Self-Driving Cars Are Surveillance Cameras on Wheels
Schneier on Security
JULY 3, 2023
. “We’ve known for a long time that they are essentially surveillance cameras on wheels,” said Chris Gilliard, a fellow at the Social Science Research Council.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
JULY 3, 2023
. “We’ve known for a long time that they are essentially surveillance cameras on wheels,” said Chris Gilliard, a fellow at the Social Science Research Council.

Schneier on Security
FEBRUARY 21, 2020
I teach cybersecurity policy and technology at the Harvard Kennedy School of Government. My most recent two books, Data and Goliath -- about surveillance -- and Click Here to Kill Everybody -- about IoT security -- are really about the policy implications of technology. Technology is inherently future focused.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Adam Shostack
APRIL 29, 2021
There’s an interesting paper, ‘It depends on your threat model’: the anticipatory dimensions of resistance to data-driven surveillance. The author critiques ‘anticipatory data practices’, a collection of techniques that include my own work, as presented to civil society activists.

Security Affairs
NOVEMBER 28, 2021
Nexa Technologies was indicted for complicity in acts of torture, the French firm is accused of having sold surveillance equipment to the Egypt. Nexa Technologies offers a range of solutions for homeland security, including surveillance solutions. ” reported the website LeMonde. ” continues Télérama.

Security Affairs
JULY 24, 2023
in response to the government’s surveillance demands. In light of the government’s surveillance demands, Apple might consider withdrawing iMessage and FaceTime services from the U.K. “ Companies like WhatsApp and Signal declined to comply with a clause present in the Online Safety Bill. .

Schneier on Security
SEPTEMBER 6, 2018
Our national security depends on the security of our technologies. Demanding that technology companies add back doors to computers and communications systems puts us all at risk. We need a "defense dominant" strategy for securing the Internet and everything attached to it. This is important.

Security Affairs
APRIL 23, 2024
The measure aims to counter the misuse of surveillance technology targeting journalists, academics, human rights defenders, dissidents, and US Government personnel, as documented in the Country Reports on Human Rights Practices. Additionally, the misuse of these tools presents a security and counterintelligence threat to U.S.

Security Affairs
FEBRUARY 6, 2024
government’s commitment to addressing the misuse of surveillance software, which poses a significant threat to society. Additionally, the misuse of these tools presents a security and counterintelligence threat to U.S. The policy underscores the U.S. ” reads the announcement. The Entity List maintained by the U.S.

Schneier on Security
JULY 21, 2023
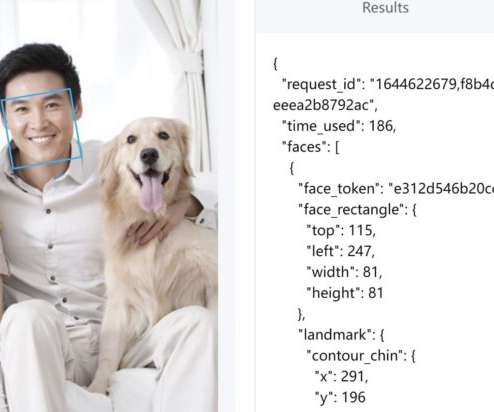
In New York, AI systems equipped with facial recognition technology are being used by businesses to identify shoplifters. China is experimenting with even more powerful forms of automated legal enforcement and targeted surveillance. A Digital Millennium Copyright Act takedown notice is a present-day example of a microdirective.

Malwarebytes
MARCH 7, 2024
Predator can turn infected smartphones into surveillance devices. Nelson said: “Today’s actions represent a tangible step forward in discouraging the misuse of commercial surveillance tools, which increasingly present a security risk to the United States and our citizens.”

Schneier on Security
OCTOBER 9, 2023
Reading the headlines, one would hope that the rapid gains in AI technology have also brought forth a unifying realization of the risks—and the steps we need to take to mitigate them. The technology historian David C. The reality, unfortunately, is quite different.

The Last Watchdog
OCTOBER 18, 2023
The ubiquity of smart surveillance systems has contributed greatly to public safety. We discussed how ABE is ready to help resolve some rather sticky privacy issues stemming from widespread digital surveillance – and also do much more. Here are my takeaways. Today, Goto says, ABE is fully ready to validate in real world deployments.

SecureWorld News
FEBRUARY 7, 2024
State Department announced Monday a new policy to impose visa restrictions on individuals linked to the misuse of commercial spyware tools that enable unlawful surveillance and human rights abuses globally. The policy allows visa denials on a case-by-case basis for those involved in spyware misuse. RELATED: U.S.

BH Consulting
MARCH 10, 2021
State sector surveillance as well as local authorities’ use of CCTV cameras was a key focus for the DPC in 2020 as highlighted in the recently published DPC annual report. Primary areas of focus for the DPC in 2020 included enforcement (under both GDPR & ePrivacy), breach notifications, data transfers and surveillance.

