The FBI warns of HiatusRAT scanning campaigns against Chinese-branded web cameras and DVRs
Security Affairs
DECEMBER 17, 2024
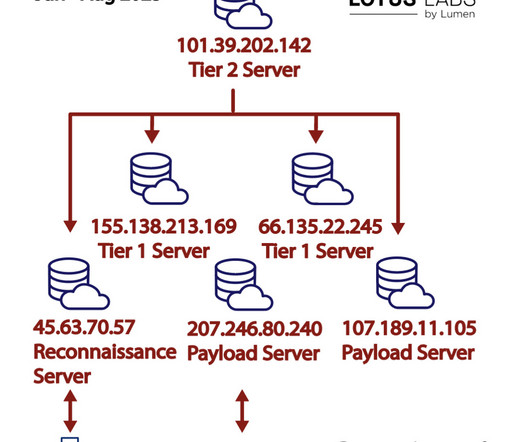
The FBI warned of a fresh wave of HiatusRAT malware attacks targeting internet-facing Chinese-branded web cameras and DVRs. In March 2024, threat actors behind this campaign started targeting Internet of Things (IoT) devices in the US, Australia, Canada, New Zealand, and the United Kingdom. ” reads the PIN report.




































Let's personalize your content