3 Essential Elements of an Identity Threat Detection and Response (ITDR) Strategy
Security Boulevard
JULY 21, 2023
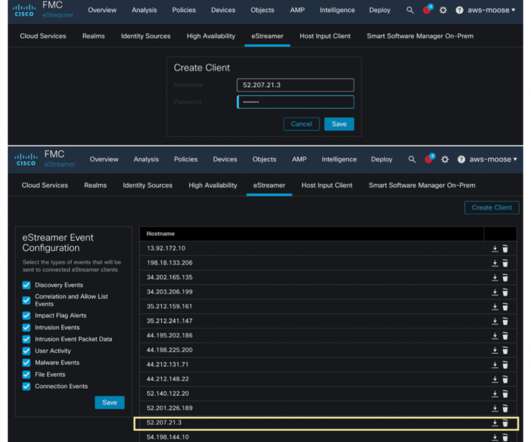
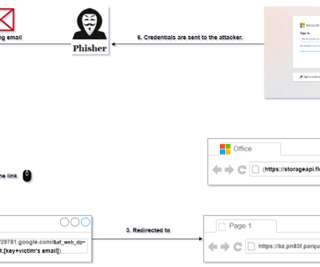
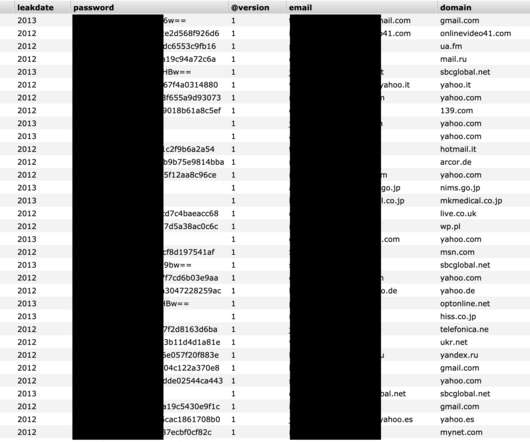
Identity threat detection and response (IDTR) equips enterprises to protect digital identities along with the identity systems that manage them. This is why it's critical to secure your user identities and passwords and the IAM services that manage them. Digital identity data is a cybercriminal's favorite target.













































Let's personalize your content