2020 sees huge increase in records exposed in data breaches
Tech Republic Security
JANUARY 21, 2021
The number of breaches may have fallen, but the number of exposed records hit a high not seen since 2005, says Risk Based Security.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JANUARY 21, 2021
The number of breaches may have fallen, but the number of exposed records hit a high not seen since 2005, says Risk Based Security.

The Last Watchdog
APRIL 24, 2019
Accounting for third-party risks is now mandated by regulations — with teeth. Allen is a widely respected thought leader on this topic, having launched Shared Assessments in 2005 as an intel-sharing and training consortium focused on third-party risks. That out of the way, business can proceed with less risk.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureBlitz
OCTOBER 1, 2022
In this interview, we spoke with David Monnier, Chief Evangelist at Team Cymru, a risk management solution launched in 2005 with a network that extends to 143 CSIRT teams in 86 countries and over 1,000 network operators and ISP community that helps keep the internet safe. Team Cymru has released the findings from their State […].

The Last Watchdog
JANUARY 30, 2019
Related: Atrium Health breach highlights third-party risks. Third-party cyber risks are likely to persist at the current scale for a while longer. According to a recent Ponemon Institute study , some 59% of companies experienced a third-party data breach in 2018, yet only 16% believe they are effectively mitigating third-party risk.

Malwarebytes
SEPTEMBER 22, 2022
In Firefox 105 a total of seven vulnerabilities were patched, three of which received the security risk rating "high". One with the rating “high” risk. Since UTF-8 as character encoding was introduced in 2005, there may be still some URLs which use a different encoding.
Security Affairs
NOVEMBER 24, 2022
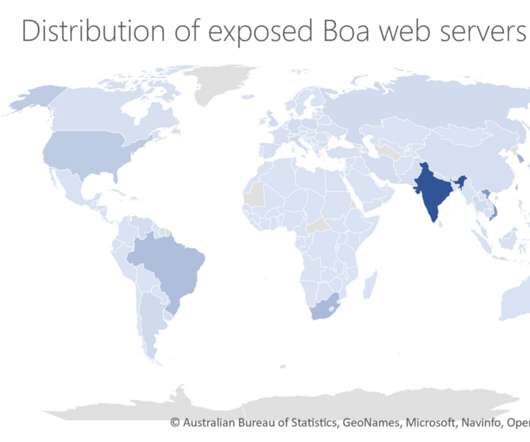
The experts pointed out that Boa has been discontinued since 2005. ” Microsoft experts explained that despite Boa being discontinued in 2005, many vendors across a variety of IoT devices and popular software development kits (SDKs) continue to use it. ” reads the report published by Microsoft. ” concludes the report.

Malwarebytes
FEBRUARY 6, 2023
In 2005, one malware install which needed the.NET framework to run would helpfully install the whole thing for you if you didn’t have it. For one final slice of additional context, 2005 was also a key year for security happenings. By curious coincidence, the ASC also came into existence in 2005. Stay safe out there!

Malwarebytes
JANUARY 12, 2024
is an open-source CMS that’s been around since 2005, and has been one of the most popular CMS platforms by market share for much of that time. Cybersecurity risks should never spread beyond a headline. Many companies, from small outfits to large enterprises, use a CMS in some form to manage their websites.

Security Affairs
MARCH 27, 2022
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities , FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.

Malwarebytes
FEBRUARY 23, 2024
is an open-source CMS that’s been around since 2005, and has been one of the most popular CMS platforms by market share for much of that time. Cybersecurity risks should never spread beyond a headline. posted details about four vulnerabilities it had fixed in its Content Management System (CMS), and one in the Joomla!

Malwarebytes
AUGUST 18, 2022
Mechanical drives have a whole lot of vibration going on inside, and this is where the drives become vulnerable to very peculiar forms of frequency based risk. As I close the lid on my 2005 Windows XP laptop for the last time, never a truer word was spoken.

Security Affairs
JUNE 13, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. The availability of the database in the cybercrime ecosystem poses a severe risk for the company users.
Security Affairs
SEPTEMBER 26, 2023
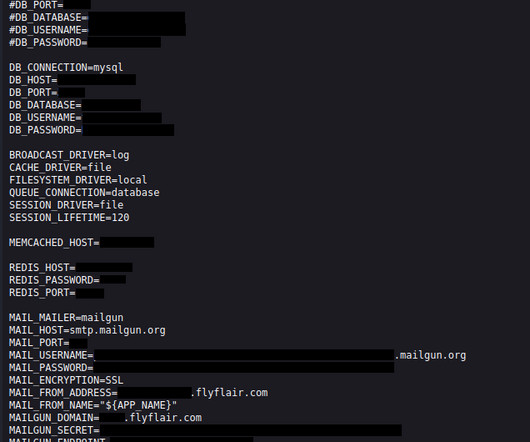
This increases the risk of passengers’ personal information, such as emails, names, or addresses, ending up in the wrong hands. Flyflair.com belongs to the Canadian ultra-low-cost carrier Flair Airlines, founded in 2005. The leak consisted of publicly accessible environment files hosted on the flyflair.com website.

