2020 Oscar Nominees Used to Spread Malware
Adam Levin
FEBRUARY 7, 2020
Online scammers are using the 2020 Oscars to spread malware. The post 2020 Oscar Nominees Used to Spread Malware appeared first on Adam Levin.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
APRIL 18, 2024
Nearly 10 million devices were infected with data-stealing malware in 2023, with criminals stealing an average of 50.9 credentials per device.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
OCTOBER 11, 2022
Attacks using ATM or PoS malware are on the rise again in 2022 after the COVID-19 lockdowns. The post The 2020-2022 ATM/PoS malware landscape appeared first on TechRepublic.

Krebs on Security
AUGUST 11, 2020
At least 17 of the bugs squashed in August’s patch batch address vulnerabilities Microsoft rates as “critical,” meaning they can be exploited by miscreants or malware to gain complete, remote control over an affected system with little or no help from users.

Schneier on Security
JANUARY 24, 2022
Crowdstrike is reporting that malware targeting Linux has increased considerably in 2021: Malware targeting Linux systems increased by 35% in 2021 compared to 2020. XorDDoS, Mirai and Mozi malware families accounted for over 22% of Linux-targeted threats observed by CrowdStrike in 2021. Lots of details in the report.

SecureList
MARCH 1, 2021
In 2020, Kaspersky mobile products and technologies detected: 5,683,694 malicious installation packages, 156,710 new mobile banking Trojans, 20,708 new mobile ransomware Trojans. It just so happened that the year 2020 gave hackers a large number of powerful news topics, with the COVID-19 pandemic as the biggest of these.

Krebs on Security
NOVEMBER 10, 2020
Some 17 of the 112 issues fixed in today’s patch batch involve “critical” problems in Windows, or those that can be exploited by malware or malcontents to seize complete, remote control over a vulnerable Windows computer without any help from users. “It is very likely he will publish the details of these bugs soon. .
Security Affairs
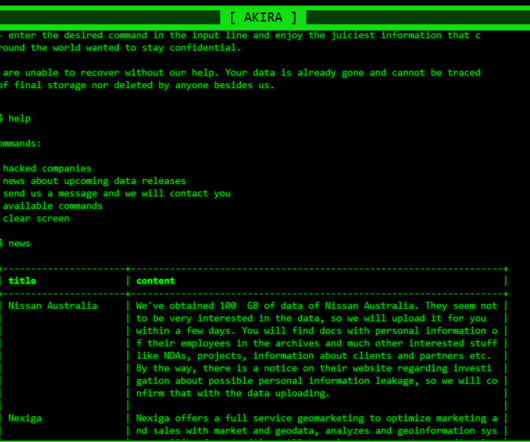
FEBRUARY 17, 2024
CISA warns that the Akira Ransomware gang is exploiting the Cisco ASA/FTD vulnerability CVE-2020-3259 (CVSS score: 7.5) Cybersecurity and Infrastructure Security Agency (CISA) added a Cisco ASA and FTD bug, tracked as CVE-2020-3259 (CVSS score: 7.5), to its Known Exploited Vulnerabilities catalog. in attacks in the wild.

Krebs on Security
APRIL 14, 2020
Nineteen of the weaknesses fixed on this Patch Tuesday were assigned Microsoft’s most-dire “critical” rating, meaning malware or miscreants could exploit them to gain complete, remote control over vulnerable computers without any help from users. Further reading: Qualys breakdown on April 2020 Patch Tuesday.

Krebs on Security
MAY 12, 2020
At least 16 of the bugs are labeled “Critical,” meaning ne’er-do-wells can exploit them to install malware or seize remote control over vulnerable systems with little or no help from users. BleepingComputer on May 2020 Patch Tuesday. Further reading: SANS Internet Storm Center breakdown by vulnerability and severity.

Krebs on Security
SEPTEMBER 8, 2020
None of the flaws are known to be currently under active exploitation, but 23 of them could be exploited by malware or malcontents to seize complete control of Windows computers with little or no help from users. “We have seen the previously patched Exchange bug CVE-2020-0688 used in the wild, and that requires authentication. .

Schneier on Security
JUNE 30, 2022
Wired is reporting on a new remote-access Trojan that is able to infect at least eighty different targets: So far, researchers from Lumen Technologies’ Black Lotus Labs say they’ve identified at least 80 targets infected by the stealthy malware, including routers made by Cisco, Netgear, Asus, and DrayTek.

SecureBlitz
FEBRUARY 21, 2024
In 2020, the digital landscape witnessed a cunning maneuver by the infamous Astaroth malware. Cisco Talos researchers first uncovered this devious strategy, revealing that Astaroth embedded encrypted and […] The post Astaroth malware uses YouTube channel descriptions for hacks appeared first on SecureBlitz Cybersecurity.