Security Affairs
DECEMBER 3, 2021
The US officials targeted by the surveillance software were either based in Uganda or focused on matters concerning the African country, revealed Reuters which was not able to determine which was NSO client that orchestrated the attacks. officials through NSO technology.” “Apple Inc iPhones of at least nine U.S. .

Malwarebytes
OCTOBER 11, 2023
It’s spying when governments do it through opaque, mass surveillance regimes, it’s spying when companies do it through shadowy data broker networks that braid together disparate streams of information, and it’s spying when private individuals do it through unseen behavior on personal devices. They are deeply concerning.

Schneier on Security
JUNE 6, 2023
In 2013 and 2014, I wrote extensively about new revelations regarding NSA surveillance based on the documents provided by Edward Snowden. I paged through weekly reports, presentation slides from status meetings, and general briefings to educate visitors. The meeting presenters try to spice things up. And Edward Snowden?

The Last Watchdog
SEPTEMBER 11, 2023
Yet, the rise of internal fraud presents a unique challenge. Another example of on-the-ground tactics includes Intelligence agencies exploiting graduate students at research universities to access sensitive materials and coercing professionals working on sensitive technologies to engage in activities like IP theft.

SecureList
JUNE 16, 2021
When run, the executables display decoy content to the victims, with some presenting images of protests against the Iranian regime and its institutions, or videos from resistance camps. Decoy image found within one of the malicious executables showing a protest against the central bank of Iran.
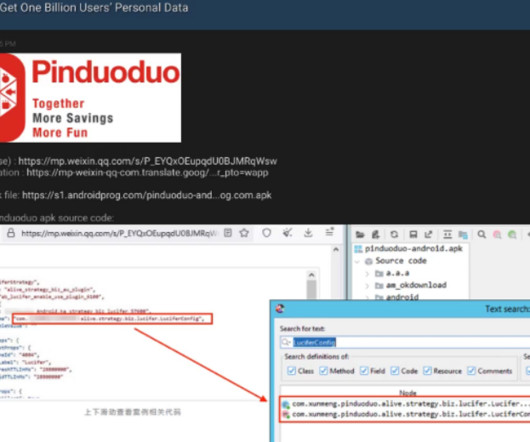
Krebs on Security
MARCH 22, 2023
Google said it believes the exploit chain for Samsung devices belonged to a “commercial surveillance vendor,” without elaborating further. “At present, a large number of end users have complained on multiple social platforms,” reads a translated version of the DarkNavy blog post. and Western interests.

SecureWorld News
MARCH 29, 2023
The order comes in response to growing concerns about the use of such software to conduct surveillance and espionage operations. The most notable of these incidents was the NSO Group's Pegasus spyware, which was used by various governments around the world to surveil activists, journalists, and other individuals.

Security Affairs
NOVEMBER 2, 2019
Proton Technologies announced this week that it has made available the source code of its popular ProtonMail iOS App. The Proton Technologies firm continues to propose initiatives aimed at ensuring the transparency of its ProtonMail applications, this week it announced the availability of the source code of its popular ProtonMail iOS App.

SecureWorld News
AUGUST 16, 2023
Technology is increasingly part of our day-to-day life; we use it for communication, work, getting information, and even running our households with smart devices. However, as we spend more and more of our lives online and put our trust in technology, it becomes an increasingly accessible tool for abusers to utilize.

CSO Magazine
MARCH 2, 2022
These include scanning of Microsoft Azure Active Directory (AD), Microsoft 365 and AWS environments for signs of attack, surveillance of network infrastructure both in the cloud and on-premises and supporting the retention of historical metadata to aid incident response investigations based on indicators of compromise for specific attack variants.

Security Affairs
OCTOBER 14, 2022
Recently, the Cybernews research team stumbled upon an unprotected database with over 90 million drone-monitoring logs generated by DJI devices – the largest market player in the world that sells both drones and devices to surveil them. The surveillance race. No personally identifiable information (PII) was present in the dataset.

Security Affairs
NOVEMBER 29, 2019
Group-IB’s annual report was presented at CyberCrimeCon 2019 international Threat Hunting and Intelligence conference in Singapore. If they manage to compromise a telecommunications company, they can then also compromise its customers for surveillance or sabotage purposes. Pierluigi Paganini.

Schneier on Security
FEBRUARY 29, 2024
This isn’t the first time the concept of a frontier has been used as a metaphor for AI, or technology in general. American exceptionalism has also wrought havoc on our country’s engagement with the internet, including lawless spying and surveillance by forces like the National Security Agency.
eSecurity Planet
FEBRUARY 11, 2022
The technology isn’t yet perfect, but it has evolved to a point that enterprise use is growing. The application of facial recognition technology in operations was primarily in law enforcement organizations until the last decade, when a massive advance in AI and deep learning allowed it to be more broadly applied.