Security Affairs
MAY 2, 2019
The availability of 10KBLAZE PoC exploits for old SAP configuration issue poses a severe risk of attacks for business applications. The risk of cyber attacks against SAP systems is increased after security researchers released PoC exploits for old SAP configuration flaws. ” reads the analysis published by Onapsis.

IT Security Guru
JUNE 28, 2022
As a result, it’s difficult to gauge how at risk an organisation is. A conservative estimate from 2002 predicted that by 2005, cyber insurance would boast a global market worth $2.5 Among security professionals, cyberattacks are no longer viewed as a risk, but as an inevitability. The story so far. It didn’t take off.
Security Affairs
MARCH 28, 2023
million records dating back to at least 2005 were also compromised in the data breach. “We are committed to working closely with impacted customers and applicants to minimise the risk and disruption to them, including reimbursing the cost if they choose to replace their ID document. 94% of these records (5.7

The Security Ledger
NOVEMBER 21, 2023
Related Stories Is a DEF CON Village the right way to assess AI risk? Air Force personnel way back in 2005 as a way to talk about the kinds of enduring cyber attacks and attempts at data exfiltration they were observing. The post Spotlight Podcast: RADICL Is Coming To The Rescue Of. Read the whole entry. » Sickened by Software?
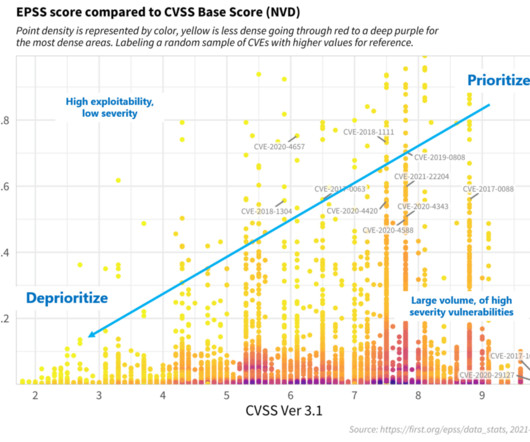
NopSec
OCTOBER 18, 2022
Accurately assessing the risk of software vulnerabilities is critical in order to prioritize remediation efforts given limited remediation resources. For vulnerabilities provided by the Common Vulnerability Enumeration (CVE) Program, many scanning systems utilize the Common Vulnerability Scoring System (CVSS) to assess risk.

Security Affairs
SEPTEMBER 4, 2021
. “For example, the SEC brought a number of enforcement actions against individuals and companies who made false and misleading statements about alleged business opportunities in light of damage caused by Hurricane Katrina in 2005. Know that promises of fast and high profits, with little or no risk, are classic signs of fraud.

The Last Watchdog
MARCH 28, 2023
In the late 1990s (yes, that long ago), I created a youth training program called YouthLink that worked with at-risk youth in Washington, DC. Over my career, I have created three non-profits and two SaaS for profits, one of which I sold in 2005.

The Last Watchdog
MAY 3, 2021
All of the technical innovation cybersecurity vendors are churning out to deal with ever-expanding cyber risks, at the end of the day, come down to protecting encrypted data. And since 2005 or so, one area of focus has been on sharpening the math formulas that make attribute-based encryption possible.

SC Magazine
FEBRUARY 18, 2021
First, the M1 chip represents a break from the Intel x86 architecture that Apple has relied on since 2005 – a move that came with promises of greater security. The new chip, which runs on reduced instruction set computing (RISC) technology, was developed by Advanced RISC Machines (ARM), which makes 32-bit and 64-bit versions.

The Last Watchdog
JUNE 23, 2021
The challenge of embracing digital transformation while also quelling the accompanying cyber risks has never been greater for small- and mid-sized businesses. Somehow SMBs must keep pace competitively, while also tamping down the rising risk of suffering a catastrophic network breach. Remote desktop risks.

The Last Watchdog
MARCH 29, 2022
They’re now the norm and security teams must assess and manage the risk of these stacks.”. Complex and evolving cyber risks need to be resolved, for instance, when it comes to securing human and machine identities, tightening supply chains, mitigating third-party risks, protecting critical infrastructure and preserving individuals’ privacy.
Security Boulevard
JULY 21, 2022
Since 2005, SHA-1 has been regarded as unsafe against well-funded adversaries. For businesses still using the broken SHA-1, they were facing serious risks , including: Increased possibility of a collision or man-in-the-middle attack. What SHA-1 history can teach us? The presence of wildcard SSL certificates. Related Posts.
Malwarebytes
OCTOBER 21, 2021
This time the update patches 19 vulnerabilities, of which 5 are classified as “high” risk vulnerabilities. Below are the CVEs attributed to external researchers that got rated as high risk: CVE-2021-37981 (High CVSS 7.7) : Heap buffer overflow in Skia.

SiteLock
AUGUST 27, 2021
With the growing popularity of the Internet over the past decade, the retail holiday Cyber Monday debuted in 2005 as the online version of Black Friday. While this influx of holiday shoppers purchasing gifts for themselves and loved ones is great for online businesses, there are risks that come along with the rewards. 25% of U.S.