The Hacker News
APRIL 22, 2024
The Russia-linked nation-state threat actor tracked as APT28 weaponized a security flaw in the Microsoft Windows Print Spooler component to deliver a previously unknown custom malware called GooseEgg.

Krebs on Security
MARCH 10, 2020
Twenty-six of those earned Microsoft’s most-dire “critical” rating, meaning malware or miscreants could exploit them to gain complete, remote control over vulnerable computers without any help from users. CVE-2020-0852 is one just four remote execution flaws Microsoft patched this month in versions of Word.

Security Boulevard
FEBRUARY 27, 2021
Our thanks to BSides Calgary and Conference Speakers for publishing their outstanding presentations; which originally appeared at the group's BSides Calgary 2020 Conference , and on the Organization's YouTube Channel.

SecureList
MARCH 31, 2021
2020 was challenging for everyone: companies, regulators, individuals. As a result, 2020 was extremely eventful in terms of digital threats, in particular those faced by financial institutions. In 2020, the group tried its hand at the big extortion game with the VHD ransomware family. Methodology. Methodology.

Troy Hunt
JUNE 9, 2021
I've had a couple of cases to date where email addresses compromised by malware then discovered in the course of investigations have been provided to Have I Been Pwned (HIBP). NordLocker has written about the nameless malware that stole 1.2 For guidance on how protecting against malware, read NordLocker's report on the incident.
Security Affairs
FEBRUARY 24, 2020
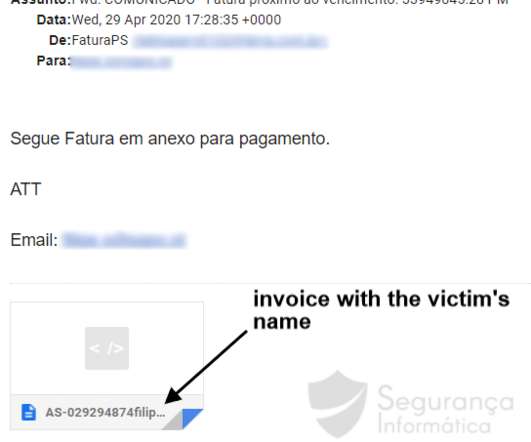
Since end-December 2019 lampion malware has been noted as the most prominent malware targeting Portuguese organizations. Figure 1: Lampion malware email templates. 2020-02-13] #Lampion v2 #portugal #malware #ATA 0998f6473004e0ba54ead5784ba62db8 h}//vrau-x.s3.us-east-2.amazonaws.[com/0.zip zip h//oiurx14x.s3.us-east-2.amazonaws.}com/P-14-7.dll
Security Affairs
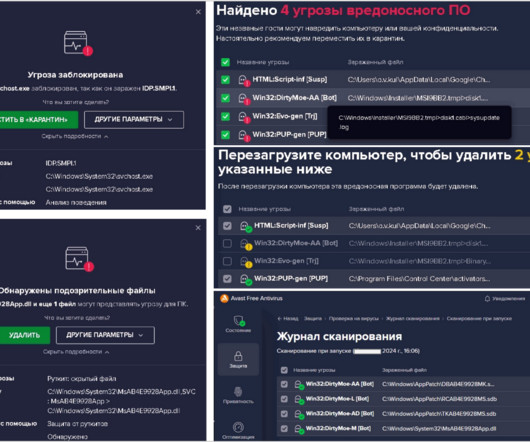
FEBRUARY 2, 2024
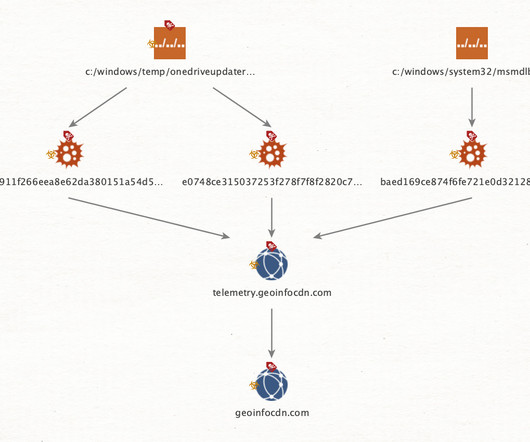
The Computer Emergency Response Team in Ukraine (CERT-UA) reported that a PurpleFox malware campaign had already infected at least 2,000 computers in the country. Experts defined DirtyMoe as a complex malware that has been designed as a modular system. ” reads the alert published by CERT-UA.

