
Cisco Security
MAY 24, 2021
The way suppliers conduct business, as well as they products they sell, could put you and your family at risk. In the business world, digital supply chains present very real risks too, even with well-established, trusted partners. They have a long, established history of design and manufacturing excellence.

CSO Magazine
MARCH 7, 2023
Edge computing is fast becoming an essential part of our future technology capabilities. Everything from autonomous vehicles to medical technologies to smarter Internet of Things (IoT) devices and applications to intelligent manufacturing facilities relies on the low latency, high reliability, and scalability of edge computing.

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
The issue is that these tens of billions of new devices will likely amplify the inherent security risks of IoT. In the absence of IoT security regulations, many smart product manufacturers simply release new devices that lack built-in security measures and have not undergone proper security review and testing.

Schneier on Security
SEPTEMBER 15, 2023
Claude’s reply: Here’s a brief summary of the key themes and arguments made in security expert Bruce Schneier’s book Beyond Fear: Thinking Sensibly About Security in an Uncertain World : Central Themes: Effective security requires realistic risk assessment, not fear-driven responses. Security theater manufactures consent.

Security Boulevard
MAY 14, 2023
In today’s interconnected world, operational technology (OT) systems play a crucial role in industries such as manufacturing, energy, and transportation. However, with increased connectivity comes the risk of cyber threats targeting these critical infrastructures.

Security Affairs
MARCH 14, 2022
While the Russia-Ukraine cyber conflict goes on, nation-state actors, crooks, and hacktivists continue to pose critical infrastructure at risk. Critical infrastructure is a privileged target for almost any kind of threat actor, the ongoing Russia-Ukraine cyber conflict is posing them at risk. ” reported researchers from Cyble.
CyberSecurity Insiders
MAY 17, 2023
As AI technologies become increasingly integrated, industries are witnessing unprecedented changes that enhance productivity, streamline operations, and optimize decision-making processes. Manufacturing: The manufacturing sector is experiencing a paradigm shift as AI optimizes processes and drives efficiency.
SC Magazine
MARCH 11, 2021
Organizations move on plans to strengthen security policies, increase training, and invest in technology. These efforts focused squarely on the people problem: addressing increased risk tied to employees working from home and workforce tensions amid societal pressures from the pandemic. Phishing remained the most frequent threat.
SecureWorld News
AUGUST 8, 2023
As technology continues to evolve, chip designers face a persistent challenge: the pursuit of speed and efficiency must not come at the expense of security. While Intel worked closely with Moghimi to develop a fix, the complex ecosystem of manufacturers, patches, and updates poses challenges in swiftly deploying solutions to protect users.

Pen Test Partners
JANUARY 8, 2024
Intelligence, espionage, technological advancements and other learnings from our annual company conference at the historic and underappreciated Latimer House. The idea was to reduce the risk of valuable information such as troop movements, ship routes, or other plans falling into the wrong hands.

Thales Cloud Protection & Licensing
FEBRUARY 28, 2022
To enable this revolution, automobile manufacturers and their supply chain partners have rapidly adopted new technologies to better serve customers and win competitive advantages: Embedding high-speed connectivity in vehicles to improve customer experience and entertainment as well as real-time diagnostics and OTA updates.

Security Affairs
AUGUST 13, 2019
Security expert discovered multiple flaws in 4G routers manufactured by several companies, some of them could allow attackers to take over the devices. G Richter, a security researcher at Pen Test Partners discovered multiple vulnerabilities 4G routers manufactured by different vendors. ” Richter explained. 0 base score) .
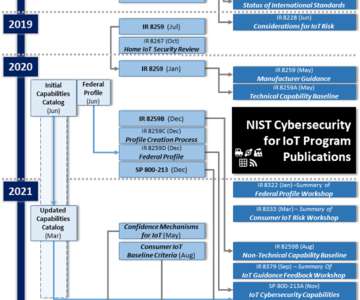
NSTIC
MAY 16, 2022
The NIST Cybersecurity for IoT program published Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks (NISTIR 8228) in June 2019, nearly 3 years ago. Since then, IoT technology has continued to develop and be adopted across sectors and markets.
Security Affairs
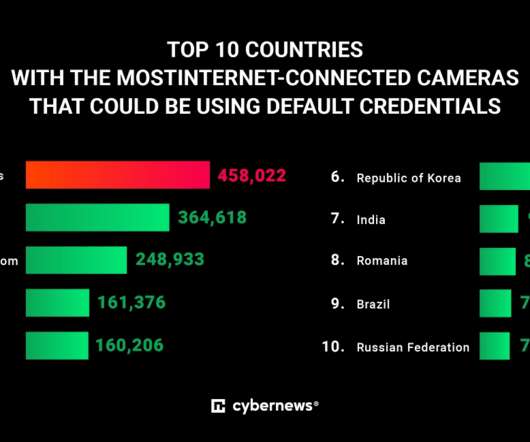
DECEMBER 14, 2022
After looking at 28 of the most popular manufacturers, our research team found 3.5 What is more, the overwhelming majority of internet-facing cameras are manufactured by Chinese companies. Most of the public-facing cameras we discovered are manufactured by the Chinese company Hikvision: the Cybernews research team found over 3.37
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content