Paragon Spyware used to Spy on European Journalists
Schneier on Security
JUNE 13, 2025
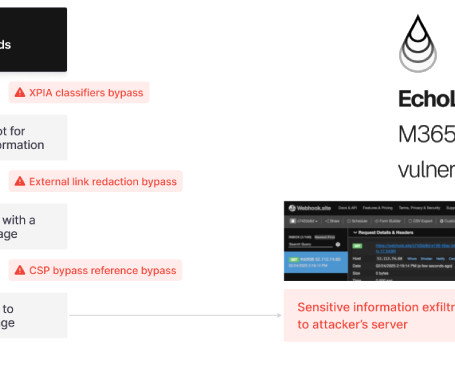
Paragon is a Israeli spyware company, increasingly in the news (now that NSO Group seems to be waning). “Graphite” is the name of their product. Citizen Lab caught them spying on multiple European journalists with a zero-click iOS exploit: On April 29, 2025, a select group of iOS users were notified by Apple that they were targeted with advanced spyware.








































Let's personalize your content