Security Affairs
FEBRUARY 9, 2023
the SIM card is not present in the phone or if the SIM card used was provided by a different operator in China or in the UK). The experts pointed out that also users that leave the country are exposed to surveillance, through the pre-installed software. . ” reads the paper published by the experts.

Security Affairs
OCTOBER 22, 2018
“The Israel Defense Forces asked cybersecurity companies in 2016 to present proposals for creating a system that would monitor social media users’ personal correspondence.” The Israeli Defense explained added that the bidding process was not carried out for both operational and technological reasons.

Malwarebytes
JULY 19, 2023
Footage from technology used to monitor Amazon delivery drivers is leaking onto the internet. AI-enabled equipment which keeps an eye on the drivers’ speed, location, and other activities is part of the growing trend of workplace surveillance. There are other privacy issues to consider too.

Krebs on Security
MARCH 2, 2023
” Brian Fox , chief technology officer and founder of the software supply chain security firm Sonatype , called the software liability push a landmark moment for the industry. ” Many of the U.S. ” Many of the U.S. based semiconductor manufacturing and research and to make the U.S.

The Security Ledger
JUNE 10, 2020
In this episode of the podcast (#185), DigiCert Chief Technology Officer Jason Sabin joins us to talk about how the COVID epidemic is shining a spotlight on the need for strong digital identities - for everything from virus contact tracing to remote work. Jason Sabin is the Chief Technology Officer at DigiCert. Read the whole entry. »

Malwarebytes
OCTOBER 10, 2022
On Tuesday, the Biden-Harris Administration's Office of Science and Technology Policy (OSTP) unveiled a new Blueprint for an AI Bill of Rights , which lists five principles to guide the design, use, and development of intelligence-based automated systems "to protect the American public in the age of artificial intelligence".
Javvad Malik
NOVEMBER 25, 2020
When we talk about privacy and surveillance, discussions usually involve talk of Governments keep the population under manners. Amazon has found itself in the spotlight this past week with Vice publishing an article entitled, Secret Amazon Reports Expose the Company’s Surveillance of Labor and Environmental Groups. Surveillance 365.
eSecurity Planet
SEPTEMBER 25, 2022
In 2013, for example, the FIDO Alliance was created to solve the world’s password problem by replacing login technology. But beyond these cases, how advanced is the implementation of the technology that wants to end passwords once and for all? The Challenges of New Authentication Technologies. See the Top Password Managers.

The Last Watchdog
SEPTEMBER 18, 2018
I talked with Jonathan Sander, Chief Technology Officer with STEALTHbits Technologies , about this at Black Hat USA 2018. While there is nascent technology for analyzing unstructured data, these solutions are still fairly primitive. Editor’s note: LW has provided consulting services to STEALTHbits Technologies.).

Schneier on Security
OCTOBER 1, 2019
There are four key implications of this revolution that policymakers in the national security sector will need to address: The first is that the unprecedented scale and pace of technological change will outstrip our ability to effectively adapt to it. The NSA doesn't opine on broad technological trends and their social implications.

Malwarebytes
MARCH 9, 2022
All data vanishes when the browser is closed (think Incognito mode), and three levels of security increasingly strip out page aspects such as JavaScript and media which could present problems. Many sites have a.onion version available to make it even harder to perform surveillance on the user. That’s not all.

SecureWorld News
JANUARY 31, 2024
The integration of technology and automation, and related collection, use, and sharing of information into everyday business practices presents an enormous opportunity for efficiency and precision, especially in the real estate sector. Cyber risk is an existential issue for companies of all sizes and in all industries.

The Last Watchdog
JULY 27, 2020
Either way, a singular piece of technology – artificial intelligence (AI) — is destined to profoundly influence which way we go from here. Law enforcement, for instance, drew criticism for using a controversial facial recognition app — Clearview AI — to surveil citizens turning out to protest the George Floyd murder.

eSecurity Planet
MAY 24, 2024
Implement Security Controls Following NIST’s cloud security model, develop policies, methods, and technology for protecting cloud assets, such as access control, encryption, and network security. Assess compliance status: Evaluate your organization’s present compliance posture, noting any gaps or flaws that must be corrected.

Security Affairs
FEBRUARY 8, 2019
The Agency calls for proposals on solutions that could support NATO’s command, control, communications, computers, intelligence, surveillance and reconnaissance (C4ISR) and of course to improve cyber capabilities. Proposals must be received by 22 March, and the Agency will announce the winners on 8 April.

Adam Levin
MARCH 8, 2019
The move will further blur the line between the consumer’s physical environment and what has become an ever-present, virtual marketplace where the offerings of Amazon are sewn into the fabric of daily life. What is Amazon’s position regarding consumer willingness to be surveilled in this way? In theory, everyone wins.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content