XDSpy APT remained undetected since at least 2011
Security Affairs
OCTOBER 2, 2020
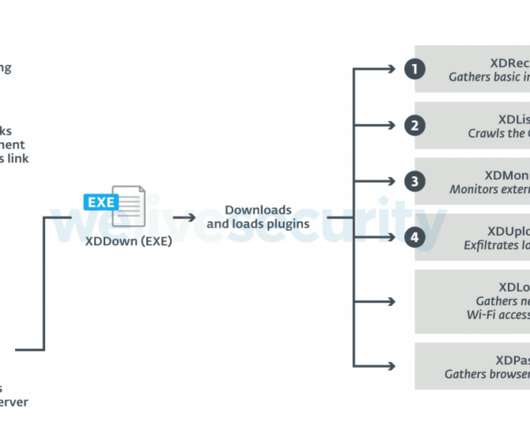
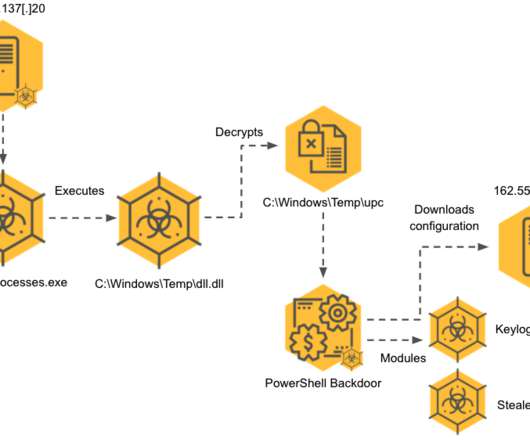
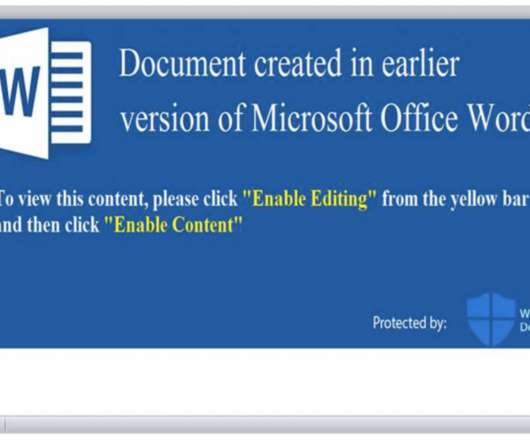
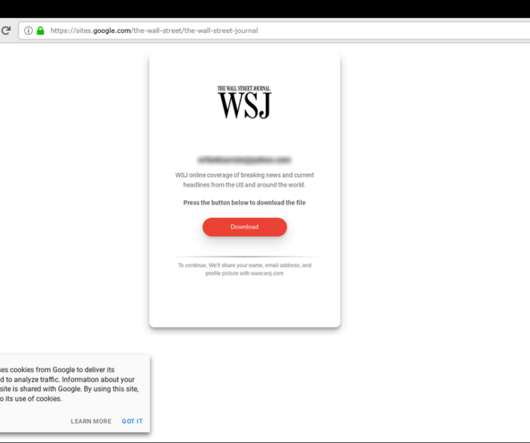
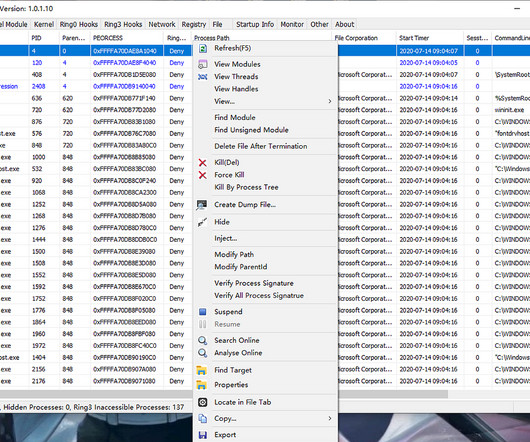
Researchers from ESET uncovered the activity of a new APT group, tracked as XDSpy, that has been active since at least 2011. XDSpy is the name used by ESET researchers to track a nation-state actor that has been active since at least 2011. XDPass: Grabs saved passwords from various applications such as web browsers and email programs.

































Let's personalize your content