Pen Test
OCTOBER 12, 2023
Various technologies and wireless protocols operate within specific frequency bands of this spectrum, each catering to distinct purposes (Tse, Viswanathan, & Letaief, 2005). These regulations necessitate thorough assessments of wireless systems to ensure compliance and mitigate the risk of data breaches. Cambridge University Press.

CyberSecurity Insiders
MAY 26, 2021
Metz brings the experience of a combat commander who led over 120,000 coalition troops belonging to Multi-National Corps-Iraq, during OPERATION IRAQI FREEDOM (2004-2005) combined with almost 40 years of commissioned service in the US Army. About Intelligent Waves, LLC.

Security Affairs
JANUARY 23, 2020
The unprotected archive was containing support requests submitted to the tech giant from 2005 to December 2019. The availability of detailed logs in the hand of crooks could expose Microsoft customers to the risk of Tech support scams. . ” reads the post published by Microsoft.

The Last Watchdog
APRIL 1, 2020
Here are key takeaways: Storage efficiencies With so much data coursing through business networks, companies would be wise to take into consideration the value vs. risk proposition of each piece of data, Lahiri says. The value of data connected to a live project is obvious.

Herjavec Group
NOVEMBER 16, 2020
When this trend started back in 2005, people preferred to shop while they were at the office, using fast computers and high-speed connections. Trust me, their corporate and personal email inboxes will be flooded with special incentives and opportunities to put your business at risk. But why Cyber Monday and not Saturday?

CyberSecurity Insiders
NOVEMBER 13, 2021
What’s more, insurers are looking to reduce the risk they take on when they provide cyber policies. Businesses have been failing to keep pace, and if they don’t commit to strategic investment in their cyber security, they risk serious financial and reputational damage.”. This is because cyberattacks are becoming more frequent.

Security Affairs
MAY 22, 2019
“We made an error when implementing this functionality back in 2005: The admin console stored a copy of the unhashed password. At the time Google did not reveal how many users might have been impacted, but we have to consider that currently, G Suite has 5 million enterprise customers potentially at risk. ” continues Google.
SiteLock
AUGUST 27, 2021
This system had two major benefits: There was no longer a need to edit core WordPress files, which meant that WordPress could be upgraded more easily without the risk of losing your customizations. The first WordPress plugin directory was born in late 2005 and looked like this: Premium Plugins Hit the Scene.

Malwarebytes
JANUARY 16, 2024
As a member of the club, he competed in a local programming competition, helping the team to win in both 2005 and 2006. We don’t just report on threats—we remove them Cybersecurity risks should never spread beyond a headline. Despite this, he was active in extracurricular activities. In high school, he participated in a computer club.

The Last Watchdog
JANUARY 7, 2019
Initially introduced in 2005, CVSS is a framework for rating the severity of security vulnerabilities in software. The risks are growing for two reasons. Kfir: What we hope will happen is that the security monitoring systems will become more risk oriented, and more focused on reducing critical vulnerabilities. Barda: Yes.

Malwarebytes
OCTOBER 27, 2022
Even so, it seems more varied types of ad presentations were required to lower the risk of turning people away from streaming or watching altogether. Way back in 2005, dynamic ads were introduced to titles like The Matrix Online. A recent change to ad types and functionality made the ads “ less annoying ” overall.

eSecurity Planet
FEBRUARY 10, 2022
Gartner first coined the term SIEM in 2005 to combine the technologies of security event management (SEM) and security information management (SIM). If log files are generated from infected endpoints, there is a risk in establishing a corrupted device as a baseline and future alerts are jeopardized. What is a SIEM?

ForAllSecure
NOVEMBER 3, 2021
In the Coming of Age era, 2005-2019, provided "free" long distance and "free" internet access, we're always online, but this gives rise to surveillance capitalism. He said, "the better you understand the risks, the better informed your decisions will be." So it's up to the hackers and researchers.

BH Consulting
MARCH 10, 2021
The DPC found that certain CCTV cameras operated by Local Authorities today for crime prevention were unlawful due to the absence of authorisation from the Garda Commissioner under Section 38 of An Garda Síochána Act 2005. Additionally, we provide recommendations on the appropriate controls to mitigate or minimise those risks.

Thales Cloud Protection & Licensing
MAY 3, 2018
According to our 2018 Global Encryption Trends Study , 43% of respondents report that their organization has an encryption strategy they apply across the enterprise, compared with 15% in 2005. Solutions for Transparent Database Encryption. With a dedicated centralized key management solution you can overcome these challenges.

Security Affairs
APRIL 8, 2019
Group-IB collects and analyses large amounts of unique and proprietary information to deliver tailored, trusted and actionable intelligence to predict risks, while preventing and mitigating any targeted attacks. About Group-IB. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

SiteLock
AUGUST 27, 2021
As you can see in the chart below from Statista, data breaches rose more than tenfold between 2005 and 2017. failing to regularly update your theme, plugin, and core files is a huge security risk. There are quite a few attack vectors available to breach a database. If you have a Content Management System (CMS) like WordPress or Joomla!,
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content