Best 5 Privacy Management Tools for 2024
Centraleyes
APRIL 8, 2024
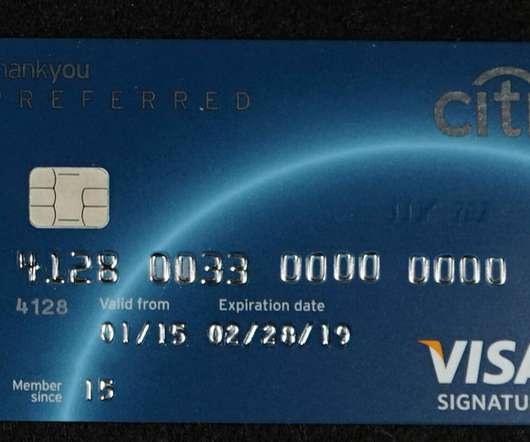
High-profile data breaches have made data protection and privacy a hot subject. Hackers use more sophisticated methods to break network defenses and steal sensitive data on a large scale. Malicious actors target personal data because of its value. They use this data to steal identities and access corporate accounts.










































Let's personalize your content