Krebs on Security
JANUARY 14, 2020
As first reported Monday by KrebsOnSecurity, Microsoft addressed a severe bug ( CVE-2020-0601 ) in Windows 10 and Windows Server 2016/19 reported by the NSA that allows an attacker to spoof the digital signature tied to a specific piece of software.
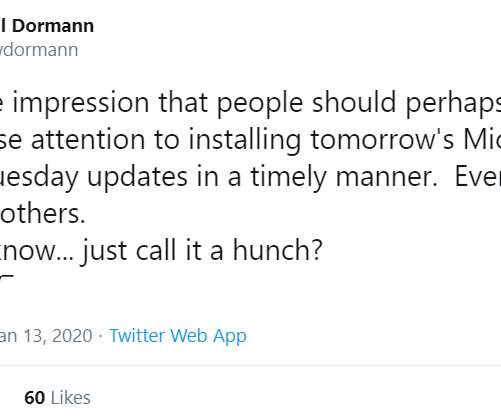
Krebs on Security
JANUARY 13, 2020
14, the first Patch Tuesday of 2020. Such a weakness could be exploited by attackers to make malware appear to be a benign program that was produced and signed by a legitimate software company. Those sources say Microsoft has quietly shipped a patch for the bug to branches of the U.S. Equally concerning, a flaw in crypt32.dll

CyberSecurity Insiders
FEBRUARY 23, 2022
A new malware developed by Sandworm hacking group has targeted appliances that are fire walled and reports are in that the military intelligence of the Russian Federation developed the malicious software. Now some statistic facts about malware. In the first half of 2020 alone, SonicWall registered over 3.2

SecureList
SEPTEMBER 13, 2021
The Incident response analyst report provides insights into incident investigation services conducted by Kaspersky in 2020. We deliver a range of services to help organizations when they are in need: incident response, digital forensics and malware analysis. Geography of incident responses by region, 2020.
Security Affairs
MAY 27, 2020
The updated Grandoreiro Malware equipped with latenbot-C2 features in Q2 2020 now extended to Portuguese banks. During April and May 2020, a new Grandoreiro variant was identified. This piece of malware includes improvements in the way it is operating. Figure 1: Grandoreiro email template Q2 2020 (Portugal).

Security Affairs
MARCH 15, 2020
In this post, I decided to share the details of the Coronavirus-themed attacks launched from February 1 to March 15, 2020. February 1, 2020 – Crooks start exploiting Coronavirus as bait to spread malware. February 25, 2020 – South Korea suffers from the spread of people infected with Corona 19. ‘

Security Boulevard
NOVEMBER 7, 2022
What’s the best way for a company to test its malware defenses in real-life scenarios? In fact, a 2017 report predicted that by 2020 businesses will be hit by a threat actor every eleven seconds. The post Safely Test Your Malware, Ransomware and Virus Defenses appeared first on Security Boulevard.
SecureList
FEBRUARY 15, 2021
In 2020: The share of spam in email traffic amounted to 50.37%, down by 6.14 Agentb malware family. In 2020, Bitcoin blackmailers stuck to their old scheme, demanding that their victims transfer money to a certain account and threatening adversity for failure to meet their demands. Figures of the year. Statistics: spam.

SecureList
AUGUST 23, 2021
billion USD in 2021, which is slightly less than the total revenue in 2020 but still significantly above the pre-pandemic figures. We examined malware and unwanted software disguised as popular PC and mobile games. We also looked in greater detail at some of the strains of malware being distributed and the dangers they pose for users.

Security Boulevard
JANUARY 11, 2022
Cloud-delivered malware is now more prevalent than web-delivered malware. In 2021, malware downloads originating from cloud apps increased to 66% of all malware downloads when compared to traditional websites, up from 46% at the beginning of 2020.

Security Boulevard
FEBRUARY 24, 2021
Our thanks to BSides Calgary and Conference Speakers for publishing their outstanding presentations; which originally appeared at the group's BSides Calgary 2020 Conference , and on the Organization's YouTube Channel.
Security Affairs
MAY 31, 2022
SideWinder, an aggressive APT group, is believed to have carried out over 1,000 attacks since April 2020, Kaspersky reported. The group stands out for the high frequency and persistence of its attacks, researchers believe that the APT group has carried out over 1,000 attacks since April 2020. ” states Kaspersky.

Hot for Security
APRIL 5, 2021
Bitdefender this week has published its annual Consumer Threat Landscape Report for 2020 underscoring some of the most prevalent cyber threats targeting regular users today. A key stat: cybercrime in 2020 was marked by a visible and aggressive targeting of the human layer. Android malware. Exploits and coin miners.

CyberSecurity Insiders
FEBRUARY 22, 2022
Trickbot Malware that started just as a banking malware has now emerged into a sophisticated data stealing tool capable of injecting malware like ransomware or serve as an Emotet downloader. Note- In September 2020, many of the hospitals and healthcare firms operating in United States were infected by RYUK ransomware.
Security Affairs
OCTOBER 9, 2023
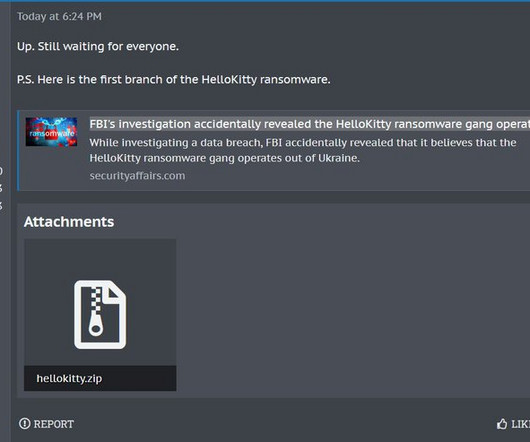
pic.twitter.com/YJavUu53v3 — vx-underground (@vxunderground) October 7, 2023 BleepingComputer was able to verify with the help of the popular malware researcher Michael Gillespie that that source code is legitimate and is related to the first version of the ransomware that was employed in 2020.
Security Affairs
DECEMBER 3, 2023
Threat actors are using the Agent Raccoon malware in attacks against organizations in the Middle East, Africa and the U.S. The malware was used in attacks against multiple industries, including education, real estate, retail, non-profit organizations, telecom companies, and governments.
Security Affairs
DECEMBER 27, 2023
Researchers discovered a new Android malware dubbed Xamalicious that can take full control of the device and perform fraudulent actions. The malware has been implemented with Xamarin, an open-source framework that allows building Android and iOS apps with.NET and C#. Google promptly removed the malware-laced apps from Google Play.

Security Affairs
FEBRUARY 24, 2020
FireEye’s report revealed that the incident response division Mandiant observed more than 500 new malware families in 2019. According to the FireEye Mandiant M-Trends 2020 report , FireEye analyzed 1.1 million malware samples per day in 2019 and identified 1,268 malware families. SecurityAffairs – hacking, malware).

Malwarebytes
FEBRUARY 16, 2021
In short, in 2020, cyberthreats evolved. Today, we are showing readers just what that evolution looked like, in our State of Malware 2021 report. This report provides our most comprehensive analysis of last year’s malware trends, with breakdowns by malware category, malware type, operating system, region, industry, and more.

Bleeping Computer
MAY 29, 2022
Kaspersky's quarterly report on mobile malware distribution records a downward trend that started at the end of 2020, detecting one-third of the malicious installations reported in Q1 2021, and about 85% of those counted in Q4 2021. [.].
Security Affairs
DECEMBER 1, 2020
The critical remote code execution (RCE) vulnerability CVE-2020-14882 in Oracle WebLogic is actively exploited by operators behind the DarkIRC botnet. Experts reported that the DarkIRC botnet is actively targeting thousands of exposed Oracle WebLogic servers in the attempt of exploiting the CVE-2020-14882. c25e6559668942[.]xyz.

Security Affairs
MARCH 29, 2020
In this post, I decided to share the details of the Coronavirus-themed attacks launched from March 22 to March 28, 2020. March 26 – WordPress WP-VCD malware delivered via pirated Coronavirus plugins. March 26 – Hackers hijack D-Link and Linksys routers to point users to COVID1 9 -themed sites serving malware.
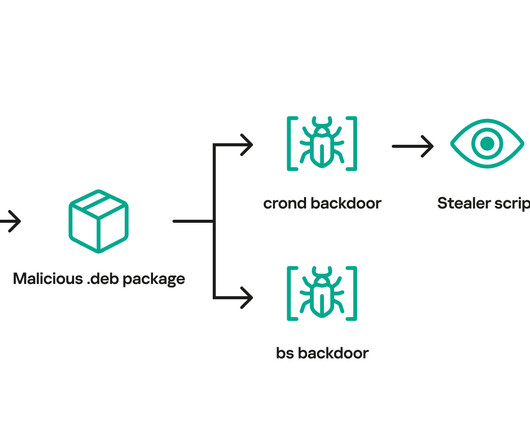
Security Affairs
SEPTEMBER 14, 2023
Researchers discovered a free download manager site that has been compromised to serve Linux malware to users for more than three years. Researchers from Kaspersky discovered a free download manager site that has been compromised to serve Linux malware. org domain and they were not containing any malware. org subdomain. .”
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content